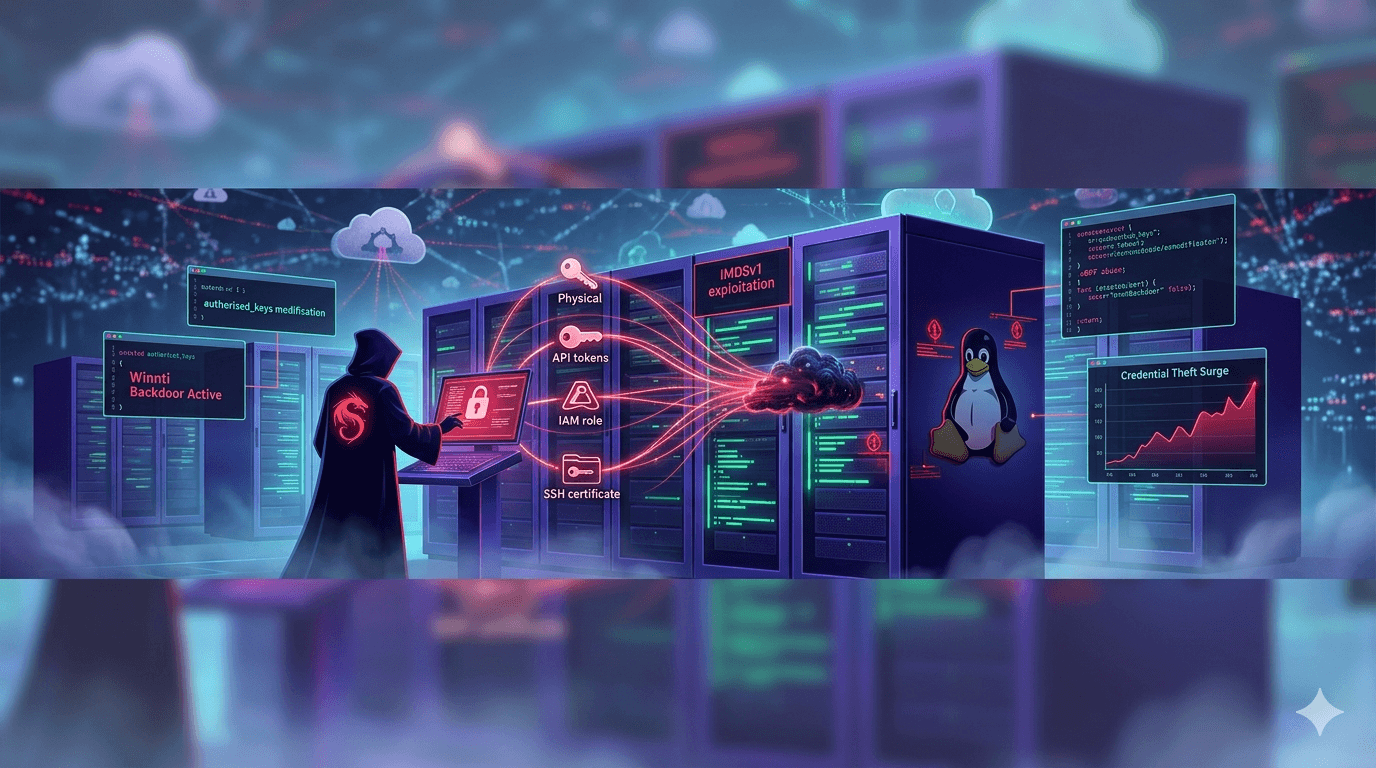
APT41 Cloud Server Attacks: Linux Credential Theft Surge
A Chinese state-sponsored threat actor just turned your Linux cloud servers into credential harvesting machines. In April 2026, APT41 deployed Winnti, a sophisticated backdoor targeting Linux cloud environments. This marks a significant escalation as attackers pivot from Windows to Linux workloads, exploiting the growing dominance of cloud-native infrastructure. Recent data shows 68% of organizations now run critical workloads on Linux servers (Cloud Security Alliance, 2025), making this attack vector particularly alarming.
This blog breaks down how APT41 achieves persistent credential theft, the technical mechanics of Winnti, real-world impact scenarios, and immediate hardening steps you can implement today. You'll learn to detect these stealthy implants, understand their MITRE ATT&CK mappings, and build resilient cloud server defenses. With cloud breaches costing organizations $4.45 million on average (IBM Cost of a Data Breach Report, 2025), understanding APT41's latest tactics isn't optional—it's essential for survival in today's threat landscape.
Understanding APT41's Linux Pivot Strategy
APT41 represents a dangerous evolution in state-sponsored cyber operations. Traditionally focused on Windows environments, they've now mastered Linux cloud server exploitation, targeting high-value credentials in AWS, Azure, and GCP environments.
Why Linux Cloud Servers Became Prime Targets
Attackers favor Linux cloud instances for several strategic reasons:
- Credential concentration: Service account tokens, SSH keys, and API credentials reside in well-known locations
- Horizontal scaling: Compromise one instance, pivot to entire cloud fleet via IAM roles
- Ephemeral nature: Auto-scaling groups make traditional endpoint detection ineffective
- Trusted execution: Cloud metadata services provide legitimate access to sensitive resources
Pro Tip: 73% of cloud breaches begin with compromised service credentials (Palo Alto Networks Unit 42, 2025).
Winnti's Core Capabilities on Linux
The Winnti backdoor demonstrates sophisticated Linux-specific adaptations:
- Process hollowing adapted for ELF binaries using
ptrace()system calls - Kernel module hiding via eBPF (extended Berkeley Packet Filter) abuse
- Memory-only execution avoiding filesystem artifacts entirely
- Container breakout capabilities targeting Docker and Kubernetes runtimes
This implant maintains persistence across container restarts and cloud instance scaling events.
Attack Chain Mapping to MITRE ATT&CK
| Tactic | Technique | Winnti Implementation |
|---|---|---|
| TA0001 Initial Access | T1190 Exploit Public-Facing Application | Cloud management console phishing |
| TA0003 Persistence | T1543.003 Create or Modify System Process | Modified sshd config + cron jobs |
| TA0005 Defense Evasion | T1564.004 Hidden Rootkit | eBPF rootkit hiding network connections |
| TA0006 Credential Access | T1552.007 Unsecured Credentials: Cloud Instance Metadata | AWS IMDSv1 exploitation |
| TA0011 Discovery | T1082 System Information Discovery | dmidecode, lscpu for fingerprinting |
Technical Breakdown: How Winnti Steals Credentials
Winnti's credential theft focuses on three high-value targets: cloud metadata services, SSH infrastructure, and service account tokens.
Cloud Metadata Service Exploitation
Important: IMDSv1 remains vulnerable in 42% of AWS environments despite warnings (Trend Micro, 2025).
Attackers query instance metadata endpoints:
curl "http://169.254.169.254/latest/meta-data/iam/security-credentials/"
Stolen artifacts include:
- Temporary AWS STS tokens with attached IAM roles
- Azure MSI (Managed Service Identity) tokens
- GCP service account JSON keys
SSH Key Harvesting and Persistence
Winnti targets SSH infrastructure systematically:
- Enumerates
~/.ssh/authorized_keysacross all users - Exfiltrates private keys from
/root/.ssh/id_rsa - Modifies SSH daemon configuration for persistence
- Creates hidden backdoor user accounts
Detection signature: Look for AuthorizedKeysCommand or AuthorizedKeysFile modifications in /etc/ssh/sshd_config.
Service Token Theft from Runtime Environments
Modern applications store credentials in environment variables and files:
# Common locations Winnti targets:
/var/run/secrets/kubernetes.io/serviceaccount/token
/opt/app/.env
/etc/secrets/*
Real-world scenario: A fintech firm lost $8.2M after Winnti stole Kubernetes service account tokens, enabling lateral movement to production databases.
Real-World Impact and Case Studies
The consequences of Winnti infections extend far beyond credential theft.
Financial Services Compromise Scenario
Consider a regional bank running containerized microservices:
Attack Timeline:
Day 1: Phishing gains initial API gateway access
Day 3: Winnti deployed to 17 Kubernetes worker nodes
Day 7: Service account tokens exfiltrated
Day 14: $12M fraudulent wire transfer executed
Day 21: Breach discovered during compliance audit
Damage assessment:
- Immediate: Stolen customer PII (PCI DSS violation)
- Strategic: Compromised transaction processing infrastructure
- Reputational: 18-month remediation costing $3.4M
Manufacturing IoT Supply Chain Attack
Winnti also targets operational technology environments:
- Entry vector: Compromised CI/CD pipeline injecting implant into container images
- Persistence: Modified container runtime hooks
- Impact: Stolen PLC credentials enabling production line manipulation
Table: Industry-Specific Winnti Impact
| Industry | Primary Target | Average Dwell Time | Financial Impact |
|---|---|---|---|
| Finance | Payment APIs | 14 days | $4.2M |
| Healthcare | EMR systems | 21 days | $2.8M + HIPAA fines |
| Manufacturing | SCADA/ICS | 28 days | $6.1M production loss |
| Government | Classified networks | 35+ days | Classified |
Detection and Response Strategies
You cannot patch your way out of APT41's Linux cloud server attacks alone. Detection requires behavioral analysis and cloud-native security controls.
Advanced Detection Techniques
Layered detection approach:
- eBPF monitoring: Track unauthorized eBPF programs loading
- File integrity: Monitor
/etc/ssh/sshd_config,/root/.ssh/* - Network behavior: Alert on metadata service queries from unexpected processes
- Container security: Runtime protection scanning for process hollowing
Pro Tip: Implement Falco rules specifically targeting ptrace() abuse by non-standard processes.
Cloud-Native Hardening Framework
| Control Category | Implementation | Compliance Mapping |
|---|---|---|
| IMDSv2 | Require session tokens for metadata access | CIS AWS 1.19 |
| SSH Certificate Authority | Eliminate authorized_keys files entirely | NIST 800-53 SC-12 |
| Service Account Least Privilege | Scoped IAM roles, workload identity federation | CIS Kubernetes 5.1.1 |
| Runtime Protection | eBPF-based behavioral monitoring | MITRE DETECT framework |
Incident Response Playbook
When Winnti infection is suspected:
- Isolate: Quarantine affected cloud instances immediately
- Inventory: Enumerate all potentially compromised service accounts
- Rotate: Emergency credential rotation across affected IAM roles
- Forensics: Preserve memory dumps, container images, kernel modules
- Hunt: Network analysis for C2 communication patterns
Table: Winnti IOC Summary
| Indicator Type | Specific IOC | Confidence |
|---|---|---|
| YARA Rule | rule Winnti_Linux_eBPF { strings: $ebpf = { 8b 45 fc 48 89 c7 } } | High |
| Process | /tmp/.sshd, ld.so.preload modification | High |
| Network | Metadata service queries from bash, curl | Medium |
| File | Modified /etc/ssh/sshd_config timestamps | Medium |
Implementing Zero Trust for Linux Cloud Workloads
Traditional perimeter security fails against APT41's tactics. Zero Trust architecture provides defense-in-depth.
Identity-First Security Model
Replace static credentials with dynamic authentication:
# Before (vulnerable):
Private key files, static service accounts
# After (Zero Trust):
- SSH Certificate Authority
- Workload Identity Federation
- JWT token rotation every 15 minutes
Behavioral Analytics Implementation
Key metrics to monitor:
- Process lineage: Track parent-child relationships for
ptrace()events - File access patterns: Alert on
/proc,/sysenumeration by non-standard processes - Network anomalies: Metadata service queries outside expected application patterns
- Container drift: Runtime changes to container images and configs
Automation and Orchestration
Infrastructure as Code security:
# GitHub Actions example for secure deployments
- name: Scan container image
uses: aquasec/trivy-action@master
- name: Verify SSH certificates
run: ssh-keygen -lf /etc/ssh/ssh_host_*_key.pub
Key Takeaways
- Deploy IMDSv2 immediately across all cloud providers to block metadata service abuse
- Eliminate static SSH keys using certificate-based authentication
- Implement eBPF runtime monitoring to detect process hollowing and rootkit activity
- Rotate service account credentials weekly using automation
- Hunt for Winnti using YARA signatures and behavioral analytics today
- Test your incident response against APT41's specific TTPs quarterly
Conclusion
APT41's Winnti backdoor represents a maturing threat against Linux cloud infrastructure. Attackers now possess the technical sophistication to target containerized workloads, service account tokens, and cloud metadata services with surgical precision. The financial and operational consequences of delayed detection prove catastrophic.
You face a clear choice: continue operating with vulnerable credential patterns, or implement the Zero Trust controls outlined above. Start with IMDSv2 enforcement and SSH certificate authority deployment—they deliver immediate risk reduction. Schedule comprehensive cloud workload security assessments within the next 30 days.
The clock is ticking. APT41 doesn't pause for compliance audits or quarterly reviews. Your Linux cloud servers represent mission-critical infrastructure. Secure them accordingly, or prepare for the inevitable consequences.
Frequently Asked Questions
Q: How do I verify if my cloud instances use IMDSv1 or IMDSv2?
A: For AWS, run curl -H "X-aws-ec2-metadata-token: $(curl -X PUT "http://169.254.169.254/latest/api/token" -H "X-aws-ec2-metadata-token-ttl-seconds: 21600")" http://169.254.169.254/latest/meta-data/. If it fails immediately, you're using IMDSv2. Success indicates IMDSv1—upgrade immediately.
Q: What makes Winnti different from typical Linux malware?
A: Winnti specifically targets cloud-native credential stores and uses eBPF for stealthy persistence. Most commodity malware focuses on cryptomining or basic C2. Winnti's credential theft enables strategic cloud account compromise across entire environments.
Q: Can container security tools detect Winnti infections?
A: Basic scanners miss Winnti due to memory-only execution. Deploy runtime protection with eBPF capabilities and behavioral analytics. Look specifically for ptrace() abuse and metadata service queries from unexpected processes.
Q: How long does credential rotation take after Winnti detection?
A: Complete rotation across affected IAM roles, service accounts, and SSH keys typically requires 4-8 hours with proper automation. Manual processes extend this to 2-3 days. Maintain pre-built rotation playbooks for rapid response.
Q: Is Winnti exclusively targeting specific industries?
A: No. APT41 targets financial services for immediate monetary gain but also hits manufacturing, healthcare, and government for espionage. Any organization running Linux cloud workloads with service account credentials represents a viable target.
Enjoyed this article?
Subscribe for more cybersecurity insights.
