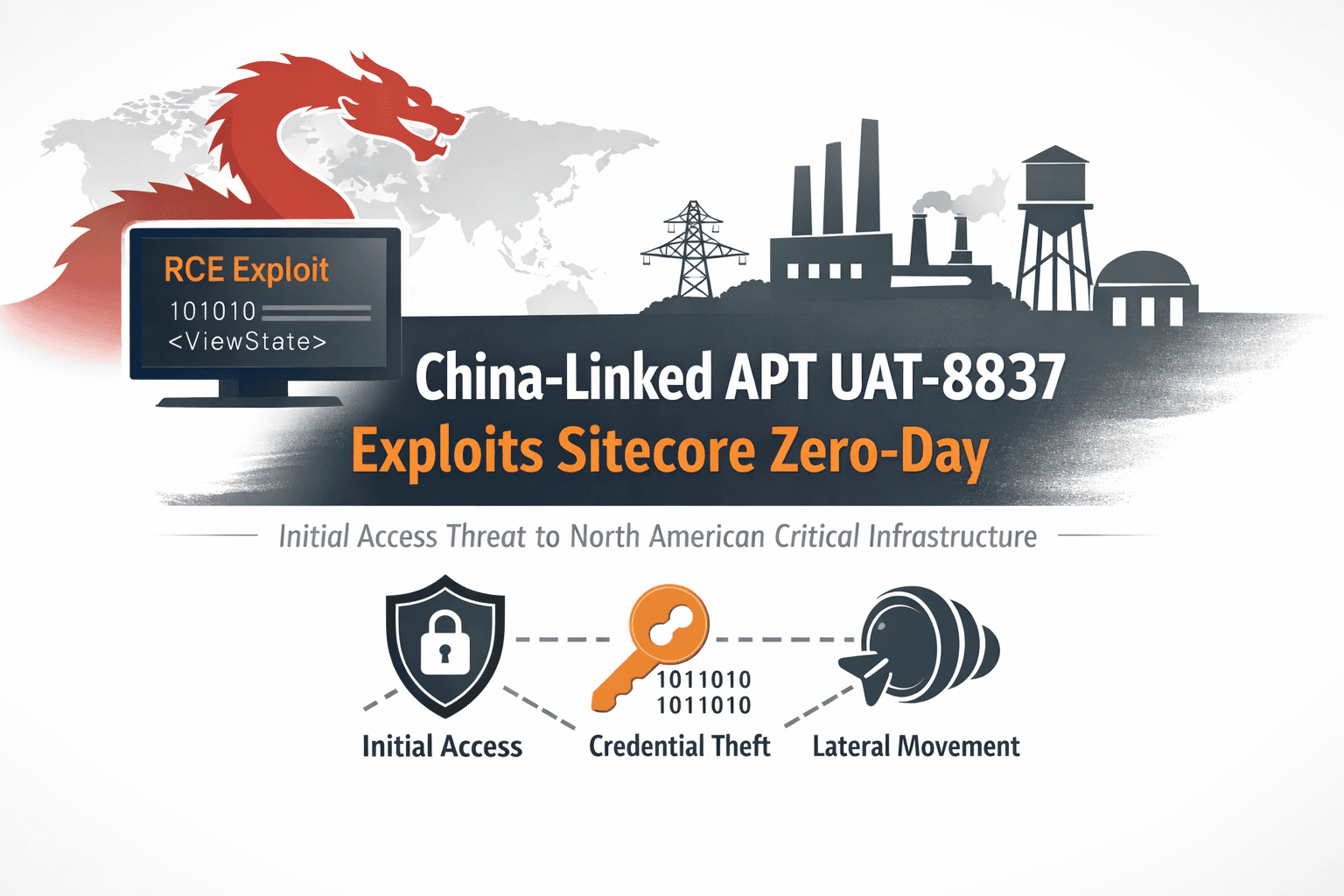
A newly identified advanced persistent threat (APT) group designated UAT-8837 has emerged as a sophisticated initial access specialist targeting organizations within North American critical infrastructure sectors.. Security researchers at Cisco Talos assess with medium confidence that the group operates with backing from Chinese state interests, having maintained active operations since at least early 2025.
What distinguishes UAT-8837 from other threat actors is their demonstrated capability to weaponize both known vulnerabilities and zero-day exploits against high-value targets. The group's recent exploitation of CVE-2025-53690, a critical Sitecore CMS vulnerability, exemplifies how rapidly modern APTs can incorporate fresh attack vectors into their arsenal. This analysis examines UAT-8837's tactics, the Sitecore vulnerability they leveraged, and the defensive measures organizations must implement to protect critical infrastructure from this evolving threat.
Understanding UAT-8837's Role as an Initial Access Broker
UAT-8837 functions as a specialized initial access operator within a larger ecosystem of China-nexus threat actors. Their primary mission involves breaching high-value networks and establishing footholds that enable follow-on operations by other groups.
The Initial Access Specialization Model
Traditional APT campaigns often involve a single group executing all phases of an attack. UAT-8837 represents a more sophisticated division of labor where specialized teams focus on specific operational phases:
- Breaking through perimeter defenses using compromised credentials or vulnerability exploitation
- Establishing persistence mechanisms that survive detection attempts
- Conducting reconnaissance to map network topology and identify valuable assets
- Preparing infrastructure for handoff to espionage or data exfiltration teams
- Maintaining access while avoiding attribution to follow-on operators
This specialization allows threat actors to develop deep expertise in initial compromise techniques while minimizing their exposure during later, more visible attack phases.
Attribution and Threat Landscape Context
Cisco Talos connects UAT-8837 to Chinese state interests through several indicators. The group targets critical infrastructure sectors aligned with Chinese strategic priorities. Their tactics overlap with known China-nexus clusters including RedLeaves and ShadowPad malware families. Operational timing and infrastructure patterns suggest coordination with groups like UAT-7290, active since 2022 in similar targeting profiles.
Table: China-Nexus APT Ecosystem
| Group | Active Since | Primary Role | Notable Tools |
|---|---|---|---|
| UAT-8837 | 2025 | Initial access specialist | WeepSteel, GoTokenTheft, Earthworm |
| UAT-7290 | 2022 | Access + espionage + infrastructure | RedLeaves, ShadowPad variants |
| Related clusters | 2018+ | Various specialized operations | Custom malware families |
CVE-2025-53690: The Sitecore ViewState Vulnerability
The exploitation of CVE-2025-53690 demonstrates UAT-8837's capability to rapidly weaponize newly disclosed vulnerabilities. This critical flaw in Sitecore CMS products enables remote code execution through malicious ViewState deserialization.
Technical Details of the Vulnerability
ViewState deserialization vulnerabilities occur when web applications fail to properly validate serialized state data sent by clients. Attackers craft malicious ViewState payloads that execute arbitrary code when the server deserializes them.
In Sitecore's case, the vulnerability affects internet-facing instances that accept ViewState data without sufficient integrity checks. Successful exploitation grants attackers the ability to execute commands with the privileges of the web application, typically allowing:
- Installation of webshells for persistent access
- Deployment of reconnaissance tools like WeepSteel
- Lateral movement preparation through network mapping
- Credential harvesting from application memory
Exploitation Timeline and Response
Mandiant first observed active exploitation in early September 2025, when attackers deployed the WeepSteel reconnaissance backdoor through malicious ViewState payloads. The discovery revealed a zero-day vulnerability being actively exploited in the wild before patches existed.
Google Cloud and Mandiant coordinated to disrupt ongoing campaigns while working with Sitecore on remediation. Sitecore subsequently released patches, but the window between exploitation and patching allowed UAT-8837 and potentially other actors to compromise numerous vulnerable systems.
Important: Organizations running Sitecore CMS must verify they have applied the latest security updates. The brief window between zero-day exploitation and patch availability means many systems were compromised before defenders could respond.
Living Off the Land: UAT-8837's Operational Toolkit
UAT-8837 employs a sophisticated blend of legitimate Windows utilities and open-source offensive tools. This "living off the land" approach makes detection significantly more challenging because the tools themselves appear legitimate.
Credential Access and Privilege Escalation Tools
The group leverages specialized utilities for extracting and abusing credentials:
GoTokenTheft enables stealing authentication tokens from running processes, allowing attackers to impersonate legitimate users without knowing their passwords. Rubeus provides comprehensive Kerberos abuse capabilities including ticket extraction, manipulation, and pass-the-ticket attacks. Certipy exploits Active Directory Certificate Services misconfigurations to obtain certificates for authentication bypass and privilege escalation.
These tools work in concert to establish multiple authentication pathways, ensuring access persists even if individual credentials are reset.
Reconnaissance and Discovery Operations
UAT-8837 conducts thorough reconnaissance focusing on Active Directory architecture:
- SharpHound automates BloodHound data collection, mapping trust relationships and attack paths
- setspn, dsquery, and dsget enumerate service principal names and domain objects using native Windows commands
- Manual commands map network topology, identify security policies, and locate high-value targets
- Focus on domain trust relationships reveals paths for moving between network segments
The emphasis on AD topology indicates planning for long-term persistence rather than quick data theft.
Remote Execution and Lateral Movement
Once credentials are harvested, UAT-8837 deploys multiple tools for executing commands on remote systems:
Table: Remote Execution Tools
| Tool | Protocol/Method | Detection Difficulty | Primary Use |
|---|---|---|---|
| Impacket | SMB, WMI, RPC | Medium | General lateral movement |
| Invoke-WMIExec | WMI | High | PowerShell-based execution |
| GoExec | Multiple | Medium | Cross-platform flexibility |
| SharpWMI | WMI | High | .NET-based stealth execution |
Tunneling and Remote Access Infrastructure
Earthworm creates reverse SOCKS tunnels that bypass egress filtering and allow external operators to interact with internal systems. DWAgent provides legitimate remote administration capabilities that blend with normal IT operations, serving both as a command channel and payload staging platform.
The rotation through tool variants helps evade signature-based detection while maintaining operational capability.
Critical Infrastructure Implications and Supply Chain Risks
UAT-8837's targeting of North American critical infrastructure raises significant national security concerns. The group's activities align with broader Chinese strategic objectives to map and potentially disrupt essential services.
Sector-Specific Targeting Patterns
Critical infrastructure encompasses multiple sectors that UAT-8837 appears to prioritize. Energy generation and distribution networks face particular risk due to their interconnected nature and aging security architectures. Water treatment facilities increasingly rely on internet-connected SCADA systems that may lack robust security controls. Transportation infrastructure including rail and aviation systems present attractive targets for intelligence collection.
The hands-on-keyboard approach UAT-8837 employs allows customized attacks tailored to each victim environment rather than automated mass exploitation.
The Supply Chain Trojanization Threat
Cisco Talos documented at least one instance where UAT-8837 exfiltrated a DLL file from a product deployed in the victim environment. This activity pattern suggests potential preparation for supply chain attacks.
By trojanizing legitimate software components, attackers could compromise downstream organizations that install updates or patches containing malicious code. This technique proved devastating in previous supply chain attacks and represents a force-multiplier for APT operations.
Organizations should implement integrity verification for all software updates and maintain detailed baselines of legitimate file hashes for critical applications.
Detection and Defense Strategies
Defending against sophisticated initial access operators requires layered security controls and proactive threat hunting. Organizations cannot rely solely on perimeter defenses when adversaries leverage zero-day exploits and valid credentials.
Vulnerability Management and Patch Prioritization
The rapid weaponization of CVE-2025-53690 demonstrates why internet-facing systems require accelerated patching cycles:
- Maintain inventory of all external-facing web applications and CMS platforms
- Subscribe to vendor security advisories for early warning of critical vulnerabilities
- Implement emergency patching procedures that can deploy fixes within 24-48 hours
- Consider web application firewalls (WAFs) as temporary mitigation during patch deployment
- Conduct regular vulnerability scans focusing on known APT-exploited CVEs
Pro Tip: Prioritize patching based on active exploitation evidence rather than just CVSS scores. A medium-severity vulnerability being actively exploited poses greater risk than a theoretical critical flaw.
Active Directory Hardening
Since UAT-8837 focuses heavily on AD reconnaissance, hardening domain infrastructure disrupts their operational playbook:
Table: Active Directory Security Controls
| Control | Purpose | Implementation Complexity |
|---|---|---|
| Credential Guard | Prevent credential theft | Medium |
| LAPS | Rotate local admin passwords | Low |
| Tiered admin model | Limit privilege escalation | High |
| ADCS hardening | Prevent certificate abuse | Medium |
| SPN monitoring | Detect Kerberoasting | Low |
Behavioral Detection and Hunting
Signature-based detection struggles against "living off the land" tactics. Security teams must hunt for suspicious behavior patterns:
Look for unusual combinations of native Windows commands executed in sequence, particularly those involving dsquery, setspn, and credential access tools. Monitor for WMI and SMB lateral movement patterns that deviate from normal administrative activity. Track PowerShell execution with suspicious parameters or obfuscation. Alert on reverse tunneling tools like Earthworm or unusual SOCKS proxy activity.
Implementing MITRE ATT&CK-based detection rules helps identify TTPs associated with UAT-8837 and similar threat actors.
Network Segmentation and Zero Trust
Assuming breach and limiting lateral movement reduces the impact when initial access occurs:
- Segment critical infrastructure networks from corporate IT environments
- Implement micro-segmentation for high-value assets
- Require multi-factor authentication for all administrative access
- Deploy inline network analysis to detect east-west malicious traffic
- Monitor and restrict outbound connections to prevent data exfiltration
Key Takeaways
- UAT-8837 operates as a specialized initial access broker preparing critical infrastructure networks for follow-on espionage and disruption operations by other China-nexus threat actors
- The group demonstrates rapid zero-day weaponization capability, exploiting CVE-2025-53690 in Sitecore CMS within the same timeframe as its public disclosure
- "Living off the land" tactics using legitimate Windows utilities and open-source tools make detection significantly more challenging than traditional malware-based attacks
- Focus on Active Directory reconnaissance and credential theft indicates planning for long-term persistence rather than opportunistic data theft
- Evidence of DLL exfiltration raises serious concerns about potential supply chain trojanization targeting downstream organizations that rely on compromised software
- Effective defense requires layered controls including accelerated patching, AD hardening, behavioral detection, and network segmentation rather than relying solely on perimeter security
Conclusion
UAT-8837 represents the evolution of state-sponsored cyber operations toward specialized roles and division of labor. Their effectiveness as initial access specialists stems from combining zero-day exploitation capability with sophisticated post-compromise techniques that abuse legitimate system administration tools.
The targeting of North American critical infrastructure carries implications beyond traditional espionage. Understanding the group's tactics and implementing comprehensive defense strategies helps organizations protect essential services from compromise. Security teams must assume that determined APT actors will eventually breach perimeter defenses and focus equally on detecting and limiting post-compromise activities.
Organizations operating critical infrastructure should conduct threat hunts specifically looking for UAT-8837 indicators of compromise released by Cisco Talos. Implement the defensive controls outlined in this analysis, with particular emphasis on rapid vulnerability patching, Active Directory security, and behavioral detection capabilities that can identify "living off the land" techniques regardless of the specific tools employed.
Frequently Asked Questions
Q: How does UAT-8837 differ from other China-nexus APT groups?
A: UAT-8837 specializes exclusively in initial access operations, focusing on breaking into networks and establishing footholds for handoff to other threat actors. Unlike full-spectrum APT groups that conduct entire campaigns themselves, UAT-8837's specialized role allows them to develop deep expertise in compromise techniques while other groups handle espionage and data exfiltration phases.
Q: What makes CVE-2025-53690 particularly dangerous for organizations running Sitecore?
A: The vulnerability allows remote code execution without authentication on internet-facing Sitecore instances, and it was actively exploited as a zero-day before patches became available. The ViewState deserialization flaw gives attackers immediate access to deploy backdoors, making it a critical risk for any organization with exposed Sitecore CMS systems that haven't applied the latest security updates.
Q: Why do APT groups prefer "living off the land" techniques over custom malware?
A: Legitimate system administration tools and native Windows utilities don't trigger antivirus signatures and appear normal in many security monitoring systems. This approach makes detection significantly harder because security teams must identify malicious behavior patterns rather than recognizing known malware signatures, and it allows attackers to maintain access even in heavily monitored environments.
Q: How can organizations detect UAT-8837 activity if they use legitimate tools?
A: Detection requires behavioral analysis rather than signature-based approaches. Look for unusual sequences of reconnaissance commands, abnormal credential access patterns, WMI-based lateral movement outside normal administrative hours, and reverse tunneling tools like Earthworm. Implementing MITRE ATT&CK-based detections and conducting regular threat hunts using the IOCs released by Cisco Talos provides the best chance of identifying compromise.
Q: What should organizations do if they suspect UAT-8837 compromise?
A: Immediately isolate affected systems to prevent lateral movement while preserving forensic evidence. Engage incident response capabilities to hunt for additional indicators across the environment, particularly focusing on Active Directory compromise and credential theft. Reset all privileged account credentials, review domain trust relationships, and search for persistence mechanisms like scheduled tasks or registry modifications. Consider bringing in external threat intelligence and forensics support given the sophistication of state-sponsored APT operations.
Enjoyed this article?
Subscribe for more cybersecurity insights.
