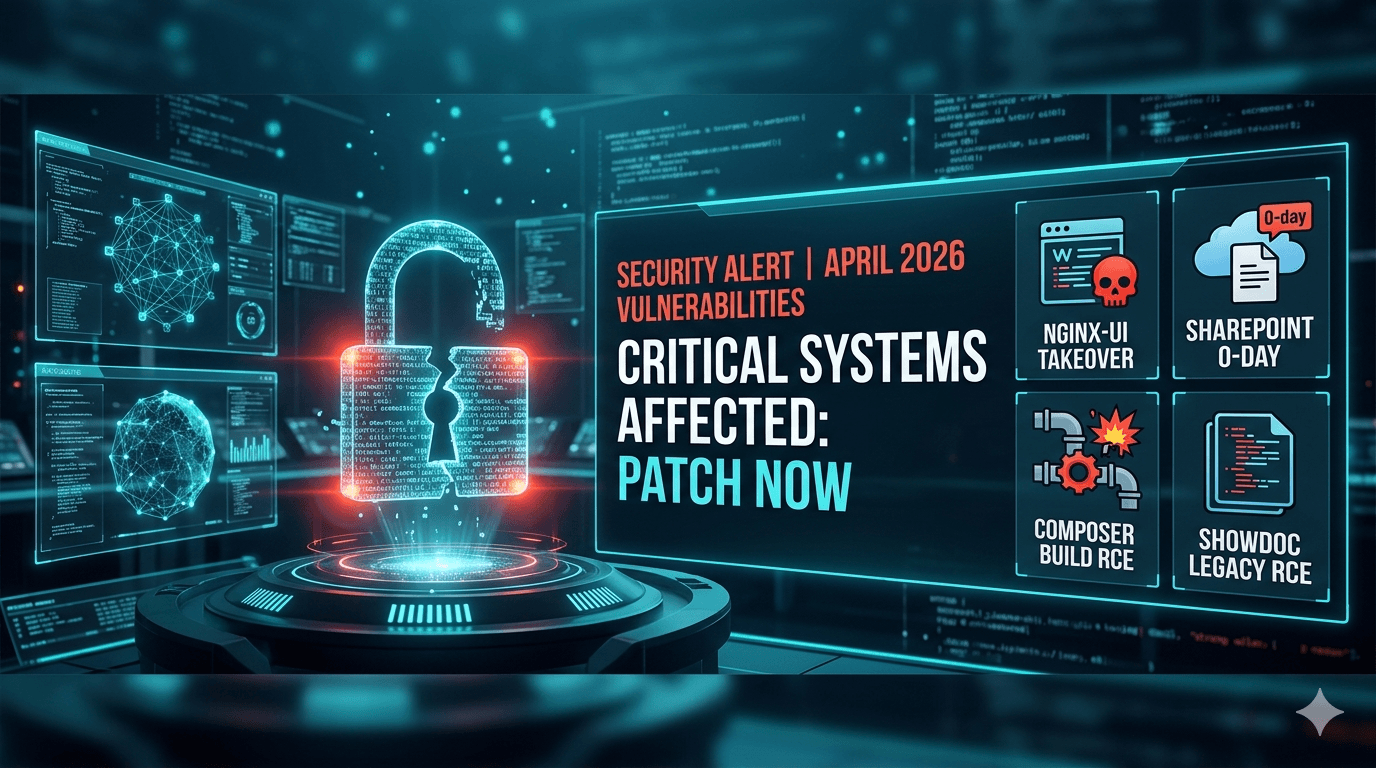
Critical April 2026 Vulnerabilities You Must Patch Now
Every major breach starts with a missed patch. In the first quarter of 2026 alone, unpatched software vulnerabilities accounted for a staggering 62% of initial access vectors in enterprise ransomware incidents (Cybersecurity Ventures, 2025). Now, a fresh wave of critical April 2026 vulnerabilities threatens to cripple organizational infrastructure globally. From web panels to core collaboration tools, attackers are weaponizing new exploits faster than most IT teams can deploy software updates.
Are you confident your external attack surface is entirely secure today? This month brings high-impact flaws across popular enterprise platforms, and threat actors are already actively exploiting several of them. A highly destructive zero-day in Microsoft SharePoint Server currently compromises on-premises environments, while a critical remote code execution flaw in nginx-ui hands attackers complete server control. Simultaneously, software developer pipelines face severe command execution risks through newly disclosed PHP Composer flaws.
This post breaks down exactly how these newly disclosed threats operate. You will learn the hidden mechanics behind these attacks, discover how cybercriminals weaponize them against businesses, and gain actionable mitigation strategies to secure your critical infrastructure immediately.
Active Exploitation in nginx-ui and Server Risks
Web-based management panels offer tremendous administrative convenience, but they also create massive security bottlenecks. The nginx-ui platform, specifically designed to simplify Nginx server configuration, is currently the primary target of a severe remote code execution attack campaign.
The Mechanics of CVE-2026-33032
Security researchers recently identified CVE-2026-33032, a critical vulnerability residing deep within the nginx-ui application interface. This specific flaw allows unauthorized threat actors to execute arbitrary commands directly on the underlying host operating system. Because administrators typically deploy nginx-ui on internet-facing reverse proxies and external API gateways, the global exposure footprint is massive.
Attackers actively exploit weak authentication mechanisms to push malicious configurations directly through the application's API. Once authenticated, they easily bypass standard security controls to achieve full root access on the host server.
Real-World Server Takeover Scenarios
How does an nginx-ui compromise look in practice? Attackers do not just deface public websites; they fundamentally alter your network traffic flow. In a recently anonymized enterprise incident, threat actors modified Nginx virtual host configurations to silently intercept customer payment credentials.
- They deployed hidden web shells in the webroot to maintain persistent remote access.
- Attackers injected malicious cryptocurrency miners into the underlying operating system.
- Threat actors manipulated server blocks to redirect legitimate API traffic to external domains.
- They established lateral movement pathways to penetrate deeper internal enterprise networks.
Table: Nginx-ui Threat and Impact Analysis
| Attack Vector | Immediate Impact | Long-Term Consequence |
|---|---|---|
| API Command Injection | Arbitrary code execution | Complete server takeover and data theft |
| Virtual Host Modification | Traffic redirection | Severe reputation damage and credential loss |
| Web Shell Deployment | Persistent backdoor access | Ransomware deployment and lateral movement |
Microsoft SharePoint Zero-Day Threat Landscape
On-premises enterprise collaboration tools remain highly lucrative targets for advanced persistent threat groups. A devastating new zero-day vulnerability in Microsoft SharePoint Server is actively disrupting enterprise environments before security teams can apply proper network defenses.
Why Attackers Target Collaboration Platforms
SharePoint acts as the central nervous system for organizational data. It securely holds sensitive internal documents, proprietary intellectual property, and critical business workflows. Is your company extranet inadvertently exposing this confidential data?
Attackers specifically target internet-exposed SharePoint deployments because they provide a highly credible staging ground for deeper intrusions. A compromised SharePoint server allows threat actors to distribute internal phishing lures that bypass traditional email security gateways completely. They leverage the platform's trusted internal status to move laterally into connected SQL databases and critical Active Directory environments.
Mitigating the SharePoint Zero-Day Exposure
Defending against a live zero-day attack requires immediate, decisive action from your security operations center. Microsoft has officially acknowledged the active exploitation and released emergency mitigation guidance for all on-premises deployments. You must isolate vulnerable instances immediately to prevent unauthorized remote code execution.
- Apply the specific April Microsoft security patches immediately to all affected SharePoint builds.
- Restrict direct internet access to SharePoint servers using secure VPNs or zero-trust network access.
- Monitor application pool logs continuously for suspicious file uploads, specifically targeting unexpected .aspx files.
- Enforce stringent multi-factor authentication requirements for all extranet and remote access portals.
Table: SharePoint Security Implementation Framework
| Security Control | Implementation Focus | Mitigation Value |
|---|---|---|
| Patch Management | Apply April 2026 emergency updates | Eliminates the core zero-day vulnerability |
| Network Isolation | Restrict internet-facing portals | Reduces external attack surface drastically |
| Behavioral Monitoring | Alert on abnormal file uploads | Detects post-exploitation web shell activity |
Developer Pipeline Threats: April 2026 Vulnerabilities in Composer
The enterprise software supply chain remains dangerously fragile. Two critical April 2026 vulnerabilities in PHP Composer currently threaten developer pipelines by enabling stealthy remote command execution during routine automated software build processes.
Understanding CVE-2026-40176 and CVE-2026-40261
These dual vulnerabilities highlight the hidden systemic risks within automated package dependency resolution. CVE-2026-40176 introduces severe command injection capabilities via malicious Perforce repository configurations. Similarly, CVE-2026-40261 allows remote attackers to inject dangerous shell metacharacters through crafted source package references.
Even if your development organization does not actively use Perforce, Composer's internal processing logic allows exploitation when handling crafted repository configurations. Attackers successfully trick automated CI/CD pipelines into fetching malicious dependencies, executing arbitrary shell commands silently in the background of your build server.
Hardening Your CI/CD Pipelines
A single compromised build server can seamlessly infect dozens of downstream enterprise applications simultaneously. You must treat your development environments with the exact same security rigor and access control as your live production servers.
- Upgrade PHP Composer immediately to the latest patched version across all local and shared environments.
- Audit all
composer.jsonfiles rigorously for unauthorized or highly suspicious repository configurations. - Execute automated build processes strictly within isolated, ephemeral Docker container environments.
- Strip all unnecessary system-level privileges from the service accounts running your dependency management tools.
Table: April 2026 Vulnerabilities Patch Priority Matrix
| Vulnerability Target | Exploitation Status | Recommended Patch Priority |
|---|---|---|
| nginx-ui (Internet Facing) | Actively Exploited | Critical (Immediate action required) |
| Microsoft SharePoint | Active Zero-Day | Critical (Immediate action required) |
| PHP Composer | Proof of Concept Available | High (Patch within 48 hours) |
| ShowDoc Instances | Actively Exploited | High (Patch or isolate immediately) |
Legacy Vulnerabilities Resurfacing: ShowDoc RCE
Sophisticated threat actors do not just chase the newest zero-days; they actively hunt for forgotten perimeter infrastructure. The persistent, ongoing exploitation of unpatched ShowDoc servers proves that older vulnerabilities still provide highly reliable initial access vectors into corporate networks.
The Persistent Threat of CVE-2025-0520
ShowDoc, a widely adopted open-source tool for API documentation, suffers from a severe remote code execution flaw officially tracked as CVE-2025-0520. Despite security patches existing for months, attackers continue to exploit unpatched systems aggressively across the globe.
Threat actors utilize automated internet scanning tools to discover exposed ShowDoc administrative interfaces rapidly. Once located, they send specifically crafted network requests to achieve instant remote code execution, entirely bypassing all standard administrative authentication requirements.
Defending Unpatched Environments
If immediate patching is technically impossible due to legacy constraints, compensating network controls become your absolute only line of defense. You must proactively sever all external network access to these vulnerable API documentation portals today.
- Deploy the latest stable ShowDoc release to eliminate the underlying remote code execution flaw completely.
- Block all public internet access to ShowDoc administrative dashboards and backend API endpoints immediately.
- Route all legitimate internal documentation traffic exclusively through a secure, authenticated VPN tunnel.
- Continuously audit public web directories for hidden web shells or unauthorized PHP script deployments.
Key Takeaways
- Isolate vulnerable servers immediately to protect your network against actively exploited zero-day threats in Microsoft SharePoint.
- Audit internet-facing web panels like nginx-ui rigorously for unauthorized configuration changes and hidden persistent backdoors.
- Secure software supply chains by updating PHP Composer and running automated builds in isolated, highly restricted environments.
- Restrict administrative interfaces from public internet access to effectively block automated exploitation of older flaws like CVE-2025-0520.
- Prioritize patching schedules strictly based on active exploitation metrics rather than relying solely on base CVSS scores.
Conclusion
The modern cybersecurity threat landscape moves significantly faster than traditional enterprise patch management cycles allow. The critical April 2026 vulnerabilities discussed in this post demand immediate, decisive, and coordinated action from IT and security teams worldwide. From complete server takeovers via nginx-ui flaws to devastating zero-day exploits in Microsoft SharePoint, advanced attackers are heavily targeting the core infrastructure that keeps your business operational.
Relying exclusively on perimeter firewalls is no longer sufficient when threat actors successfully weaponize legitimate developer tools like PHP Composer against you. You must aggressively adopt a proactive security posture, combining rapid software patch deployment with strict network isolation and continuous behavioral monitoring. Do not wait for late-stage indicators of compromise to trigger your incident response plan.
Review your external internet attack surface right now, identify any exposed instances of these highly vulnerable platforms, and begin executing your emergency patching protocols today.
Frequently Asked Questions
Q: What specifically makes the April 2026 vulnerabilities in nginx-ui so dangerous? A: The CVE-2026-33032 vulnerability is highly dangerous because it provides remote attackers with direct code execution capabilities on the underlying host system. Since nginx-ui actively manages web traffic routing, attackers can easily intercept sensitive customer data, deploy ransomware payloads, or establish persistent backdoors across your entire web infrastructure.
Q: How do I definitively know if my SharePoint Server was compromised by the zero-day? A: You should aggressively review your SharePoint application pool logs and underlying IIS web logs for highly suspicious behavior. Look specifically for unexpected .aspx or .ps1 file uploads, unfamiliar internet user agents executing anomalous POST requests, and unauthorized administrative modifications to critical system configurations like the web.config file.
Q: Do the PHP Composer vulnerabilities actually affect me if my team does not use Perforce? A: Yes, your build pipeline remains vulnerable even if your organization does not actively use Perforce for version control. The vulnerabilities (CVE-2026-40176 and CVE-2026-40261) reside directly within how Composer processes configurations, allowing attackers to inject malicious code simply by tricking your automated pipeline into reading a crafted repository file.
Q: Why are threat actors still actively exploiting the older ShowDoc CVE-2025-0520 vulnerability? A: Threat actors frequently rely on fast, automated internet scanning scripts to uncover abandoned or forgotten web infrastructure. Many organizations deploy internal developer documentation tools like ShowDoc and simply fail to maintain them, creating an incredibly easy, reliable attack vector for cybercriminals seeking initial corporate network access.
Q: Which major security compliance frameworks mandate immediate patching for actively exploited flaws? A: Multiple stringent regulatory frameworks, including PCI DSS v4.0, SOC 2 Type II, and ISO 27001, strictly mandate rigorous vulnerability management protocols. Specifically, the CIS Controls (v8) demand that organizations remediate critical, actively exploited vulnerabilities rapidly to maintain ongoing compliance and successfully protect sensitive user data.
Enjoyed this article?
Subscribe for more cybersecurity insights.
