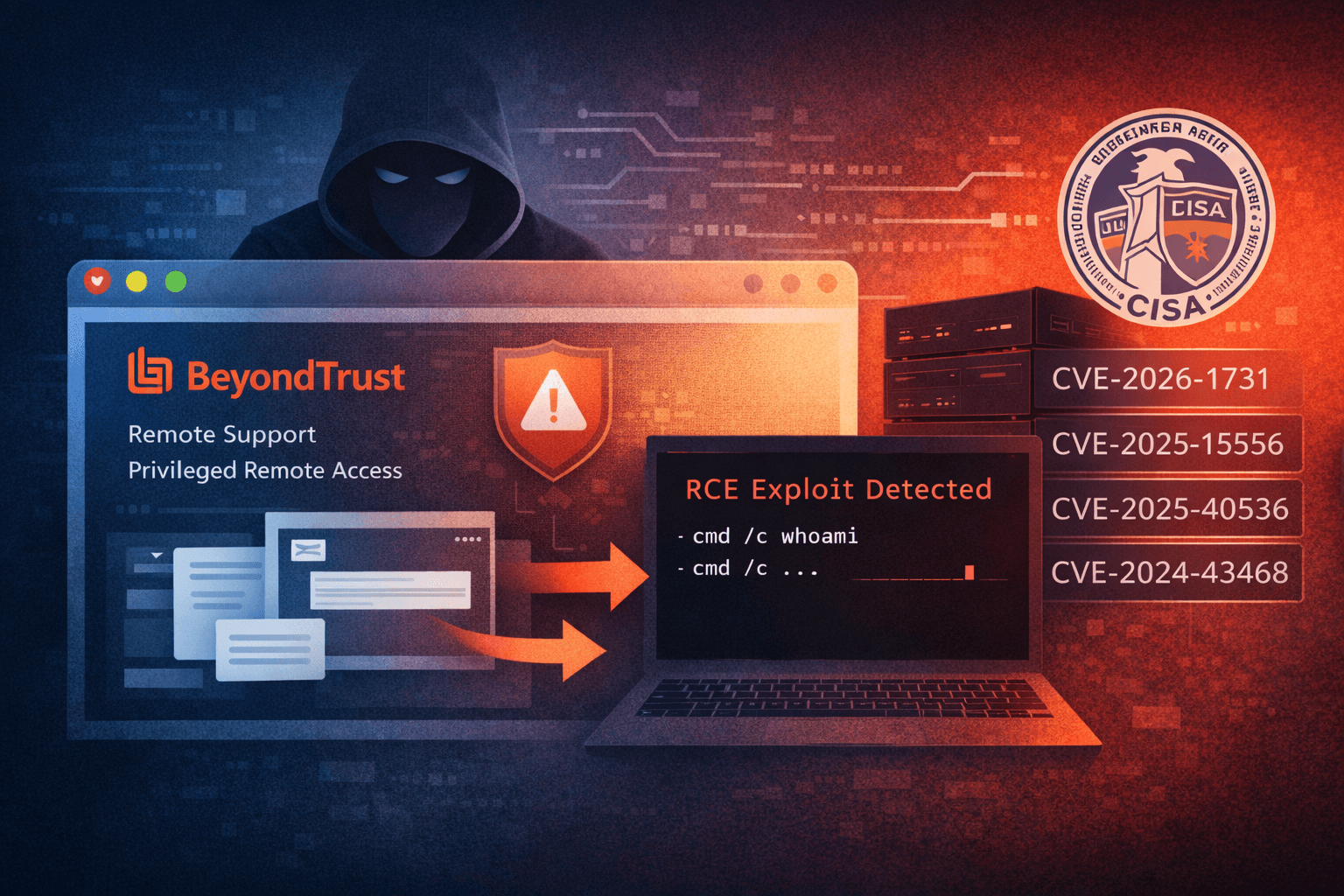
Threat actors are actively exploiting CVE-2026-1731, a critical remote code execution vulnerability in BeyondTrust's Remote Support and Privileged Remote Access platforms, with reconnaissance activity detected less than 24 hours after proof-of-concept code became public. This CVSS 9.9 pre-authentication flaw allows unauthenticated attackers to execute operating system commands as the site user, creating immediate risk for organizations running vulnerable versions. The rapid weaponization timeline underscores a troubling reality: the window between vulnerability disclosure and active exploitation continues to shrink.
Meanwhile, CISA has added four additional actively exploited vulnerabilities to its Known Exploited Vulnerabilities catalog, including a sophisticated supply-chain attack targeting Notepad++ users and critical flaws in Apple platforms, SolarWinds, and Microsoft Configuration Manager. Federal agencies face strict remediation deadlines, with patches required by February 15 for one vulnerability and March 5 for three others. This coordinated wave of exploitation demonstrates that adversaries are simultaneously weaponizing multiple attack vectors across enterprise infrastructure.
This article examines the technical details of the BeyondTrust vulnerability, analyzes the emerging threat landscape, and provides actionable guidance for prioritizing remediation efforts.
The BeyondTrust CVE-2026-1731 Vulnerability
Technical Overview and Attack Mechanics
CVE-2026-1731 affects BeyondTrust Remote Support versions 21.3 through 25.3.1 and Privileged Remote Access versions 22.1 through 24.x. The vulnerability enables unauthenticated remote code execution, allowing attackers to run arbitrary operating system commands with site user privileges without requiring valid credentials.
Researchers at watchTowr documented the attack workflow used in active exploitation campaigns. Attackers first abuse the get_portal_info functionality to extract the x-ns-company value from the target system. Using this extracted data, they establish a WebSocket channel that serves as the communication pathway for delivering and executing malicious commands.
The pre-authentication nature of this vulnerability makes it particularly dangerous. Traditional security controls that rely on authentication boundaries provide no protection against exploitation attempts. Once attackers identify vulnerable BeyondTrust instances exposed to the internet, they can achieve complete system compromise without needing to bypass authentication mechanisms or elevate privileges.
Exploitation Timeline and Threat Intelligence
The speed at which CVE-2026-1731 moved from disclosure to active exploitation illustrates the compressed timeline defenders now face. Security researchers observed reconnaissance activity beginning less than 24 hours after a proof-of-concept exploit became publicly available, demonstrating that threat actors maintain infrastructure ready to rapidly integrate new vulnerability checks.
GreyNoise and Defused Cyber detected scanning and exploitation attempts originating from multiple sources. Analysis revealed that 86% of observed reconnaissance activity originated from a single commercial VPN IP address in Frankfurt, suggesting an organized scanning operation rather than opportunistic individual attackers. This concentration of activity indicates that threat actors are systematically identifying vulnerable targets for immediate or future exploitation.
Table: CVE-2026-1731 Attack Progression
| Timeline Stage | Timeframe | Activity Observed |
|---|---|---|
| Vulnerability disclosure | Day 0 | BeyondTrust releases advisory and patches |
| PoC publication | Day 1 | Public exploit code becomes available |
| Initial reconnaissance | <24 hours after PoC | Automated scanning from VPN infrastructure |
| Active exploitation | Day 2-3 | watchTowr observes WebSocket-based attacks |
| Widespread scanning | Ongoing | 86% of traffic from single Frankfurt VPN node |
Patch Availability and Remediation
BeyondTrust has released patches addressing CVE-2026-1731 across affected product lines. Organizations must apply version-specific patches based on their current deployment.
Remote Support instances running versions 21.3 through 25.3.1 require patch BT26-02-RS. Privileged Remote Access versions 22.1 through 24.x need patch BT26-02-PRA. Organizations running PRA version 25.1 or later are not affected by this specific vulnerability and do not require patching for this issue.
Important: Given the active exploitation and the critical nature of remote access platforms, organizations should treat this as an emergency patch requiring deployment within 24-48 hours rather than following standard patch management timelines.
CISA KEV Catalog Additions
Four New Critical Vulnerabilities
CISA added four actively exploited vulnerabilities to its Known Exploited Vulnerabilities catalog, each representing distinct attack vectors that threat actors are successfully leveraging in real-world campaigns.
CVE-2026-20700 affects Apple platforms and involves a memory corruption vulnerability that security researchers believe may be used for spyware delivery. The specifics of exploitation remain limited, but the KEV designation confirms that threat actors are actively weaponizing this flaw against Apple users.
CVE-2025-15556 represents a supply-chain compromise in Notepad++, where attackers manipulated the update mechanism to deliver malware. CVE-2025-40536 enables control bypass in SolarWinds Web Help Desk, allowing unauthorized access to administrative functions. CVE-2024-43468 is an unauthenticated SQL injection vulnerability in Microsoft Configuration Manager that Microsoft patched in October 2024 but continues to see active exploitation.
The Notepad++ Supply-Chain Attack
The Notepad++ vulnerability reveals a sophisticated supply-chain attack orchestrated by Lotus Blossom, a China-linked advanced persistent threat group also tracked as Billbug and Bronze Elgin. Unlike traditional software compromises that modify source code, this campaign used trojanized installers and selectively diverted update traffic to specific high-value targets.
The attackers leveraged the WinGUp auto-update mechanism to deliver a new backdoor called Chrysalis. By targeting only strategically valuable victims rather than mass deployment, the campaign maintained a low detection profile while enabling long-duration espionage operations. This selective targeting approach reduces noise and extends the useful lifespan of the compromise before security researchers detect the malicious infrastructure.
DomainTools and LevelBlue SpiderLabs recommend three immediate actions:
- Upgrade to Notepad++ version 8.9.1 or later
- Consider disabling the WinGUp auto-updater in environments where manual updates are feasible
- Enforce network policies ensuring the updater communicates only with legitimate update servers
Table: CISA KEV Critical Vulnerabilities
| CVE ID | Affected Product | Vulnerability Type | Suspected Use Case | Federal Deadline |
|---|---|---|---|---|
| CVE-2026-20700 | Apple platforms | Memory corruption | Spyware delivery | March 5, 2026 |
| CVE-2025-15556 | Notepad++ | Supply-chain compromise | APT espionage (Lotus Blossom) | March 5, 2026 |
| CVE-2025-40536 | SolarWinds Web Help Desk | Access control bypass | Multi-stage intrusion | February 15, 2026 |
| CVE-2024-43468 | Microsoft Configuration Manager | Unauthenticated SQL injection | Unknown | March 5, 2026 |
SolarWinds and Microsoft Configuration Manager Risks
CVE-2025-40536 in SolarWinds Web Help Desk enables attackers to bypass access controls, granting unauthorized administrative capabilities. Recent threat intelligence reports indicate that attackers are using this vulnerability for multi-stage intrusions, establishing initial access before moving laterally to high-value assets within compromised environments.
The Microsoft Configuration Manager SQL injection vulnerability (CVE-2024-43468) presents particular concern because Microsoft patched it in October 2024, yet exploitation continues months later. This pattern suggests that organizations are failing to patch critical infrastructure components promptly, creating persistent exposure windows that threat actors actively exploit. The details of who is exploiting this vulnerability and for what purposes remain unclear, but the KEV designation confirms ongoing malicious activity.
Rapid Vulnerability Weaponization Trends
The Shrinking Patch Window
The CVE-2026-1731 case exemplifies how quickly threat actors now weaponize newly disclosed vulnerabilities. The sub-24-hour timeline from proof-of-concept release to observed reconnaissance represents a significant acceleration compared to historical exploitation patterns. This compression eliminates the traditional grace period defenders once had to test and deploy patches before facing active threats.
Several factors contribute to this acceleration. Automation enables threat actors to rapidly integrate new vulnerability checks into existing scanning infrastructure. Underground markets facilitate the sharing of exploit code among multiple threat groups simultaneously. Cloud-based attack infrastructure allows rapid scaling of scanning and exploitation attempts across internet-exposed attack surfaces.
Organizations can no longer rely on the assumption that they have days or weeks to patch critical vulnerabilities before exploitation begins. The weaponization timeline now measures in hours, fundamentally changing the risk calculus for vulnerability management programs.
Coordinated Multi-Vector Attacks
The simultaneous exploitation of vulnerabilities across remote access tools, supply-chain mechanisms, and enterprise management platforms suggests increasingly sophisticated threat actor operations. Rather than focusing on a single vulnerability or attack vector, adversaries are diversifying their approaches to maximize the probability of successful compromise.
This coordinated approach serves strategic purposes. If one exploitation attempt fails due to effective patching or detection, alternative vectors remain available. The variety of affected platforms ensures that most enterprise environments have exposure through at least one vulnerable system. By simultaneously pursuing multiple attack paths, threat actors increase their overall success rate while distributing defensive attention across multiple remediation efforts.
Prioritization and Remediation Strategies
Risk-Based Patching Approach
Not all vulnerabilities pose equal risk to every organization. Security teams must evaluate their specific exposure based on which affected products they deploy, whether those systems are internet-accessible, and what data or capabilities those systems protect.
Organizations running BeyondTrust Remote Support or Privileged Remote Access face immediate critical risk from CVE-2026-1731 and should prioritize emergency patching. Those using SolarWinds Web Help Desk must remediate CVE-2025-40536 by February 15 to meet federal deadlines. Microsoft Configuration Manager deployments require assessment and patching of CVE-2024-43468, particularly for internet-exposed instances.
The Notepad++ supply-chain compromise presents unique challenges because the affected application is often deployed broadly across workstations rather than managed as critical infrastructure. Organizations should inventory Notepad++ installations, verify versions, and deploy updates through enterprise software management tools.
Pro Tip: Create separate remediation tracks for internet-exposed systems versus internal infrastructure. Internet-facing vulnerable systems require immediate emergency patching regardless of standard change management processes, while internal systems can follow expedited but controlled deployment procedures.
Detection and Monitoring
Patching addresses future risk, but organizations must also assess whether exploitation occurred before patches were applied. Security teams should review logs and network traffic for indicators of compromise related to these vulnerabilities.
For CVE-2026-1731, examine BeyondTrust logs for unusual get_portal_info requests and unexpected WebSocket connections. Review firewall and proxy logs for connections to known malicious infrastructure associated with the Frankfurt VPN node conducting reconnaissance. Check for unauthorized administrative actions or lateral movement originating from BeyondTrust systems.
The Notepad++ compromise requires endpoint detection. Search for evidence of the Chrysalis backdoor, monitor outbound connections from systems running Notepad++, and review process execution logs for unusual child processes spawned by Notepad++ or the WinGUp updater. Network monitoring should flag connections to domains outside the legitimate Notepad++ update infrastructure.
Federal Compliance Deadlines
U.S. Federal Civilian Executive Branch agencies face binding remediation deadlines under CISA's directive. CVE-2025-40536 must be patched by February 15, 2026, while CVE-2026-20700, CVE-2025-15556, and CVE-2024-43468 require remediation by March 5, 2026.
While these deadlines apply specifically to federal agencies, private sector organizations should treat them as recommended timelines reflecting the severity and urgency of these threats. The deadlines account for the active exploitation status and the potential impact of successful attacks, providing guidance for prioritization even outside the federal context.
Key Takeaways
- CVE-2026-1731 moved from proof-of-concept release to active exploitation in under 24 hours, demonstrating that the patch window for critical vulnerabilities has collapsed to hours rather than days
- BeyondTrust Remote Support and Privileged Remote Access users must apply emergency patches immediately, with internet-exposed instances requiring priority remediation
- CISA added four actively exploited vulnerabilities to the KEV catalog, including a sophisticated Notepad++ supply-chain attack by the Lotus Blossom APT group
- Organizations must implement risk-based patching that prioritizes internet-exposed systems and evaluates specific product exposure rather than applying generic severity scores
- Detection and monitoring for indicators of pre-patch exploitation is essential, particularly for BeyondTrust systems showing unusual WebSocket activity or Configuration Manager instances with anomalous database queries
- Federal remediation deadlines of February 15 and March 5 provide practical timelines that private sector organizations should adopt for these actively exploited vulnerabilities
Conclusion
The simultaneous exploitation of CVE-2026-1731 and four additional critical vulnerabilities demonstrates that threat actors are operating with unprecedented speed and coordination. The sub-24-hour weaponization timeline for the BeyondTrust vulnerability eliminates the traditional buffer defenders relied upon to test and deploy patches before facing active threats.
Organizations must fundamentally reassess their vulnerability management processes to accommodate this new reality. Emergency patching protocols need clear triggers and pre-authorized procedures enabling rapid deployment when active exploitation is confirmed. Detection capabilities must provide visibility into exploitation attempts even when patches cannot be deployed immediately due to technical or operational constraints.
The diversity of attack vectors represented in these vulnerabilities reinforces that effective security requires defense-in-depth. No single control or remediation effort addresses all threats. Security teams must maintain comprehensive visibility across remote access platforms, supply-chain mechanisms, enterprise management tools, and endpoint systems to detect and respond to the coordinated multi-vector attacks that define the current threat landscape.
Frequently Asked Questions
Q: How quickly should we patch CVE-2026-1731 compared to our normal patch cycle?
A: Treat CVE-2026-1731 as an emergency requiring deployment within 24-48 hours for internet-exposed BeyondTrust systems. The active exploitation timeline measured in hours rather than days eliminates the safety margin that standard monthly or quarterly patch cycles provide. Internal systems can follow an expedited but controlled deployment over 3-5 days.
Q: What should we do if we cannot immediately patch vulnerable BeyondTrust systems?
A: Implement immediate compensating controls including restricting network access to BeyondTrust systems via firewall rules, requiring VPN access for all remote support sessions, and deploying intrusion detection signatures for the specific get_portal_info exploitation pattern. Enable enhanced logging and monitor for WebSocket connections and unusual administrative activity while preparing for emergency patching.
Q: How do we identify if the Notepad++ supply-chain attack affected our organization?
A: Inventory all Notepad++ installations to identify versions earlier than 8.9.1, review endpoint detection logs for the Chrysalis backdoor signatures, and analyze network traffic for connections to domains outside legitimate Notepad++ update infrastructure. The selective targeting nature means most organizations were likely not affected, but verification requires checking these indicators rather than assuming safety.
Q: Why is Microsoft Configuration Manager still being exploited six months after the patch was released?
A: Many organizations struggle to patch Configuration Manager promptly due to its critical role in enterprise operations and the complexity of testing patches that manage other systems. Attackers exploit this lag, knowing that essential infrastructure components often remain unpatched longer than typical endpoints. The continued exploitation underscores the need for accelerated patching of management infrastructure.
Q: Should we disable auto-updates for software after the Notepad++ supply-chain attack?
A: No, disabling auto-updates broadly would create more risk than it prevents by leaving systems vulnerable to known exploits. Instead, implement network controls ensuring updaters only communicate with verified legitimate update servers, deploy endpoint detection to identify suspicious update behavior, and maintain current versions through managed enterprise software deployment tools that provide verification and rollback capabilities.
Enjoyed this article?
Subscribe for more cybersecurity insights.
