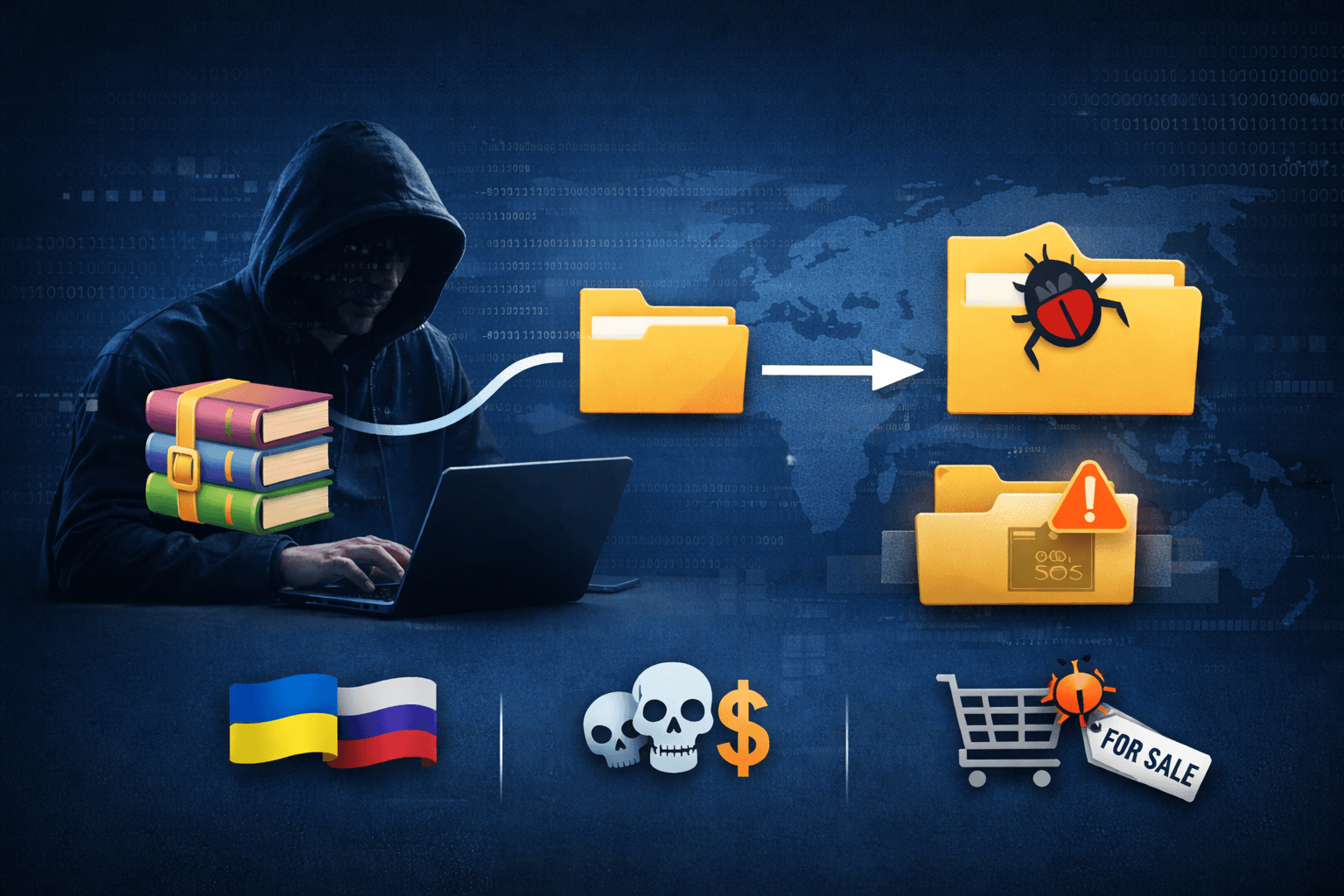
A critical zero-day vulnerability in WinRAR is actively exploited by state-sponsored threat groups and financially motivated attackers, marking yet another example of how archive file handlers remain attractive targets for sophisticated cyber operations. CVE-2025-8088, a path traversal flaw leveraging NTFS Alternate Data Streams, enables attackers to deliver malware with minimal user interaction by disguising malicious payloads inside seemingly harmless compressed files.
According to Google's Threat Intelligence Group, at least five nation-state actors and multiple criminal organizations have weaponized this vulnerability in active campaigns throughout 2025. The attacks predominantly target Ukrainian organizations and critical infrastructure, though financially motivated groups have cast a wider net across multiple regions. What makes this situation particularly concerning is the commercial availability of ready-made exploits through underground brokers, lowering the barrier to entry for less sophisticated threat actors and accelerating widespread exploitation.
This article examines the technical mechanics of CVE-2025-8088, identifies the threat actors exploiting it, analyzes the attack patterns observed in the wild, and provides actionable guidance for security teams defending against this ongoing threat.
Understanding CVE-2025-8088: Technical Breakdown
The vulnerability represents a fundamental flaw in how WinRAR processes archive files containing NTFS Alternate Data Streams, a Windows file system feature that allows multiple data streams to be associated with a single file. Attackers exploit this mechanism to bypass security controls and achieve persistence on compromised systems.
The Path Traversal Mechanism
CVE-2025-8088 enables attackers to write files to arbitrary locations on the victim's file system during archive extraction. The vulnerability specifically affects WinRAR's handling of ADS (Alternate Data Streams) metadata embedded within compressed archives. When a malicious archive is extracted, WinRAR fails to properly validate the destination paths specified in ADS attributes.
This path traversal attack allows threat actors to:
- Write malicious files directly to the Windows Startup folder
- Bypass file extension filters and security warnings
- Execute code automatically at user login without additional interaction
- Maintain persistent access through legitimate Windows functionality
Exploit Chain Architecture
The attack leverages a multi-stage infection process that exploits user trust in familiar file types. Attackers craft specially formatted RAR archives containing a decoy document (typically a PDF, Word document, or Excel spreadsheet) that appears legitimate to the victim. The actual malicious payload resides within an NTFS Alternate Data Stream attached to the decoy file.
Table: CVE-2025-8088 Infection Stages
| Stage | Action | Technical Detail |
|---|---|---|
| Delivery | Victim receives malicious RAR archive | Distributed via phishing, watering holes, or compromised websites |
| Extraction | User opens archive in WinRAR | Malicious ADS metadata triggers path traversal |
| Payload Drop | Malicious files written to Startup folder | LNK, HTA, BAT, CMD, or script files placed for persistence |
| Execution | System restart or user login | Payload automatically executes via Windows Startup mechanism |
| Post-Exploitation | Secondary malware deployment | RATs, stealers, or reconnaissance tools installed |
Why Alternate Data Streams Matter
NTFS Alternate Data Streams were originally designed to support file metadata and compatibility with other file systems. However, their hidden nature makes them ideal for concealing malicious content. Standard file browsers and many security tools do not display ADS content by default, allowing attackers to hide executable code within what appears to be a benign document file.
When WinRAR extracts an archive containing ADS-enabled files, the vulnerability allows attackers to manipulate the extraction path. Instead of placing files in the expected temporary directory, the exploit redirects them to system directories where they will execute automatically, establishing persistence without requiring further victim interaction beyond the initial archive extraction.
Threat Actor Landscape: Who's Exploiting CVE-2025-8088
Google's Threat Intelligence Group has attributed exploitation of CVE-2025-8088 to multiple distinct threat actors with varying objectives and capabilities. The observed campaigns demonstrate both state-sponsored cyber espionage operations and financially motivated criminal activity, illustrating the vulnerability's broad appeal across the threat landscape.
Nation-State Actors and APT Groups
Five confirmed advanced persistent threat (APT) groups have incorporated CVE-2025-8088 into their operational toolkits, with Ukrainian targets receiving disproportionate attention. These state-sponsored actors demonstrate sophisticated tradecraft and operational security, leveraging the vulnerability for strategic intelligence collection and persistent network access.
RomCom (UNC4895): This Russia-linked threat group has extensively utilized CVE-2025-8088 in operations targeting Ukrainian government agencies and critical infrastructure. RomCom deploys custom malware families including NESTPACKER and Snipbot RAT through the vulnerability. Their campaigns often involve elaborate social engineering pretexts tailored to victim organizations, combining technical exploitation with psychological manipulation.
APT44 (Sandworm): The notorious Russian military intelligence unit has integrated the WinRAR flaw into broader campaigns targeting energy, telecommunications, and transportation sectors. APT44's use of STOCKSTAY malware delivered via CVE-2025-8088 demonstrates how established APT groups continuously refresh their technical capabilities by adopting newly discovered vulnerabilities.
TEMP.Armageddon: Also focused on Ukrainian targets, this threat actor has weaponized the vulnerability for cyber espionage operations. Their campaigns align with broader geopolitical objectives and often precede or accompany physical military operations, highlighting the blurred lines between cyber and kinetic warfare.
Turla: The Russian Federal Security Service (FSB)-attributed group has employed CVE-2025-8088 to maintain persistent access within compromised networks. Turla's sophisticated operational security and patient approach to intelligence gathering make their adoption of this vulnerability particularly concerning for high-value targets.
China-linked actors: Multiple Chinese APT groups have been observed testing and deploying exploits for CVE-2025-8088, deploying POISONIVY and other backdoors. While specific attribution remains challenging, these campaigns demonstrate China's continued investment in offensive cyber capabilities targeting intellectual property and strategic intelligence.
Financially Motivated Cybercriminals
Beyond state actors, numerous criminal organizations have embraced CVE-2025-8088 as a reliable infection vector for commodity malware. These groups prioritize volume over sophistication, casting wide nets to compromise as many systems as possible for financial gain.
Table: Malware Families Delivered via CVE-2025-8088
| Malware Type | Examples | Primary Function |
|---|---|---|
| Remote Access Trojans | XWorm, AsyncRAT | Full system control and data exfiltration |
| Information Stealers | Credential harvesters, browser data extractors | Financial account theft and identity fraud |
| Telegram-Controlled Backdoors | Custom bot-based malware | Command and control via encrypted messaging |
| Banking Trojans | Malicious Chrome extensions | Real-time banking credential interception |
Financially motivated actors exploit CVE-2025-8088 to distribute widespread malware campaigns aimed at credential theft, banking fraud, and ransomware deployment. The vulnerability's reliability and low detection rates make it particularly attractive for criminals seeking to maximize return on investment while minimizing operational risk.
The Zero-Day Exploit Marketplace: Commoditization of Advanced Capabilities
The widespread exploitation of CVE-2025-8088 reflects a broader trend in the cybercrime ecosystem: the commercialization and commoditization of sophisticated exploit capabilities. Security researchers have identified a broker known as "zeroplayer" who actively advertises ready-made exploits for this and other critical vulnerabilities.
The Exploit Broker Model
Zeroplayer represents a new breed of cyber mercenary who acts as an intermediary between vulnerability researchers and threat actors. This broker model democratizes access to advanced exploitation techniques, enabling less sophisticated attackers to deploy nation-state-level capabilities. The typical exploit package includes:
- Proof-of-concept code demonstrating successful exploitation
- Weaponized exploit chains ready for operational deployment
- Technical documentation and implementation guidance
- Post-exploitation tools and payload delivery mechanisms
- Updates and patches as security researchers discover detection methods
Price Points and Market Dynamics
Intelligence gathered from underground forums reveals zeroplayer's pricing structure for various zero-day exploits, illustrating the economics of the vulnerability marketplace:
Table: Zero-Day Exploit Pricing (Underground Market)
| Vulnerability Type | Target Software | Price Range (USD) | Estimated Market Size |
|---|---|---|---|
| Archive Handler Flaws | WinRAR, 7-Zip | $80,000 - $150,000 | 15-20 active buyers |
| Office Suite Exploits | Microsoft Office | $150,000 - $250,000 | 30+ interested parties |
| VPN Zero-Days | Enterprise VPN solutions | $200,000 - $300,000 | High-value APT groups |
| Windows LPE | Local privilege escalation | $100,000 - $200,000 | Broad criminal interest |
| EDR Bypass Techniques | Major security vendors | $150,000 - $250,000 | Ransomware operators |
These price points reflect the value attackers place on undetected, reliable exploitation capabilities. For comparison, a single successful ransomware attack can yield millions in extortion payments, making a $150,000 investment in a reliable zero-day exploit economically rational for organized criminal groups.
Implications for Defenders
The exploit marketplace fundamentally changes the threat landscape security teams must navigate. Previously, zero-day vulnerabilities were primarily the domain of well-resourced nation-state actors with in-house vulnerability research capabilities. Now, any threat actor with sufficient capital can purchase sophisticated exploits, collapsing the traditional pyramid of capability and threat sophistication.
This commoditization means organizations can no longer rely on threat intelligence based solely on actor profiling. A seemingly unsophisticated criminal group may suddenly deploy advanced techniques previously attributed only to APT groups. Defense strategies must account for this democratization of offensive capabilities.
Important: The emergence of exploit brokers like zeroplayer accelerates the timeline between vulnerability discovery and widespread exploitation, compressing the window for defensive patching and mitigation.
Detection and Defense Strategies
Protecting against CVE-2025-8088 exploitation requires a multi-layered security approach combining technical controls, user awareness, and proactive threat hunting. Organizations must address both the immediate vulnerability and the broader class of archive file exploitation techniques.
Immediate Mitigation Steps
Security teams should implement these controls immediately to reduce exposure to CVE-2025-8088 attacks:
-
Patch Management: Update WinRAR to the latest version that addresses CVE-2025-8088. Organizations using WinRAR 6.24 or earlier remain vulnerable and should prioritize updates.
-
Alternative Archive Tools: Consider migrating to alternative compression utilities with better security track records. Evaluate 7-Zip (open source with active security maintenance) or Windows' built-in ZIP handling for less complex use cases.
-
Email Filtering: Configure email security gateways to quarantine or block RAR file attachments, particularly from external senders. Many organizations have no legitimate business need for RAR files in email communications.
-
Application Whitelisting: Implement application control policies that prevent automatic execution of files placed in the Startup folder without administrative approval.
-
Endpoint Detection Response: Configure EDR solutions to monitor file creation events in system directories, particularly the Windows Startup folder and other persistence locations.
Detection Capabilities
Effective detection requires visibility into multiple attack stages, from initial delivery through post-exploitation activity. Security teams should implement monitoring for the following indicators:
File System Monitoring:
- Unexpected file creation in Windows Startup folders (user and system-level)
- Files with NTFS Alternate Data Streams (use PowerShell or specialized ADS scanning tools)
- Archive extraction to unusual directories outside temporary or user-controlled spaces
- LNK, HTA, BAT, CMD, or script files appearing in startup locations
Network Monitoring:
- Outbound connections from newly created processes in startup directories
- Command-and-control traffic patterns associated with RATs like XWorm, AsyncRAT
- DNS queries to newly registered domains or suspicious TLDs
- Telegram API communications (used by bot-controlled backdoors)
Behavioral Analytics:
- Process execution chains originating from archive extraction tools
- Unusual child processes spawned by WinRAR.exe
- Registry modifications creating new startup items
- Privilege escalation attempts following archive extraction
Advanced Threat Hunting Queries
Security operations teams should incorporate these detection rules into their SIEM and EDR platforms:
PowerShell detection for Alternate Data Streams:
Get-ChildItem -Path C:\ -Recurse | Get-Item -Stream * | Where-Object {$_.Stream -ne ':$DATA'}
Windows Event Log monitoring:
- Event ID 4688 (Process Creation) with parent process WinRAR.exe and command-line parameters indicating startup folder activity
- Event ID 4663 (File System access) for write operations in
%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\
Pro Tip: Create baseline profiles of normal archive extraction behavior in your environment. Statistical anomalies in extraction patterns, file types, or destination directories often indicate exploitation attempts.
Organizational Response Framework
Beyond technical controls, organizations need structured processes for responding to potential CVE-2025-8088 exploitation. This framework outlines the key phases of an effective response.
Assessment and Prioritization
Begin by evaluating your organization's exposure to this vulnerability. Consider these factors:
- WinRAR deployment scope: Identify all systems with WinRAR installed through asset inventory and software audit tools
- User populations at risk: Prioritize updates for high-value targets including executives, system administrators, and users handling sensitive data
- Business criticality: Assess which systems process external archives and their importance to business operations
- Current security controls: Evaluate existing protections such as email filtering, EDR coverage, and user security awareness
Organizations in sectors targeted by the nation-state actors exploiting CVE-2025-8088 should treat this vulnerability as critical priority. This includes defense contractors, government agencies, critical infrastructure providers, and organizations with Ukrainian operations or affiliations.
Incident Response Procedures
If you suspect or confirm CVE-2025-8088 exploitation in your environment, follow this structured response:
Table: Incident Response Checklist
| Phase | Actions | Key Stakeholders |
|---|---|---|
| Containment | Isolate affected systems from network; disable WinRAR; preserve forensic evidence | SOC, IT Operations, Legal |
| Eradication | Remove malicious files from Startup folders; scan for persistence mechanisms; remediate compromised accounts | Incident Response, Forensics Team |
| Recovery | Rebuild compromised systems; restore from clean backups; implement enhanced monitoring | IT Operations, Business Units |
| Lessons Learned | Document attack timeline; update detection rules; improve security controls; conduct tabletop exercises | Security Leadership, Risk Management |
Policy and Governance Considerations
Update organizational security policies to address the risks highlighted by CVE-2025-8088:
- Establish clear guidance on handling external archive files
- Define acceptable use policies for compression utilities
- Require security approval for archive tools in production environments
- Mandate regular security awareness training covering phishing and malicious attachments
- Implement vendor risk management processes that evaluate third-party software security
Organizations subject to compliance frameworks such as GDPR, HIPAA, PCI DSS, or SOC 2 should document how CVE-2025-8088 mitigation aligns with their compliance obligations, particularly requirements for vulnerability management and incident response capabilities.
Key Takeaways
- CVE-2025-8088 exploits NTFS Alternate Data Streams to write malicious files to arbitrary locations, enabling automatic execution via Windows Startup folders with minimal user interaction beyond opening a malicious archive.
- Five nation-state actors and numerous criminal groups actively exploit this vulnerability, demonstrating its broad appeal across the threat landscape for both espionage and financially motivated attacks.
- The underground exploit marketplace enables less sophisticated threat actors to purchase ready-made exploits for $80,000-$300,000, democratizing access to advanced capabilities and compressing the timeline between vulnerability discovery and widespread exploitation.
- Effective defense requires immediate patching, multi-layered technical controls including email filtering and EDR monitoring, and proactive threat hunting for indicators of compromise in startup directories and file system activity.
- Organizations must move beyond reactive patching to implement comprehensive archive file security controls, user awareness training, and structured incident response procedures that account for the evolving threat landscape.
Conclusion
CVE-2025-8088 represents more than a single software vulnerability—it exemplifies the evolving dynamics of modern cyber threats where advanced capabilities rapidly proliferate through commercial exploit marketplaces. The simultaneous exploitation by nation-state actors and cybercriminals demonstrates how traditional threat boundaries have dissolved, requiring security teams to defend against the full spectrum of adversaries regardless of organizational size or industry.
The technical sophistication of this attack, combined with its social engineering elements and abuse of legitimate Windows functionality, highlights why defense-in-depth remains essential. No single control prevents exploitation; instead, layered security controls create multiple opportunities to detect and disrupt the attack chain. Security teams must prioritize both immediate remediation through patching and longer-term improvements to security architecture, detection capabilities, and incident response processes.
As the exploit marketplace continues to mature and lower barriers to entry for threat actors, organizations cannot afford complacency. Regular security assessments, proactive threat hunting, and continuous security awareness training form the foundation of resilience against vulnerabilities like CVE-2025-8088 and the inevitable zero-days that will follow.
Frequently Asked Questions
Q: How can I tell if my organization has been compromised through CVE-2025-8088?
A: Check the Windows Startup folders (%APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\ and %PROGRAMDATA%\Microsoft\Windows\Start Menu\Programs\Startup\) for unexpected LNK, HTA, BAT, CMD, or script files. Use PowerShell to scan for files with NTFS Alternate Data Streams. Review EDR logs for unusual process execution chains originating from WinRAR.exe, particularly processes writing to startup directories. Consider engaging forensic specialists if you identify suspicious activity.
Q: Are alternative compression tools like 7-Zip vulnerable to similar attacks?
A: While 7-Zip and other compression utilities have experienced security vulnerabilities in the past, CVE-2025-8088 is specific to WinRAR's handling of NTFS Alternate Data Streams. However, path traversal vulnerabilities represent a broader class of archive extraction flaws that can affect multiple tools. Maintain current versions of any compression software and follow defense-in-depth principles regardless of which tool you use.
Q: What should I do if WinRAR is required for business operations?
A: Update immediately to the latest patched version addressing CVE-2025-8088. Implement compensating controls including email filtering to block RAR attachments, application whitelisting to prevent automatic startup execution, and EDR monitoring focused on WinRAR process behavior. Consider virtualized or sandboxed environments for processing external archives. Train users to verify archive sources before extraction and report suspicious files to security teams.
Q: How does the exploit marketplace impact my organization's security strategy?
A: The commercialization of exploits means organizations face threats from a broader range of adversaries with varying sophistication levels. Security strategies must account for rapid weaponization of newly disclosed vulnerabilities and assume that any critical flaw will be quickly exploited. This reality demands faster patch deployment cycles, robust vulnerability management processes, and detection capabilities that identify exploitation attempts rather than relying solely on threat actor attribution or expected sophistication levels.
Q: What frameworks should guide our response to vulnerabilities like CVE-2025-8088?
A: Leverage established security frameworks such as NIST Cybersecurity Framework for overall security program structure, CIS Controls for specific technical safeguards, and MITRE ATT&CK for understanding adversary tactics and techniques. Specifically, MITRE ATT&CK techniques T1566.001 (Phishing with Attachment) and T1547.001 (Boot or Logon Autostart Execution via Registry Run Keys) provide context for CVE-2025-8088 exploitation patterns. Map your security controls to these frameworks and identify gaps requiring additional investment or process improvements.
Enjoyed this article?
Subscribe for more cybersecurity insights.
