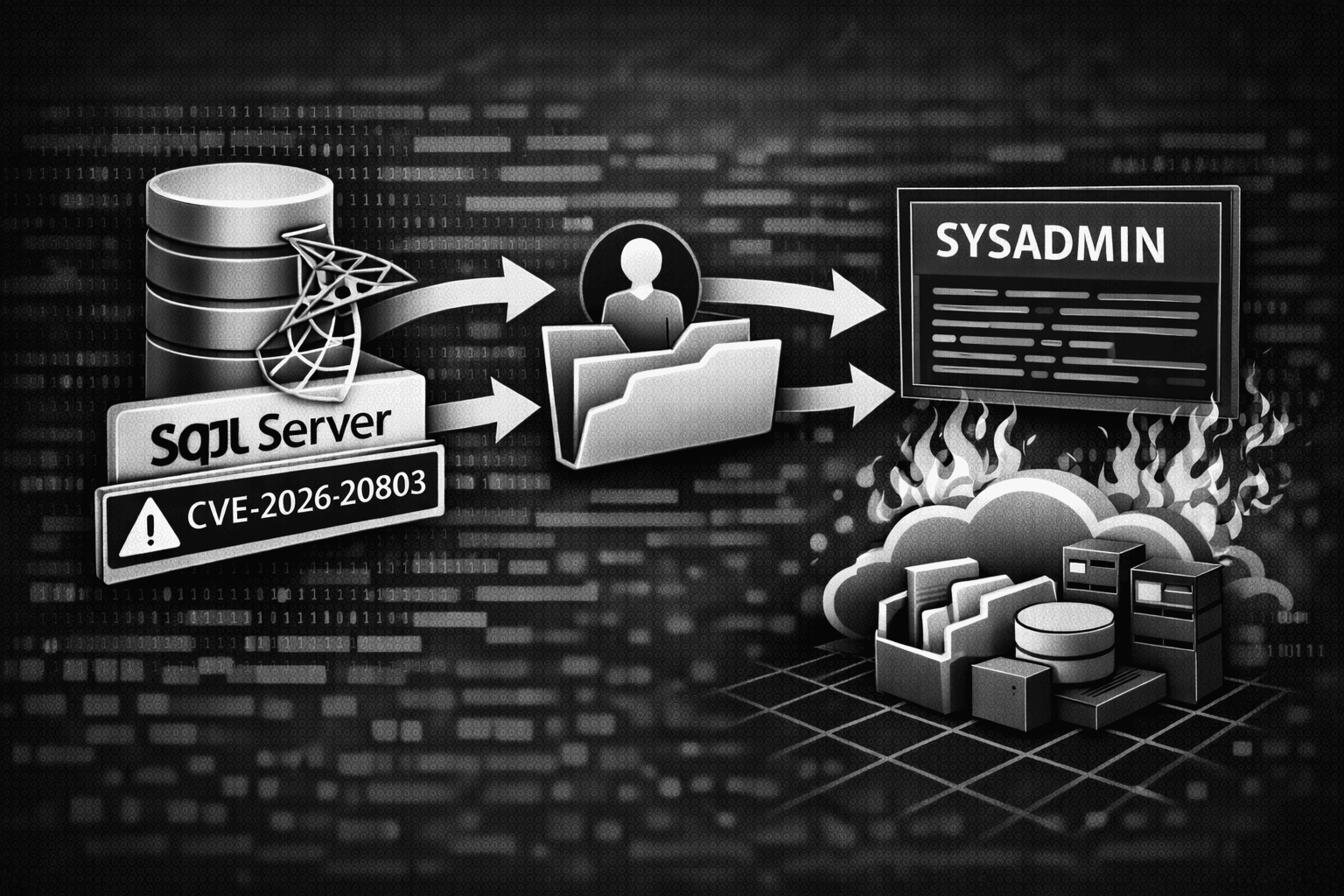
A critical vulnerability in Microsoft SQL Server is giving authenticated attackers a direct path to system-level administrative control — and the blast radius is significant. CVE-2026-20803 stems from missing authentication checks around sensitive database engine functions, meaning any attacker who already holds database credentials can bypass normal access controls entirely, elevate to the highest privilege tier, and execute arbitrary code or access every data object in the instance.
Microsoft released patches on January 13, 2026, but the exploitation risk is far from contained. SQL Server is embedded in enterprise infrastructure at extraordinary scale — powering ERP systems, healthcare records platforms, financial databases, and line-of-business applications across virtually every industry. Organizations running unpatched on-premises deployments or cloud-hosted SQL Server instances remain fully exposed. For environments subject to HIPAA, PCI DSS, or SOC 2, an unpatched SQL Server isn't just a technical risk — it's an active compliance liability. This post explains how the vulnerability works, what attackers can do with it, and exactly how to prioritize your response.
Understanding CVE-2026-20803: What the Vulnerability Actually Does
To defend against this flaw effectively, your team needs to understand the underlying mechanism — not just the severity rating. CVE-2026-20803 is a privilege escalation vulnerability, which means exploitation requires an attacker to already hold some level of authenticated access to the SQL Server instance before the flaw becomes exploitable.
The Missing Authentication Check Problem
The vulnerability originates from missing authorization validation around internal database engine functions that should be restricted to system administrators (sysadmin role). Under normal access controls, these functions are gated — only principals with the appropriate privilege level can invoke them. CVE-2026-20803 bypasses this gate entirely.
An authenticated attacker with low-level database permissions — a read-only user, a service account, even a developer credential — can call these sensitive engine functions without triggering the expected authorization check. SQL Server processes the request as if it originated from a privileged principal, granting the attacker sysadmin-equivalent rights within the engine.
This failure maps directly to MITRE ATT&CK T1078 (Valid Accounts) for initial access and T1068 (Exploitation for Privilege Escalation) for the escalation phase. The attacker never needs to compromise additional systems or intercept credentials — the database engine itself promotes them.
What Sysadmin Access Enables
The consequences of reaching sysadmin on a SQL Server instance are severe. At this privilege level, an attacker can:
- Execute operating system commands via
xp_cmdshell, effectively gaining code execution on the underlying host - Read, modify, or delete any database, table, or record in the instance — including encrypted data if keys are stored within SQL Server
- Create or modify SQL Server logins and roles, establishing persistence that survives patch deployment
- Access linked servers, potentially pivoting to other database instances on the network
- Disable SQL Server audit logging and traces, eliminating forensic evidence
Important: The path from CVE-2026-20803 exploitation to full host-level compromise is short. If xp_cmdshell is enabled or can be re-enabled by a sysadmin-level principal, attackers can break out of the database layer entirely and execute commands on the Windows Server host.
Affected Versions and Deployment Models
Microsoft's advisory covers multiple SQL Server versions and service packs. The vulnerability affects both on-premises deployments and SQL Server installed on cloud-hosted virtual machines (IaaS). It is distinct from Azure SQL Database's managed service layer — fully managed PaaS deployments receive patches through Microsoft's service infrastructure, but SQL Server installed on Azure VMs, AWS EC2, or GCP Compute Engine requires manual patching by the customer.
Table: CVE-2026-20803 Exposure by Deployment Model
| Deployment Model | Patch Responsibility | Automatic Update Available | Exposure Level |
|---|---|---|---|
| On-premises SQL Server | Customer | No — manual patching required | Critical |
| SQL Server on Azure VM | Customer | No — manual patching required | Critical |
| SQL Server on AWS EC2 / GCP | Customer | No — manual patching required | Critical |
| Azure SQL Database (PaaS) | Microsoft | Yes — service-managed | Low |
| Azure SQL Managed Instance | Microsoft | Yes — service-managed | Low |
The Exploitation Path: From Low-Privilege Credential to Full Database Takeover
Understanding the realistic exploitation scenario helps security teams assess their actual risk exposure and prioritize compensating controls for environments where patching cannot happen immediately.
Realistic Attack Scenarios
Consider a common enterprise scenario: a developer has a read-only SQL Server login for a reporting database. That login was created years ago, the password hasn't rotated in 18 months, and it's stored in a configuration file on a web application server. An attacker compromises the web app through an unrelated vulnerability, extracts the connection string, and now holds a low-privilege SQL Server credential.
Before CVE-2026-20803, that credential provided limited value — the attacker could read reporting data but couldn't meaningfully escalate. With this vulnerability unpatched, that same credential becomes a master key to the entire SQL Server instance and potentially the underlying host.
This scenario is not theoretical. Credential theft from application configuration files is one of the most common post-exploitation techniques, and SQL Server connection strings are among the most frequently exposed secrets in enterprise environments (Verizon DBIR, 2024).
How Attackers Establish Persistence After Escalation
Once an attacker achieves sysadmin rights through CVE-2026-20803, their first priority is typically persistence — ensuring they retain access even after the vulnerability is patched. Common persistence techniques at the sysadmin level include:
- Creating a new SQL Server login with sysadmin role membership under a plausible service account name
- Enabling and using
xp_cmdshellto add a local Windows administrator account on the host - Installing SQL Server Agent jobs that execute malicious code on a schedule
- Modifying existing stored procedures or triggers to execute attacker-controlled logic
Pro Tip: After patching, don't assume you're clean. Audit all SQL Server logins created after your earliest possible exposure date, review SQL Server Agent jobs for unauthorized entries, and check for any changes to stored procedures or triggers in high-value databases.
Table: Post-Exploitation Persistence Techniques and Detection Methods
| Persistence Technique | SQL Server Mechanism | Detection Query / Log Source | Difficulty to Detect |
|---|---|---|---|
| Rogue sysadmin login | CREATE LOGIN + sp_addsrvrolemember | SQL Server Audit: Login events | Low |
| Scheduled malicious job | SQL Server Agent Job | msdb.dbo.sysjobs audit | Medium |
| Modified stored procedure | ALTER PROCEDURE | DDL Change Tracking, Git comparison | Medium |
| xp_cmdshell OS command | EXEC xp_cmdshell | SQL Server Audit: Object Access | Low |
| Linked server pivot | Linked server query | Linked server access audit logs | High |
Patching and Compensating Controls: Your Response Prioritization Framework
Patching is the only complete remediation for CVE-2026-20803. However, the reality of enterprise SQL Server deployments — with application compatibility testing requirements, maintenance windows, and production dependencies — means patching takes time. Your compensating controls strategy must cover that gap.
Patching Priority and Process
Apply the January 13, 2026 cumulative update to all affected SQL Server instances. Prioritize in this order:
- Internet-facing SQL Server instances or those accessible from DMZ networks
- SQL Server instances storing regulated data (PHI, PII, cardholder data)
- SQL Server instances with
xp_cmdshellenabled - SQL Server instances where service account credentials are stored in application configuration files
- Internal instances with broad network accessibility
Test patches in non-production environments first, but compress your testing timeline — a critical privilege escalation vulnerability warrants aggressive patching urgency. NIST SP 800-40 recommends patching critical vulnerabilities within 30 days; for actively-targeted flaws of this severity, your practical target should be within 14 days or less.
Compensating Controls for Unpatched Systems
While patches are being tested and deployed, apply these compensating controls to reduce exploitation risk:
- Restrict network access to SQL Server ports (default TCP 1433) using host-based firewalls and network ACLs — allow only application servers and authorized management hosts
- Audit and rotate SQL Server credentials stored in application configuration files, secrets managers, and documented runbooks
- Disable
xp_cmdshellon all instances where it is not operationally required — this severs the path from database escalation to OS-level code execution - Enable SQL Server Audit and forward logs to your SIEM with alerting on new login creation and sysadmin role assignments
- Review current sysadmin role membership and remove any principals that do not require that level of access
Compliance Implications
Organizations subject to regulatory frameworks face specific obligations. Under HIPAA, unpatched vulnerabilities in systems storing protected health information (PHI) constitute a known risk that must be documented in your risk management plan along with active mitigation measures. PCI DSS Requirement 6.3.3 mandates that all system components are protected from known vulnerabilities by installing applicable security patches. SOC 2 Type II auditors will specifically review patch management evidence for critical CVEs during your audit period.
Table: Compliance Requirements and Response Obligations for CVE-2026-20803
| Framework | Relevant Requirement | Obligation | Timeline Expectation |
|---|---|---|---|
| PCI DSS v4.0 | Requirement 6.3.3 | Apply security patches | Critical patches within 1 month |
| HIPAA Security Rule | 45 CFR §164.308(a)(5) | Address known vulnerabilities | Document + mitigate promptly |
| SOC 2 (CC7.1) | Change management controls | Patch and evidence collection | Within audit period |
| ISO 27001 | Annex A 8.8 | Technical vulnerability management | Risk-based prioritization |
| CIS Controls v8 | Control 7 | Continuous vulnerability management | Critical = highest priority |
Key Takeaways
- Patch all SQL Server instances immediately using Microsoft's January 13, 2026 cumulative update — prioritize internet-facing, regulated-data, and xp_cmdshell-enabled instances first
- Disable
xp_cmdshellon every SQL Server instance where it is not required — this single control breaks the most dangerous post-exploitation path from database to OS-level compromise - Audit sysadmin role membership today and revoke any principals that do not legitimately require that level of access
- Rotate all SQL Server credentials stored in application configuration files — these are the most commonly harvested tokens in post-exploitation scenarios
- Enable SQL Server Audit with SIEM forwarding and build alert rules for new login creation, role assignment changes, and
xp_cmdshellexecution - Document compensating controls formally in your risk register to satisfy HIPAA, PCI DSS, and SOC 2 obligations while patches are being deployed
Conclusion
CVE-2026-20803 is a high-impact SQL Server privilege escalation vulnerability that converts any valid database credential into potential full system control. The patch exists and has been available since January 13, 2026 — the only question is how quickly your organization deploys it across every affected instance. For environments where patching is still in progress, the compensating controls outlined in this post — network restriction, credential rotation, xp_cmdshell disablement, and audit logging — reduce your exposure materially while you work toward full remediation. SQL Server sits at the center of too much critical business and regulated data to treat this as a routine patch cycle item. Prioritize it, document your response, and verify that no attacker has already leveraged the vulnerability to establish persistence before your patches land.
Frequently Asked Questions
Q: Does CVE-2026-20803 affect Azure SQL Database and Azure SQL Managed Instance? A: No. Fully managed PaaS offerings like Azure SQL Database and Azure SQL Managed Instance are patched at the service level by Microsoft and are not vulnerable to this CVE. The vulnerability affects SQL Server software installed and managed by the customer — including on-premises deployments and SQL Server running on virtual machines in any cloud environment.
Q: An attacker needs existing database credentials to exploit this — does that make it lower risk? A: The authentication requirement reduces the attack surface compared to unauthenticated vulnerabilities, but it does not make the risk low. SQL Server credentials are frequently exposed through application configuration files, credential-stuffing attacks, phishing, and insider threats. Any organization with SQL Server accessible to more than a tightly controlled set of principals has meaningful exposure, and the escalation from any valid credential to full sysadmin access makes this a critical-priority patch.
Q: How do I identify whether an attacker has already exploited this vulnerability in my environment?
A: Review SQL Server Audit logs and the Windows Security Event Log for new login creation events, sysadmin role membership changes, and xp_cmdshell execution — particularly any activity that occurred under accounts that should not have had elevated privileges. Also query sys.server_principals and sys.server_role_members to identify any sysadmin-level principals created or modified after your earliest possible exposure date.
Q: What SQL Server versions are affected by CVE-2026-20803? A: Microsoft's security advisory covers the full list of affected versions and the corresponding cumulative updates. You should consult the official MSRC (Microsoft Security Response Center) advisory directly for the definitive version matrix, as the affected scope includes multiple SQL Server major versions and service pack levels. Apply the appropriate cumulative update for each version in your environment rather than assuming a single patch covers all deployments.
Q: Does enabling Transparent Data Encryption (TDE) on SQL Server databases protect against this vulnerability? A: No. Transparent Data Encryption (TDE) protects data at rest from physical media theft — it encrypts database files on disk. An attacker who escalates to sysadmin through CVE-2026-20803 operates within the SQL Server engine itself, where TDE encryption is transparent and all data is accessible in plaintext. TDE provides no protection against in-engine privilege escalation attacks.
Enjoyed this article?
Subscribe for more cybersecurity insights.
