When the U.S. Department of Justice, in coordination with German and Canadian authorities, dismantled the infrastructure behind four major botnets, the numbers were staggering: over 3 million compromised devices worldwide, hundreds of thousands in the United States alone. These weren't obscure, theoretical threats. They were active networks used to launch distributed denial-of-service (DDoS) attacks against real targets—hospitals, financial institutions, government systems, and enterprises across multiple sectors.
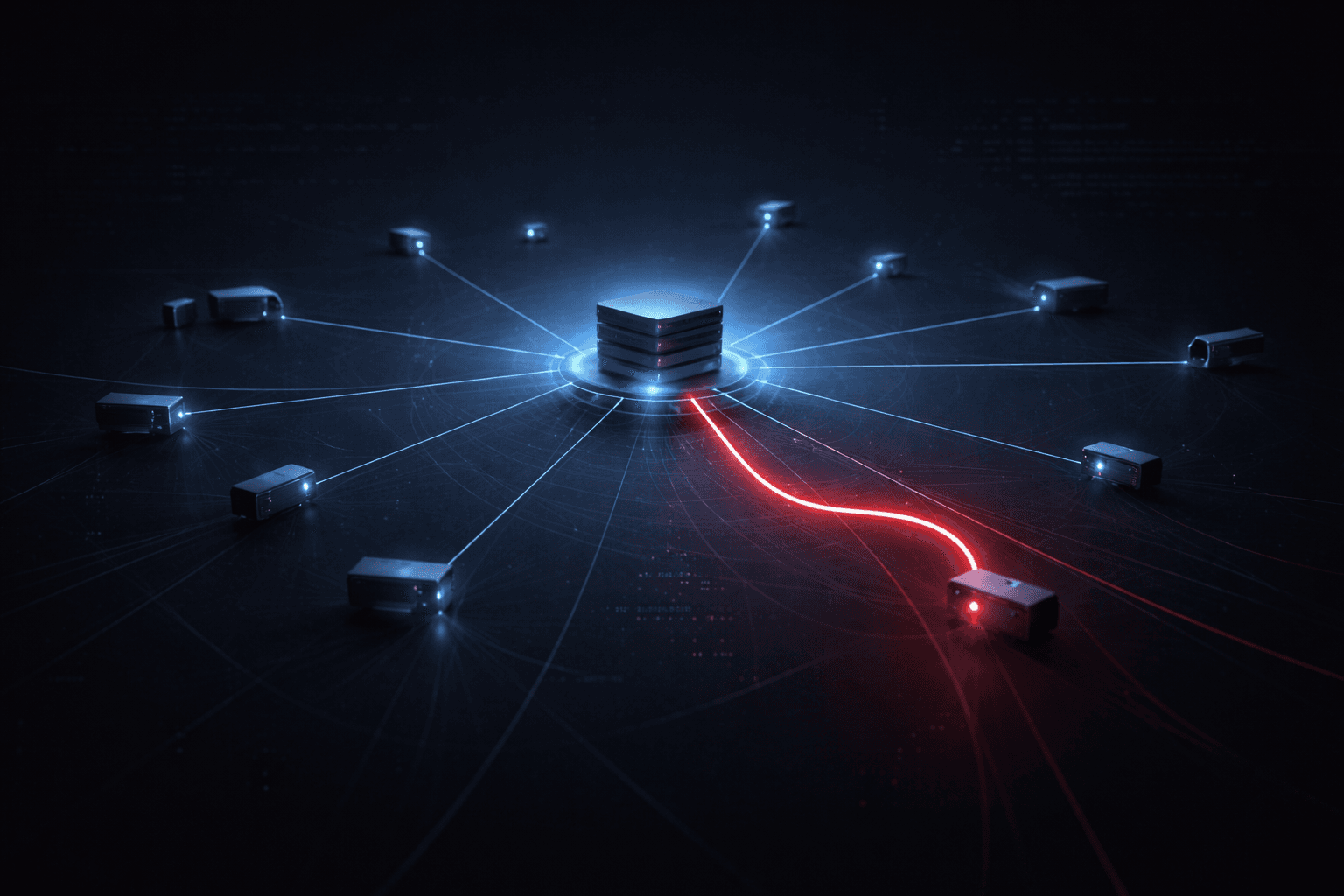
The operation involved seizing servers and redirecting botnet traffic away from attacker-controlled command-and-control (C2) infrastructure, effectively severing the communication channels that allowed criminal operators to coordinate attacks at scale. But here is the harder truth: for every botnet dismantled by law enforcement, others continue to grow undetected, fed by poorly secured IoT devices, unpatched edge appliances, and consumer routers that organizations overlook entirely.
This post examines what this takedown reveals about the modern botnet threat, how these networks operate, what defenders should learn from the operation, and the concrete steps your organization can take to avoid contributing to—or becoming a victim of—the next one.
How Modern Botnets Are Built and Weaponized
Understanding the anatomy of a botnet is the first step toward defending against it. Modern botnets are not built through sophisticated targeted intrusions. They are assembled at scale by exploiting the vast population of devices that are deployed and then forgotten.
Infection Vectors: How Devices Become Nodes
Botnet operators use a small set of highly effective infection methods to recruit devices. The most common vectors include:
- Credential stuffing against default or weak passwords on routers, IP cameras, and network-attached storage (NAS) devices
- Exploitation of known unpatched vulnerabilities in consumer and small-business IoT firmware—many of which have public proof-of-concept exploit code available for years before vendors ship patches
- Drive-by malware downloads that compromise endpoint devices and enroll them into a botnet without any visible symptoms to the user
- Supply chain compromises where devices arrive pre-infected or pull malicious firmware updates from hijacked update servers
Once infected, a device receives instructions from a C2 server. The device owner typically observes nothing unusual. Bandwidth consumption increases marginally. The device continues its normal function. The botnet operator gains a persistent, distributed attack platform.
DDoS as a Service: The Operational Reality
The four botnets dismantled in this operation were used primarily to launch DDoS attacks. What distinguishes modern botnet-driven DDoS from older volumetric attacks is the geographic and network diversity of the attacking nodes. A botnet of 3 million devices distributed across residential ISPs, cloud providers, and enterprise networks produces traffic that is extremely difficult to filter using traditional source-based blocking. Legitimate-looking traffic from real residential IP addresses overwhelms rate limiting and IP reputation filtering alike.
Important: DDoS attacks launched from large consumer botnets are often indistinguishable from legitimate traffic spikes at the network edge. Organizations that rely solely on IP reputation blocking or simple volumetric thresholds will find these attacks extremely difficult to mitigate without upstream scrubbing infrastructure.
Table: Modern DDoS Attack Types Enabled by Botnets
| Attack Type | Mechanism | Primary Target | Mitigation Complexity |
|---|---|---|---|
| Volumetric flood | Raw bandwidth exhaustion | Internet links | High — requires upstream mitigation |
| TCP state exhaustion | Connection table overflow | Firewalls, load balancers | Medium — rate limiting + SYN cookies |
| Application layer (L7) | HTTP/S request floods | Web applications, APIs | High — requires behavioral analysis |
| Amplification/reflection | Spoofed UDP to open resolvers | Any internet host | Medium — ingress filtering (BCP38) |
| Slow-rate attacks | Slow HTTP, Slowloris | Web servers | Medium — connection timeout tuning |
What the Takedown Operation Reveals for Defenders
International botnet takedowns are increasingly sophisticated operations, but they offer defenders more than headline reassurance. The methods law enforcement uses to dismantle botnets map directly onto defensive capabilities organizations should build internally.
The Role of Telemetry Sharing
The DOJ operation succeeded in part because of telemetry sharing between private sector partners and law enforcement. ISPs, cloud providers, and security vendors contributed data that allowed investigators to map C2 infrastructure, identify infected device populations, and time the sinkholing operation—redirecting malicious traffic to law enforcement-controlled servers—to be maximally disruptive to botnet operators.
For defenders, this highlights a concrete action: participate in threat intelligence sharing communities. Frameworks like the Traffic Light Protocol (TLP) govern how shared threat data can be redistributed, and sector-specific Information Sharing and Analysis Centers (ISACs) provide structured channels for contributing and receiving operational intelligence. Organizations that share telemetry about C2 indicators they observe in their own traffic contribute directly to operations like this one.
Sinkholing and Its Defensive Lessons
During the operation, authorities redirected traffic destined for attacker C2 servers to law enforcement-controlled sinkholes. This technique—well-established in botnet disruption—also has direct application in enterprise environments. Organizations that monitor for traffic to known malicious C2 domains, and that block or redirect that traffic at the DNS or network layer, can detect infected devices on their own networks before those devices contribute to attacks against others.
- Deploy DNS-based filtering or DNS response policy zones (RPZ) to intercept queries to known C2 domains
- Monitor for connections to IP ranges associated with known botnet infrastructure using threat intelligence feeds
- Alert on devices generating unusual outbound traffic volumes, particularly to non-standard ports or unfamiliar geographies
- Review NetFlow or equivalent flow data regularly; infected IoT devices often exhibit distinctive traffic patterns even without known-bad indicators
Table: Defensive Controls Mapped to Botnet Infection Stages
| Infection Stage | Attack Activity | Defensive Control | Framework Reference |
|---|---|---|---|
| Initial infection | Credential brute force | MFA, default credential policy | CIS Control 5 |
| Exploitation | Firmware vulnerability abuse | Patch management, asset inventory | CIS Control 7, NIST SP 800-40 |
| C2 establishment | DNS/HTTP beacon to C2 | DNS filtering, RPZ, outbound proxy | CIS Control 9 |
| Attack execution | DDoS traffic generation | NetFlow anomaly detection, ISP coordination | NIST SP 800-61 |
| Persistence | Firmware implant | Integrity monitoring, secure boot | CIS Control 10 |
Securing IoT and Edge Devices That Become Botnet Nodes
The devices that composed these botnets were not exotic targets. They were the same routers, cameras, and smart devices deployed by the millions in homes and small offices—and in enterprise environments where shadow IT and unmanaged device sprawl are persistent challenges. How do you secure devices that you may not even know exist on your network?
Building an IoT Asset Inventory
You cannot secure what you cannot see. CIS Control 1 (Inventory and Control of Enterprise Assets) is foundational for a reason: botnet operators rely on the fact that defenders don't maintain accurate inventories of their network-attached devices. Practical steps include:
- Run continuous network discovery scans—not just periodic audits—using passive and active techniques
- Maintain a categorized asset inventory that distinguishes managed endpoints, unmanaged IoT devices, OT/ICS systems, and guest/BYOD devices
- Flag any device running end-of-life firmware for which vendor patches are no longer available—these are permanent botnet candidates
- Apply network segmentation to isolate IoT devices from sensitive internal systems; a compromised IP camera should never have a path to your domain controllers
Hardening IoT Devices Against Exploitation
Many IoT devices cannot run traditional endpoint agents. Hardening must happen at the device configuration level and at the network boundary. Prioritize these controls:
- Change default credentials immediately upon deployment; use a privileged access management (PAM) solution or documented credential vault to track unique passwords per device
- Disable unnecessary services — UPnP, Telnet, and remote management interfaces are common exploitation vectors and are enabled by default on many consumer-grade devices
- Enable automatic firmware updates where vendor implementations are trustworthy; for enterprise devices, test updates in a staging environment before broad deployment
- Implement network access control (NAC) to enforce device posture requirements before granting network access
Pro Tip: For devices that cannot be updated or hardened, compensating controls at the network layer are your last line of defense. Place these devices behind a dedicated VLAN with strict egress filtering that limits outbound connections to only what the device legitimately requires to function.
Compliance and Regulatory Implications
Botnet participation—even unknowingly—carries compliance risk. If a device on your network is recruited into a botnet and used to attack a third party, your organization may face questions about whether adequate security controls were in place.
Framework Alignment for Botnet Prevention
Table: Compliance Framework Requirements Relevant to Botnet Prevention
| Framework | Relevant Control | Requirement Summary |
|---|---|---|
| NIST CSF 2.0 | DE.CM-01 | Networks and network services are monitored to find potentially adverse events |
| CIS Controls v8 | Control 1, 7, 13 | Asset inventory, vulnerability management, network monitoring |
| ISO/IEC 27001:2022 | A.8.7, A.8.20 | Protection against malware, network security controls |
| PCI DSS v4.0 | Req. 6.3, 10.2 | Vulnerability management, audit log monitoring |
| HIPAA Security Rule | §164.312(a)(1) | Access control; monitoring for unauthorized access |
| SOC 2 (CC7.2) | CC7.2 | System monitoring for security events and anomalies |
Incident Reporting When Devices Are Compromised
Under GDPR Article 33, organizations must report personal data breaches to supervisory authorities within 72 hours of becoming aware. If a botnet-infected device on your network exfiltrates personal data as part of its operation—a common secondary function of multi-purpose botnet malware—that constitutes a reportable breach. Establish clear internal procedures for escalating suspected botnet infections to your privacy and legal teams alongside your technical response.
Key Takeaways
- Contribute threat telemetry to sector ISACs and law enforcement partnerships—operational intelligence sharing directly enables botnet takedowns like this one
- Deploy DNS-based filtering and C2 blocklists to detect and isolate botnet-infected devices on your own network before they participate in attacks against others
- Audit your IoT and edge device inventory immediately; any device with default credentials, end-of-life firmware, or no active management is a botnet node waiting to be recruited
- Segment unmanaged and IoT devices into dedicated VLANs with strict egress filtering as a compensating control where device-level hardening is not possible
- Test your DDoS resilience through tabletop exercises and upstream ISP coordination; botnet-driven attacks are designed to defeat on-premises mitigation tools alone
- Establish botnet infection as a breach trigger in your incident response runbooks; multi-purpose botnet malware frequently exfiltrates data alongside DDoS participation, creating regulatory notification obligations
Conclusion
The dismantling of four major botnets and the recovery of 3 million compromised devices is a significant law enforcement achievement—but it is not a permanent solution. Botnet operators rebuild infrastructure, recruit new devices, and adapt their C2 architectures to survive future takedowns. The devices that fed these botnets are still out there, largely unsecured, waiting to be re-recruited.
For security teams, the lesson is not to rely on law enforcement action as a backstop. The lesson is to shrink your organization's attack surface—through IoT asset visibility, aggressive credential hygiene, network segmentation, and DNS-layer monitoring—so that your devices never become nodes in the next campaign. Coordinate with your ISP about upstream DDoS mitigation options and formalize your participation in relevant ISAC threat sharing communities. The defenders who contributed telemetry to this operation made it possible. Your organization can be part of that next success.
Frequently Asked Questions
Q: How can I tell if a device on my network is part of a botnet? A: Look for anomalous outbound traffic patterns in your NetFlow or firewall logs—unusual volumes, connections to unfamiliar geographies, or traffic on non-standard ports from devices that should only communicate with a narrow set of destinations. DNS-based filtering tools that log queries to known C2 domains will surface infected devices even when the traffic appears benign at the network layer.
Q: Are enterprise networks really at risk from consumer-grade botnets? A: Yes, in two distinct ways. First, enterprise environments often contain unmanaged IoT devices—IP cameras, building automation systems, smart TVs in conference rooms—that share the same vulnerabilities as consumer devices and can be recruited as botnet nodes. Second, enterprise services are frequent targets of botnet-driven DDoS attacks, making outbound device hygiene and inbound DDoS resilience equally important.
Q: What should I do if I discover a botnet-infected device on my network? A: Isolate the device from the network immediately to stop its participation in ongoing attacks, then preserve forensic evidence including traffic logs and any available device logs before remediation. Notify your legal and privacy teams to assess whether any data exfiltration occurred that could trigger GDPR, HIPAA, or other breach notification obligations, and consider reporting indicators of compromise to your sector ISAC or to CISA.
Q: Does patching alone protect IoT devices from botnet recruitment? A: Patching significantly reduces exploitation risk but is not sufficient on its own. Many botnet infections leverage default or weak credentials rather than software vulnerabilities, so credential hygiene is equally important. Network segmentation and egress filtering provide essential compensating controls for devices where patching is delayed or impossible due to end-of-life status.
Q: How do DDoS attacks from botnets differ from other DDoS attacks? A: Botnet-driven DDoS attacks use geographically distributed, residential IP addresses that bypass IP reputation and source-based blocking controls effectively. Unlike attacks from a single data center range, botnet traffic blends with legitimate user traffic at the network edge, making application-layer filtering and behavioral analysis—rather than simple volumetric thresholds—the necessary mitigation approach. Coordination with your upstream ISP for traffic scrubbing is often required to absorb large-scale botnet-driven attacks.
Enjoyed this article?
Subscribe for more cybersecurity insights.
