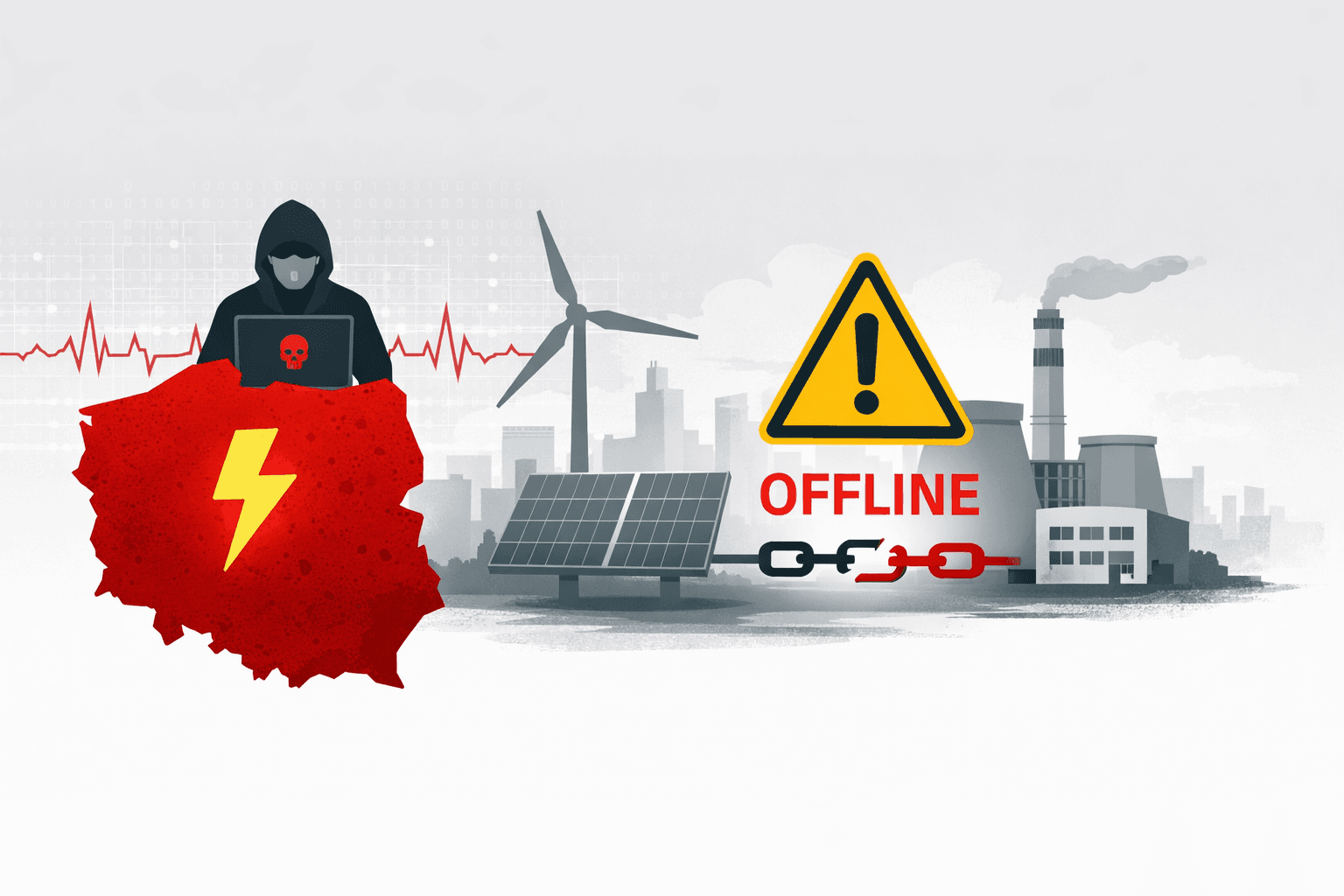
A coordinated cyberattack on Poland's energy infrastructure in late December 2024 compromised approximately 30 distributed energy resource (DER) sites, destroying operational equipment while narrowly avoiding power outages. The incident targeted combined heat and power plants alongside wind and solar dispatch systems, damaging critical operational technology (OT) beyond repair.
Despite affecting roughly 1.2 gigawatts of generation capacity—approximately 5% of Poland's total supply—the attack failed to trigger blackouts. However, cybersecurity researchers from Dragos warn that this outcome should serve as a critical wake-up call rather than reassurance. The breach exposed fundamental vulnerabilities in decentralized energy infrastructure that threat actors can exploit to devastating effect.
This analysis examines the technical details of the attack, the threat actor behind it, and the urgent security implications for energy operators worldwide managing distributed generation assets.
Understanding the Poland DER Attack Vector
Targeted Infrastructure Components
The attackers demonstrated sophisticated knowledge of distributed energy systems by simultaneously compromising multiple site types. The breach focused on three critical technology layers: remote terminal units (RTUs) managing field device communications, edge computing devices processing local operational data, and Windows-based supervisory control systems coordinating site operations.
Each compromised layer represented a deliberate escalation path, allowing attackers to move from initial access through monitoring systems to direct control over generation equipment.
Attack Methodology and Execution
Electrum, the Russian-linked threat actor attributed to this operation, employed tactics indicating extensive reconnaissance and operational planning. The group repeatedly compromised similar device configurations across geographically dispersed sites, suggesting exploitation of common vulnerabilities in standardized DER deployments.
Attack Timeline and Impact:
| Phase | Target Systems | Result | Operational Effect |
|---|---|---|---|
| Initial Compromise | Network perimeter devices | Persistent access established | Remote monitoring degraded |
| Lateral Movement | RTUs and edge devices | Configuration corruption | Loss of remote control capability |
| Destructive Phase | OT controllers and HMIs | Device firmware wiped | Physical equipment replacement required |
| Communication Severance | SCADA networks | Protocol disruption | Situational awareness eliminated |
The attackers successfully severed communications between remote facilities and central control centers while allowing local power generation to continue autonomously. This approach maximized operational disruption without triggering the immediate emergency response that widespread blackouts would have prompted.
Why Local Generation Continued Operating
Modern DER sites incorporate autonomous operation capabilities designed to maintain generation during communication failures. Local controllers continued managing turbine operations, solar inverter outputs, and thermal loads based on pre-programmed parameters. However, grid operators lost critical visibility into generation levels, equipment status, and the ability to dispatch or curtail output in response to grid conditions.
Pro Tip: Autonomous operation modes should include cryptographically verified health checks that detect tampering and transition sites to safe shutdown states when compromise indicators appear.
The Electrum Threat Actor Profile
Attribution and Capabilities
Dragos analysts attribute the Poland attack to Electrum with moderate confidence, distinguishing this group from the more widely known Sandworm/APT44 cluster despite apparent connections to Russian state interests. Electrum has demonstrated specialized expertise in energy sector operations, particularly understanding grid management principles, distributed resource coordination, and the industrial protocols controlling generation assets.
Tactical Evolution
Previous attacks linked to Russian-aligned threat actors include Industroyer/Industroyer2 (directly manipulated substation circuit breakers in Ukraine), DynoWiper (destructive malware targeting Ukrainian energy organizations), and Caddywiper (data destruction attacks). The Poland incident represents tactical evolution beyond these predecessors—rather than seeking immediate, visible disruption, Electrum focused on degrading operational capabilities while maintaining plausible deniability through the absence of immediate blackouts.
Comparison of Russian-Linked Energy Sector Attacks:
| Attack | Year | Target | Primary Goal | Visible Impact |
|---|---|---|---|---|
| Industroyer | 2016 | Ukrainian substations | Power disruption | 1-hour blackout |
| Industroyer2 | 2022 | Ukrainian distribution | Service denial | Prevented by defenders |
| DynoWiper | 2024 | Ukrainian energy org | Data destruction | IT systems offline |
| Poland DER | 2024 | Distributed generation | Capability degradation | No blackouts |
This "below-threshold" aggression complicates attribution and diplomatic response while achieving meaningful degradation of national critical infrastructure resilience.
Grid Stability Risks in Distributed Energy Systems
The Frequency Regulation Challenge
While the Poland attack avoided widespread outages, Dragos researchers emphasized that simultaneous loss of 1.2 GW could have triggered grid frequency instability. Modern electrical grids maintain precise frequency control through continuous balance between generation and consumption. Sudden generation loss forces grid operators to rapidly compensate through activating spinning reserves, implementing automated load shedding protocols, and adjusting interconnection flows.
The 2025 Iberian Peninsula grid collapse, referenced by Dragos as a concerning parallel, demonstrated how distributed generation failures can cascade into broader system instability.
Visibility and Control Dependencies
When attackers severed SCADA connectivity to compromised sites, operators lost real-time generation output monitoring, equipment health visibility, remote dispatch control, frequency response coordination, and voltage regulation capabilities. Grid operators managing modern power systems increasingly depend on visibility into thousands of distributed generation points. Attackers exploiting this centralized monitoring architecture can achieve disproportionate impact relative to the physical generation capacity affected.
Decentralization as Security Double-Edge
Security Trade-offs in DER Infrastructure:
| Factor | Centralized Generation | Distributed Generation |
|---|---|---|
| Attack Surface | Few large targets | Many small targets |
| Security Resources | Concentrated expertise | Dispersed capabilities |
| Physical Redundancy | Limited diversity | Geographic distribution |
| Monitoring Complexity | Centralized visibility | Multi-site coordination required |
The Poland attack exploited common vulnerabilities replicated across numerous sites, demonstrating how standardized DER deployments can enable scalable attack operations.
Critical Security Gaps Exposed
Remote Access and Perimeter Security
The successful compromise of 30 geographically distributed sites indicates fundamental weaknesses in remote access security architectures. Common vulnerabilities in DER remote access include default credentials on remote terminal units, unencrypted communication protocols, insufficient network segmentation between IT and OT, inadequate monitoring of privileged access activities, and missing multi-factor authentication on critical systems.
Important: Energy operators should implement zero-trust network architectures that verify every access request regardless of source, eliminating implicit trust in "internal" network connections.
Device Configuration Management
The attack's destructive phase corrupted or wiped device configurations so severely that physical replacement became necessary. Robust configuration management for operational technology requires automated cryptographically verified configuration backups, offline backup storage isolated from operational networks, regular restoration testing, change detection and alerting for unauthorized modifications, and hardware-based configuration protection.
Implementing Defense-in-Depth for DER Security
Network Architecture Hardening
Effective DER security begins with network segmentation that limits lateral movement and contains breaches. Each network boundary should implement defense-in-depth controls including firewalls with deny-by-default policies, intrusion detection systems trained on industrial protocols, and continuous monitoring for anomalous communication patterns.
Key zones include corporate IT networks separated from operations DMZ gateways, site OT networks with unidirectional gateways, control system layers with physical isolation where possible, and completely isolated safety systems with independent monitoring channels.
Operational Technology Security Fundamentals
Key OT security controls include:
- Application allowlisting on Windows-based control systems
- Read-only historian connections preventing data manipulation
- Hardware-enforced run-time integrity verification
- Secure remote access through isolated jump hosts
- Regular vulnerability scanning with production-aware scheduling
Detection and Response Capabilities
Critical detection capabilities for DER environments include asset inventory with unauthorized device alerting, protocol anomaly detection for industrial communications, behavioral analysis identifying unusual access patterns, configuration change monitoring with automatic rollback, and coordinated multi-site event correlation.
Supply Chain and Third-Party Risk
Many DER facilities depend on external vendors for equipment maintenance and remote monitoring services. Vendor security management should address contractual security requirements, regular security assessments, just-in-time access provisioning replacing persistent credentials, vendor activity monitoring, and independent verification of vendor-performed configuration changes.
Key Takeaways
- Distributed energy resources multiply attack surfaces - Decentralized generation creates numerous potentially vulnerable sites that attackers can compromise at scale using common vulnerabilities
- Communication layer attacks degrade situational awareness - Severing monitoring connections blinds operators to actual conditions even when physical generation continues
- Configuration destruction represents escalating threat tactics - Corrupting device firmware beyond recovery forces costly equipment replacement and extended restoration timelines
- Below-threshold attacks avoid triggering crisis response - Adversaries refine techniques that degrade capabilities without causing immediately visible disruptions
- Defense-in-depth architecture is essential - Network segmentation, configuration management, continuous monitoring, and vendor risk management must work together
Conclusion
The coordinated cyberattack on Poland's distributed energy infrastructure represents a concerning evolution in critical infrastructure targeting. By compromising 30 DER sites and destroying operational equipment while avoiding widespread blackouts, adversaries demonstrated sophisticated understanding of modern grid operations and the vulnerabilities introduced by decentralized generation architectures.
The incident should prompt energy operators worldwide to reassess security postures for distributed resources. The absence of power outages must not obscure the attack's significance—adversaries proved capable of coordinating multi-site compromises, degrading operational capabilities, and positioning themselves for potential future escalation.
Energy sector organizations must implement comprehensive security programs addressing the unique challenges of DER environments, including network segmentation, robust configuration management, enhanced visibility and detection capabilities, and rigorous vendor security management.
Frequently Asked Questions
Q: How did the attackers compromise 30 different sites without detection?
A: The attackers likely exploited common vulnerabilities in standardized equipment deployments, possibly including default credentials, unpatched systems, or weak remote access security. The coordinated timing suggests extensive reconnaissance and preparation before the destructive phase.
Q: Why didn't the attack cause blackouts if it affected 5% of Poland's generation capacity?
A: Modern DER sites include autonomous operation capabilities that maintain local generation during communication failures. While attackers severed monitoring and control connections, physical generation equipment continued running based on local controller programming, though operators lost critical visibility.
Q: What makes Electrum different from other Russian-linked threat actors like Sandworm?
A: While Electrum shows connections to Russian state interests, the group demonstrates distinct tactical preferences and specialized expertise in distributed energy systems. The Poland operation emphasized capability degradation rather than immediately visible disruption, complicating attribution and diplomatic response.
Q: Should small renewable energy sites implement the same security as large power plants?
A: While resource constraints differ, smaller DER sites face similar threats and require appropriate security controls scaled to their environment. Priority should focus on network segmentation, robust remote access security with multi-factor authentication, configuration backup and validation, and participation in sector-wide threat intelligence sharing.
Q: How can grid operators maintain visibility if attackers target communication systems?
A: Resilient architectures should include redundant communication paths using diverse technologies, out-of-band monitoring channels that can detect compromise of primary systems, and local storage of critical operational data. Organizations should establish procedures for operating with degraded visibility during communication disruptions.
Enjoyed this article?
Subscribe for more cybersecurity insights.
