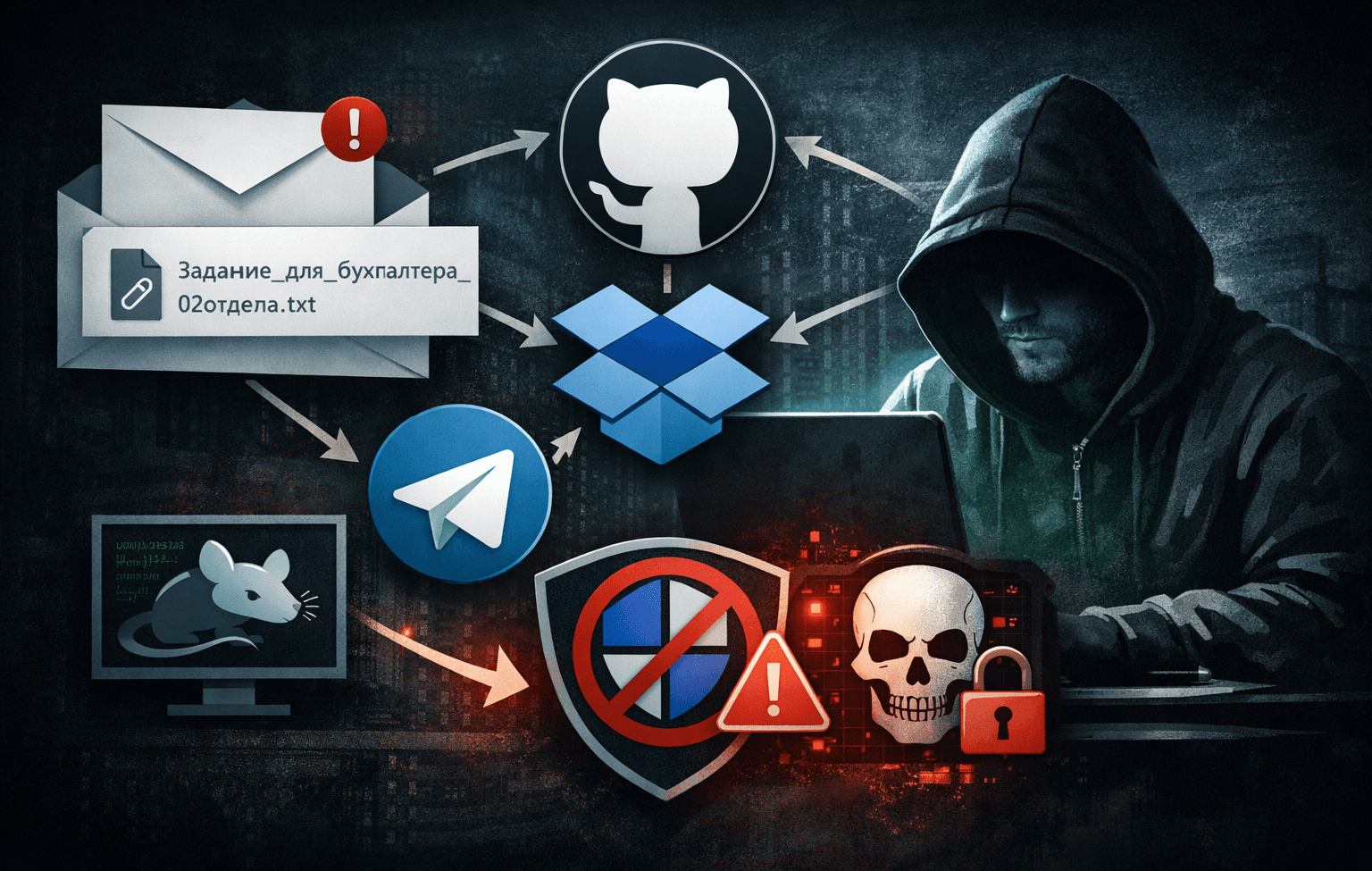
A sophisticated phishing campaign targeting Russian organizations has emerged, leveraging legitimate cloud platforms and security tool manipulation to deploy ransomware and information-stealing malware. This attack chain demonstrates how threat actors can achieve complete system compromise without exploiting a single software vulnerability.
The campaign, tracked under operations including UNG0902 and Paper Werewolf, specifically targets HR departments, payroll processors, and internal administrative teams. By abusing trusted services like GitHub, Dropbox, and Telegram, attackers bypass traditional security controls while maintaining operational stealth. This living-off-the-land approach represents a growing trend that every security professional must understand to protect their organization.
Understanding the Attack Chain
This multi-stage campaign orchestrates a carefully sequenced infection process that transforms a single click into full system compromise. The attackers demonstrate advanced knowledge of Windows security mechanisms and cloud service abuse techniques.
Initial Compromise Vector
The attack begins with highly targeted business-themed lures delivered in Russian language. Victims receive ZIP archives containing what appears to be legitimate documentation alongside a malicious LNK file disguised with a double extension technique.
The deceptive filename structure uses patterns like "Задание_для_бухгалтера_02отдела.txt.lnk" (Task_for_accountant_02department.txt.lnk). Windows' default behavior of hiding known extensions means victims see only "Задание_для_бухгалтера_02отдела.txt", creating the illusion of a harmless text document. This social engineering tactic exploits user trust in familiar file types.
Cloud Infrastructure Abuse
Rather than maintaining traditional command-and-control infrastructure, attackers leverage legitimate cloud platforms:
Table: Cloud Services Exploitation Matrix
| Platform | Role in Attack | Detection Challenge |
|---|---|---|
| GitHub | Hosts PowerShell scripts and .NET modules | Legitimate developer platform traffic |
| Dropbox | Stores final payloads (Amnesia RAT, ransomware) | Standard file sharing service |
| Telegram Bot API | Command-and-control and data exfiltration | Encrypted messaging platform |
This infrastructure approach offers attackers significant advantages. Security tools typically whitelist these platforms, making malicious traffic blend with normal business operations. Network monitoring solutions struggle to distinguish attack traffic from legitimate cloud service usage.
Script Execution Cascade
Once the malicious LNK executes, it triggers a PowerShell and Visual Basic script cascade. These scripts fetch additional components from GitHub repositories, establishing persistence mechanisms while maintaining a low detection profile.
The scripts perform reconnaissance, identify security solutions, and prepare the environment for payload deployment. Each stage retrieves only the next component needed, limiting forensic evidence if discovered prematurely.
Neutralizing Microsoft Defender
A critical component of this campaign involves completely disabling Microsoft Defender through multiple complementary techniques. This demonstrates how attackers can render endpoint protection ineffective without exploiting vulnerabilities.
The Defendnot Tool
Attackers deploy a specialized tool called "defendnot" designed specifically to disable Windows security features. This utility manipulates Windows Security Center APIs and Defender configurations through legitimate administrative interfaces.
The tool operates by:
- Presenting fake UAC (User Account Control) prompts to obtain elevated privileges
- Modifying Registry policies that control Defender behavior
- Creating broad exclusion rules that prevent scanning of attacker-controlled locations
- Disabling real-time protection and cloud-delivered protection features
Registry Tampering and Policy Manipulation
Beyond defendnot, the attack modifies specific Registry keys that govern security policy enforcement. These changes persist across reboots and resist casual remediation attempts.
Important: Tamper Protection, when enabled, prevents unauthorized modification of these critical Registry locations. Organizations running Defender without Tamper Protection remain vulnerable to this technique.
UAC Exploitation for Privilege Escalation
The campaign leverages social engineering to overcome User Account Control protections. Fake UAC prompts mimic legitimate Windows dialogs, tricking users into granting administrative privileges.
These prompts appear contextually appropriate—often claiming to be required for document viewing or system updates. The psychological manipulation makes even security-aware users susceptible to approval.
Deployed Malware Payloads
Following successful security neutralization, attackers deploy two primary malware families that work in tandem to maximize impact and profit.
Amnesia RAT Capabilities
The Amnesia Remote Access Trojan, delivered as "svchost.scr", provides comprehensive system control. This information stealer targets multiple data types simultaneously.
Primary theft objectives include:
- Browser-stored credentials and autofill data across all major browsers
- Cryptocurrency wallet files and private keys
- Active session tokens for email and cloud services
- Browser cookies enabling account access without passwords
- Screenshots and keylogger data for sensitive information capture
Amnesia RAT maintains persistence through multiple mechanisms and establishes bidirectional communication with operators. The malware can download and execute additional payloads, enabling campaign evolution without reinfection.
Hakuna Matata Ransomware Variant
The ransomware component shares characteristics with the Hakuna Matata malware family. This dual-purpose payload combines traditional encryption with additional monetization techniques.
Table: Ransomware Functionality Breakdown
| Function | Target | Impact |
|---|---|---|
| File encryption | Documents, media, source code | Data unavailability and ransom pressure |
| Process termination | Antivirus, backup, database services | Prevents interference and maximizes damage |
| Clipboard hijacking | Cryptocurrency wallet addresses | Redirects victim transactions to attacker wallets |
| Screen locking | Windows desktop access | Forces ransom note visibility |
The process termination component specifically targets services that might interfere with encryption or allow recovery. Database services, backup agents, and competing malware all face termination before the encryption phase begins.
Clipboard Hijacking Mechanism
An innovative monetization technique monitors the system clipboard for cryptocurrency wallet addresses. When detected, the malware substitutes the attacker's wallet address seamlessly.
Victims attempting cryptocurrency transactions unknowingly send funds directly to attackers. This technique operates independently of the ransomware component, providing additional revenue even if victims refuse to pay ransoms.
Detection and Prevention Strategies
Organizations can implement multiple defensive layers to detect and prevent this attack pattern, despite its sophisticated evasion techniques.
Monitoring Security Feature Tampering
Microsoft recommends monitoring specific indicators of Defender manipulation. Security teams should alert on:
- Unexpected modifications to Windows Defender Registry keys
- Sudden creation of broad scanning exclusions
- Disablement of real-time protection outside maintenance windows
- Windows Security Center API calls from unexpected processes
- Repeated UAC prompts requesting security-related permissions
Pro Tip: Enable Windows Event Logging for security policy changes and correlate these events with process creation logs to identify tamper attempts.
Network Traffic Analysis
Despite using legitimate cloud services, this attack generates detectable traffic patterns. Security operations should monitor for:
Table: Suspicious Traffic Indicators
| Indicator | Description | Priority |
|---|---|---|
| GitHub raw content downloads | PowerShell fetching scripts from repositories | High |
| Dropbox API usage from scripting engines | Automated file retrieval patterns | High |
| Telegram Bot API traffic | Unusual messaging patterns from endpoints | Critical |
| Sequential cloud service connections | Single process accessing multiple platforms | Medium |
Implementing SSL/TLS inspection for cloud traffic enables deeper analysis, though this requires careful policy management to respect privacy and compliance requirements.
Endpoint Hardening Measures
Technical controls can significantly raise attacker costs and success difficulty:
- Enable Tamper Protection on all Windows endpoints to prevent Defender manipulation
- Configure Attack Surface Reduction rules to block script execution from suspicious locations
- Implement application whitelisting to control which executables can run
- Disable PowerShell for users who don't require it operationally
- Show file extensions for known file types to expose double-extension tricks
- Enforce least-privilege access to minimize UAC prompt effectiveness
User Security Awareness Training
Technical controls require human reinforcement through targeted training programs. Focus education on:
- Double-extension file recognition and the risks of LNK files
- Scrutinizing UAC prompts for legitimacy and appropriate context
- Verifying sender authenticity before opening attachments
- Reporting suspicious files through established channels
- Understanding that legitimate documents rarely require administrative privileges
Training should include simulated phishing exercises using similar Russian-language lures and business themes to test and reinforce awareness.
Threat Intelligence and Attribution
While specific attribution remains complex, the targeting patterns and tool selection reveal strategic campaign planning focused on Russian-speaking organizations.
Campaign Tracking Identifiers
Security researchers track this activity under multiple designations including UNG0902, Operation DupeHike, and Paper Werewolf. These identifiers help organizations correlate internal detections with external intelligence.
The focus on HR and payroll departments suggests attackers seek either financial fraud opportunities or access to sensitive employee data for subsequent attacks. Administrative teams provide broad network access useful for lateral movement.
Living-Off-the-Land Techniques
The complete absence of software vulnerability exploitation distinguishes this campaign. Attackers achieve all objectives through:
- Legitimate Windows utilities and scripting engines
- Authorized cloud services used outside intended purposes
- Social engineering rather than technical exploitation
- Security feature abuse instead of security feature bypass
This approach complicates detection because every tool and technique appears legitimate in isolation. Only behavioral analysis and pattern recognition reveal malicious intent.
Key Takeaways
- Multi-stage phishing campaigns can achieve complete compromise without exploiting vulnerabilities through security feature manipulation and cloud service abuse
- Enabling Tamper Protection is critical to preventing defendnot-style attacks that disable Microsoft Defender through Registry and policy manipulation
- Double-extension LNK files remain effective social engineering vectors that bypass user suspicion by hiding malicious file types
- Monitoring unusual cloud service access patterns from scripting engines provides early warning of living-off-the-land attacks
- Combining technical controls with targeted security awareness training creates overlapping defensive layers against sophisticated phishing campaigns
- Living-off-the-land techniques will continue increasing as defenders improve vulnerability management and patch deployment practices
Conclusion
This Russian-focused phishing campaign exemplifies the evolution of cyber threats toward security feature abuse rather than vulnerability exploitation. By leveraging trusted cloud platforms and legitimate Windows functionality, attackers demonstrate that even fully patched systems remain vulnerable to sophisticated social engineering and configuration manipulation.
Security professionals must shift defensive strategies to address this reality. Technical controls like Tamper Protection, behavioral monitoring, and attack surface reduction complement rather than replace user awareness training. Organizations should implement defense-in-depth approaches that assume some technical controls will fail and prepare backup detection mechanisms.
The most effective defense combines technical hardening with organizational vigilance. Regular security assessments should specifically test resistance to living-off-the-land techniques and security feature tampering. By understanding attacker methodologies, security teams can build resilient defenses that protect against current threats while adapting to future campaign evolution.
Frequently Asked Questions
Q: Can this attack succeed against systems with Tamper Protection enabled?
A: Tamper Protection significantly increases attack difficulty by preventing defendnot from disabling Microsoft Defender through Registry modifications. However, attackers might still succeed if users grant administrative privileges through social engineering, making user awareness training equally important alongside technical controls.
Q: How can organizations detect if defendnot has already compromised their endpoints?
A: Check for unexpected Microsoft Defender exclusions, disabled real-time protection, and suspicious Registry modifications under HKLM\SOFTWARE\Policies\Microsoft\Windows Defender. Review Windows Event Logs for security policy changes and correlate with process execution logs to identify tamper attempts. Immediate remediation requires removing exclusions and re-enabling protection features.
Q: Why do attackers prefer cloud services over traditional command-and-control infrastructure?
A: Legitimate cloud platforms provide built-in redundancy, global availability, and SSL/TLS encryption while security tools typically whitelist these services. This makes attacker traffic blend with normal business operations, complicating detection and attribution while reducing infrastructure costs and operational complexity for threat actors.
Q: What makes LNK files with double extensions effective despite being a known technique?
A: Windows default configuration hides file extensions for known types, making "document.txt.lnk" appear as "document.txt" to users. Combined with legitimate-looking icons and business-themed naming, victims perceive harmless documents. This technique exploits operating system behavior rather than user ignorance, remaining effective even against security-aware individuals.
Q: Should organizations block access to GitHub, Dropbox, and Telegram to prevent this attack?
A: Blanket blocking creates significant operational disruption for legitimate business functions and developer workflows. Instead, implement conditional access policies, monitor unusual usage patterns from scripting engines, and employ SSL/TLS inspection where appropriate. Focus on detecting behavioral anomalies rather than blocking entire platforms that serve legitimate business purposes.
Enjoyed this article?
Subscribe for more cybersecurity insights.
