
Ransomware Forensics 2026: Reconstructing the Attacker's Full Kill Chain
The average ransomware attacker dwells inside your network for 23 days before triggering encryption. In a typical 2025...
Stay ahead of cyber threats with expert insights, breaking news, and practical guides tailored specifically for the Cyber Security landscape.
Join 5,000+ subscribers. No spam, unsubscribe anytime.
Deep dives into the latest security trends. (173 articles)

The average ransomware attacker dwells inside your network for 23 days before triggering encryption. In a typical 2025...
A firewall is the digital equivalent of a security guard at a building's entrance — it decides who gets in and who gets...
Imagine buying a sealed jar of peanut butter from a supermarket you trust completely — only to discover the factory tha...
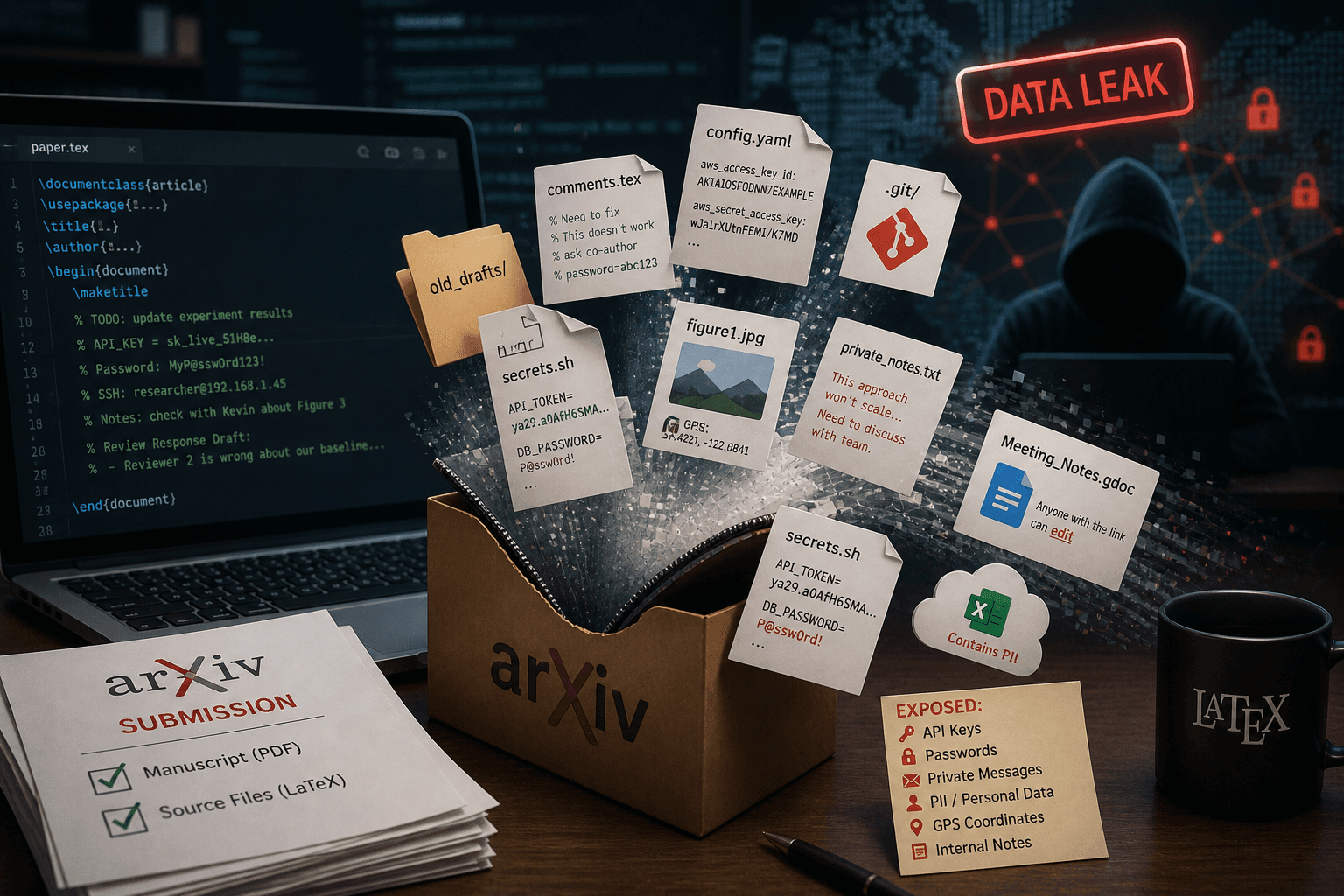
When researchers write academic papers, they often use a formatting system called LaTeX — think of it like a word proce...
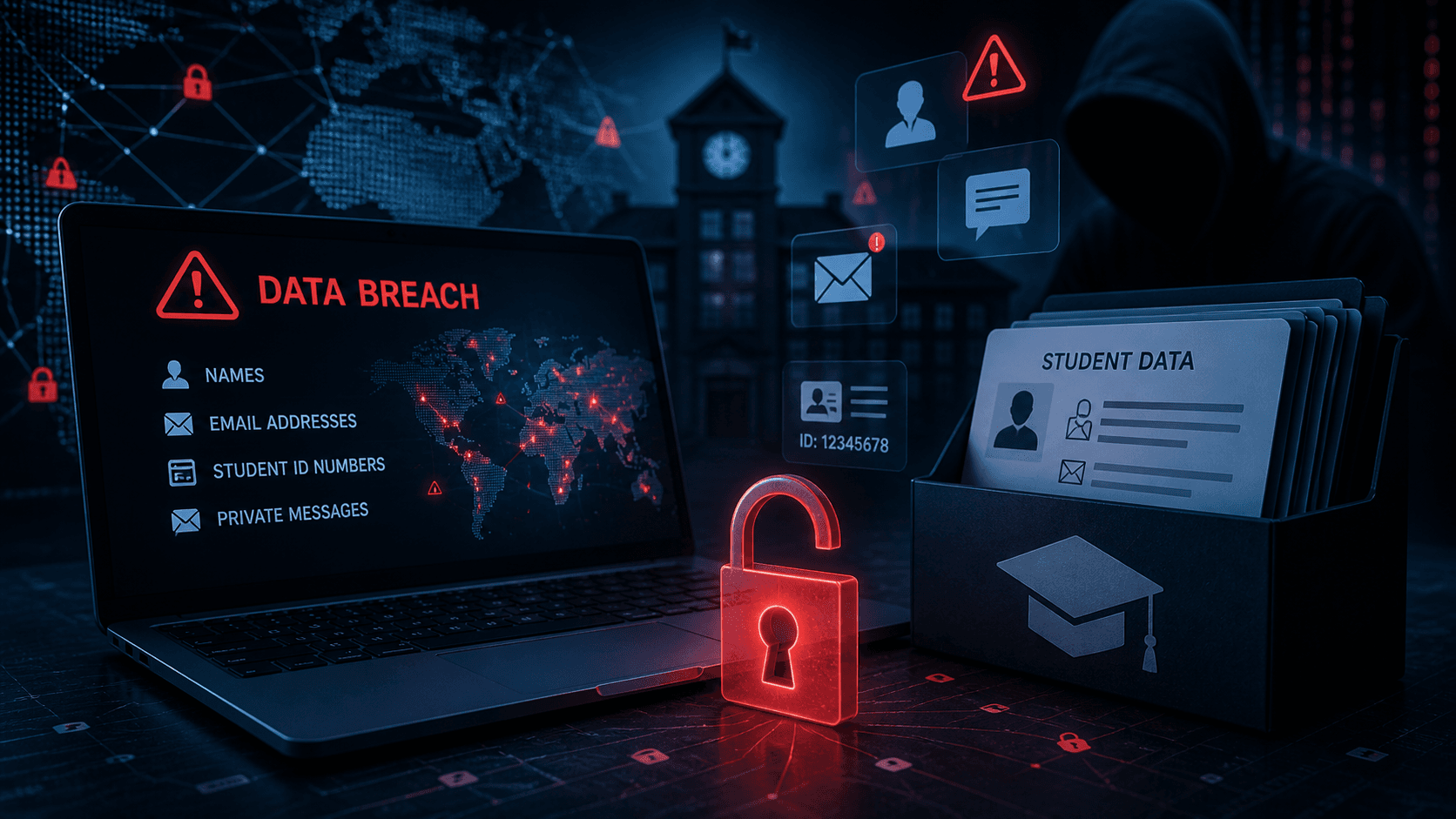
Schools and universities rely on centralized digital platforms to store student names, email addresses, IDs, and private...
Cryptocurrency was supposed to be anonymous. It isn't — and that distinction is reshaping financial crime investigatio...
Imagine receiving an official-looking email from your bank — but it's actually a scammer pretending to be your bank. Tha...
Imagine you hired a super-smart assistant to help you build a house. You gave them a master key to your entire property...

In January 2024, an AI-generated robocall mimicking President Biden's voice instructed New Hampshire voters to stay home...

In October 2023, a murder investigation in the United States turned on data recovered from a smart thermostat — times...
Imagine you send a letter to a post office, and inside the envelope you secretly include a note that says "ignore all...

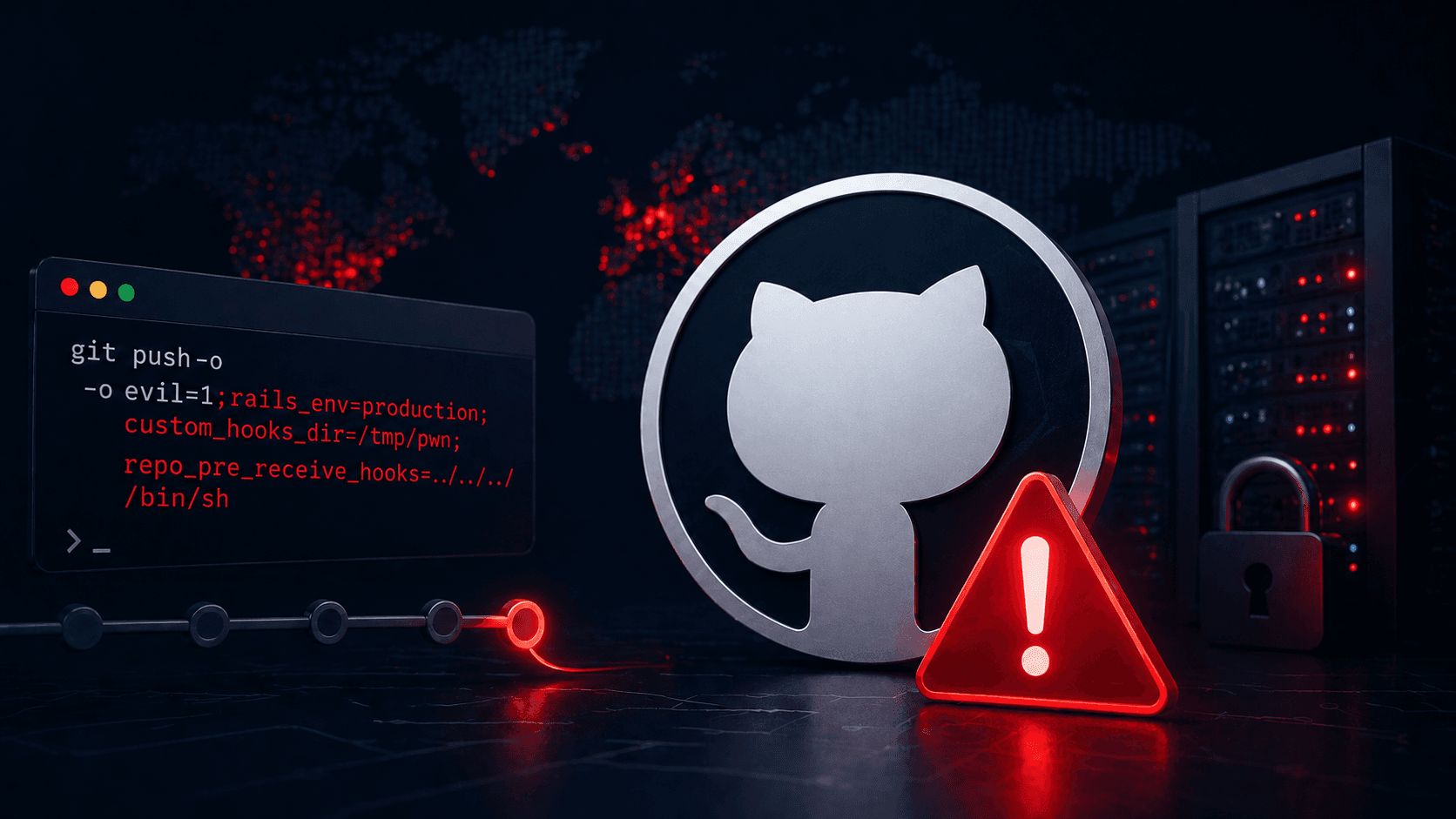
🔰 What is a Privilege Escalation Vulnerability? Imagine your office building has a security guard (a software progra...