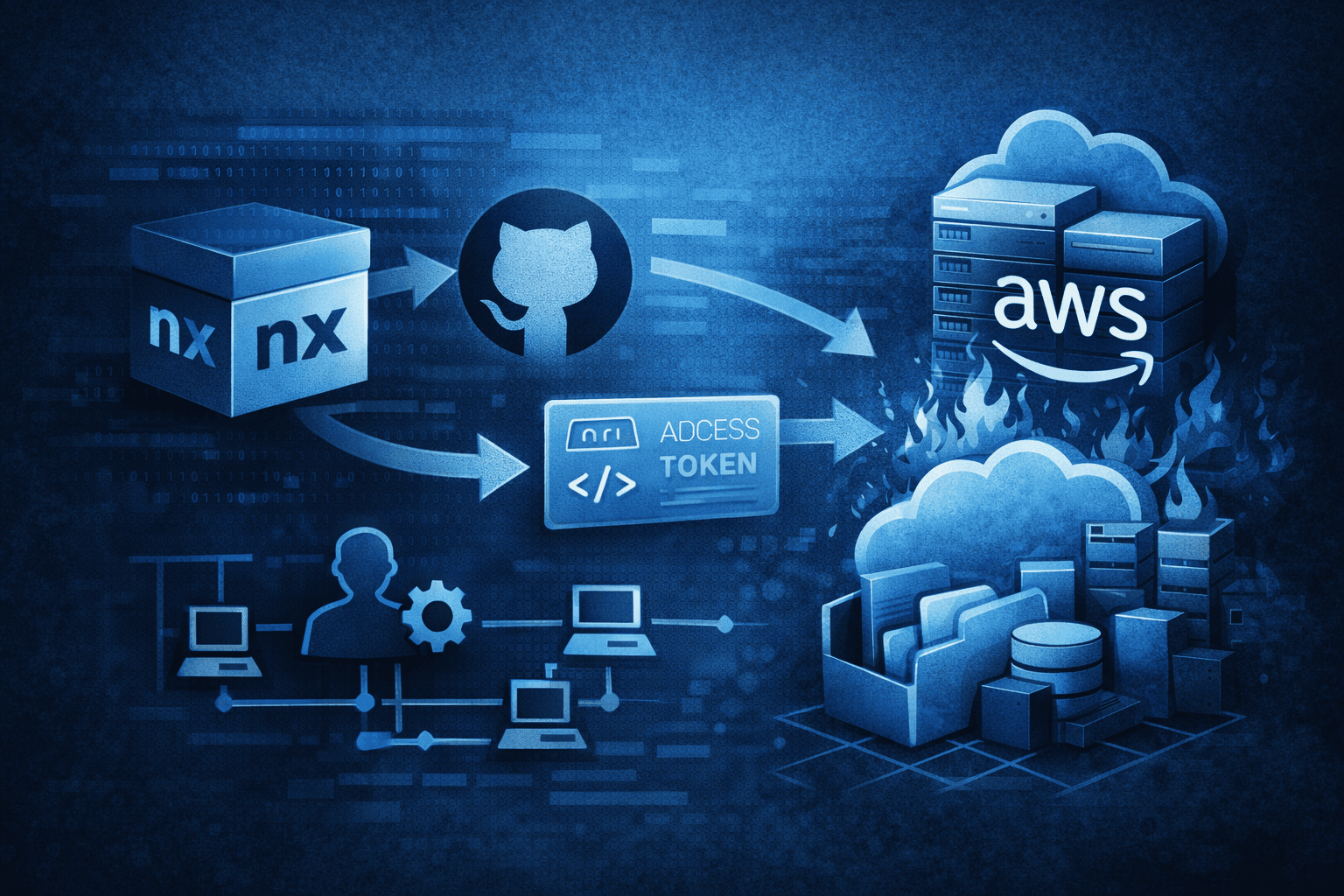
Supply Chain to Cloud Takeover: The nx npm Package Breach
A single stolen token. Seventy-two hours. Complete cloud destruction. That is the timeline threat actor UNC6426 achieved...
Stay ahead of cyber threats with expert insights, breaking news, and practical guides tailored specifically for the Cyber Security landscape.
Join 5,000+ subscribers. No spam, unsubscribe anytime.
Deep dives into the latest security trends. (121 articles)
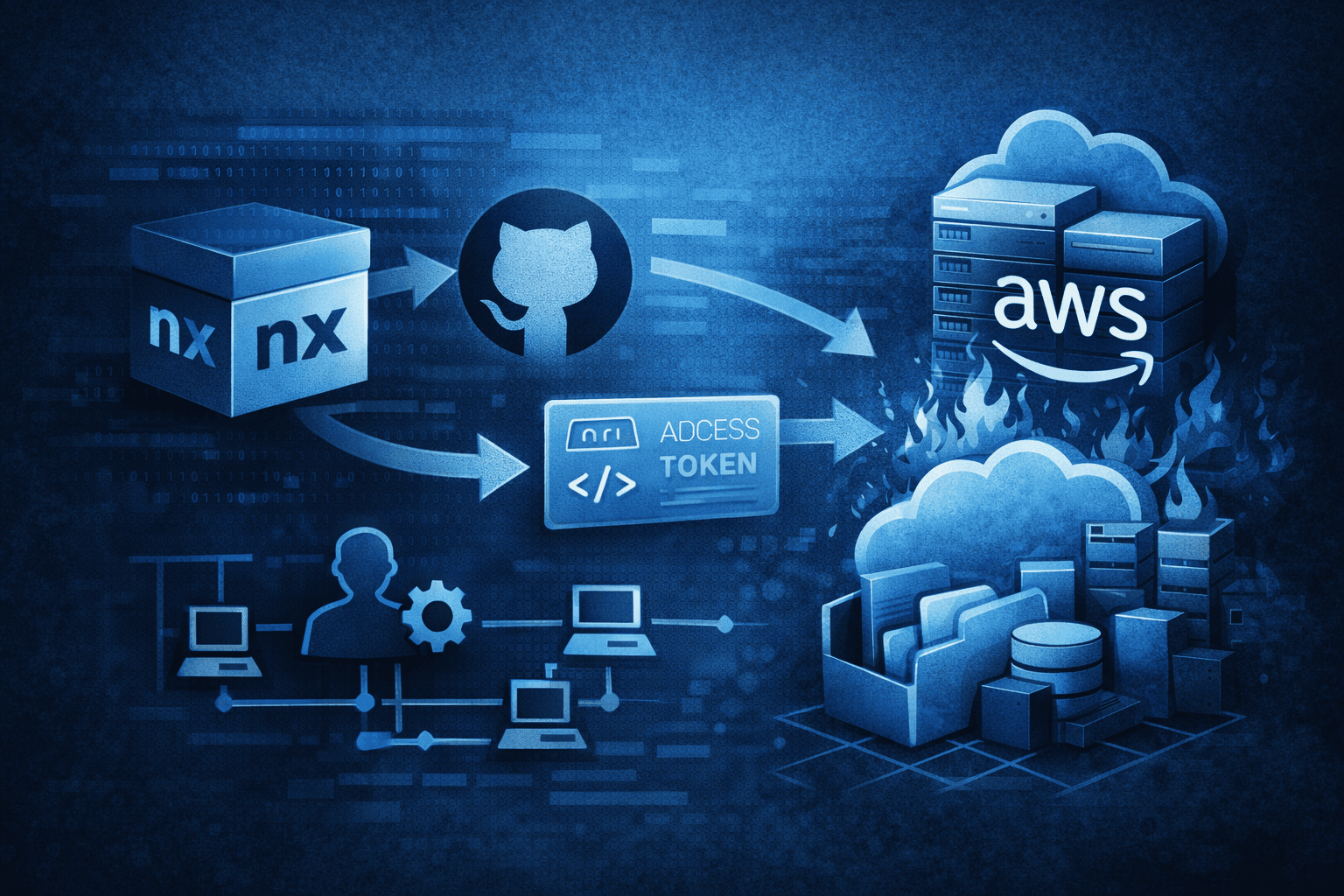
A single stolen token. Seventy-two hours. Complete cloud destruction. That is the timeline threat actor UNC6426 achieved...
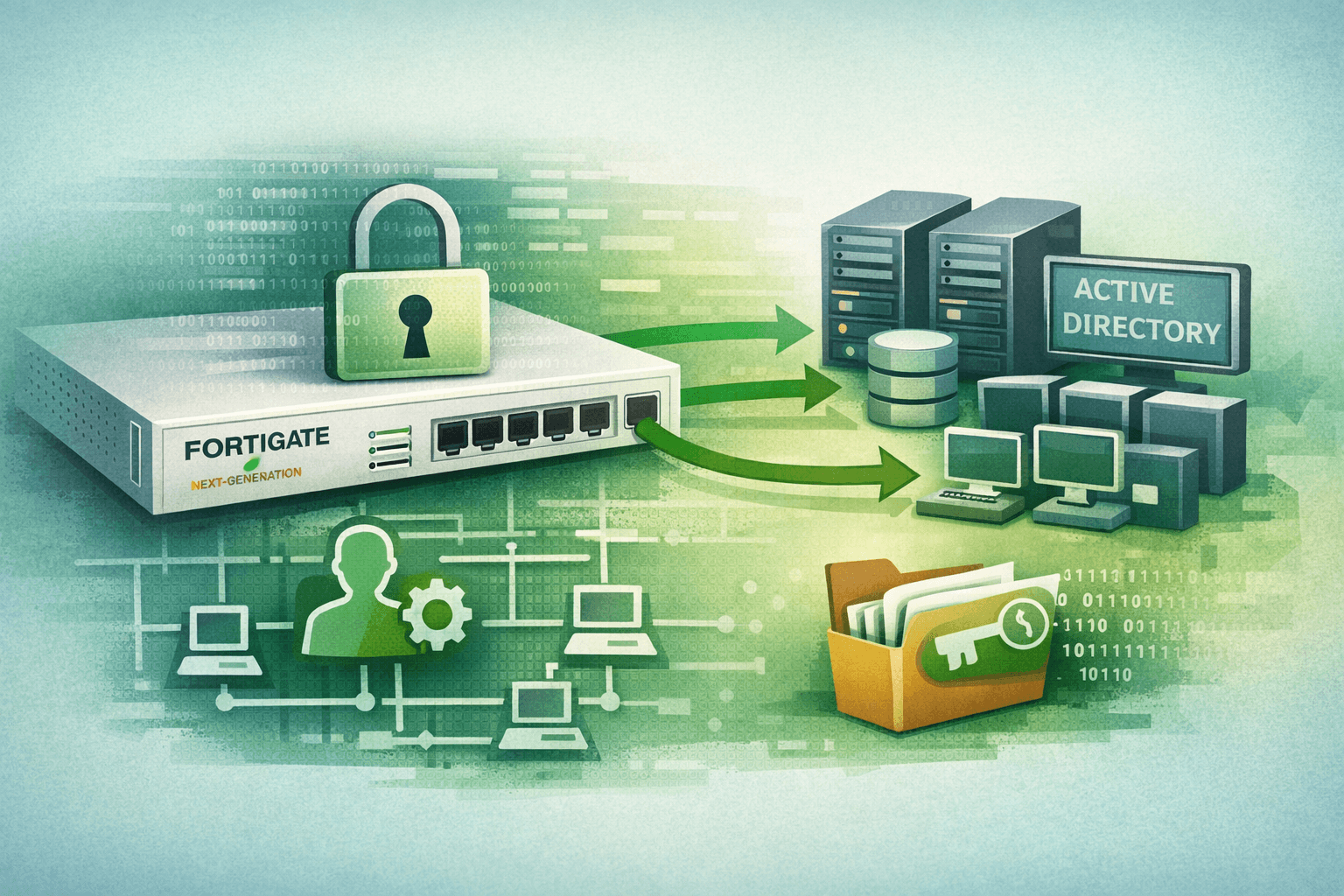
In late 2025, a threat actor quietly created a local admin account on a FortiGate next-generation firewall (NGFW) — and...
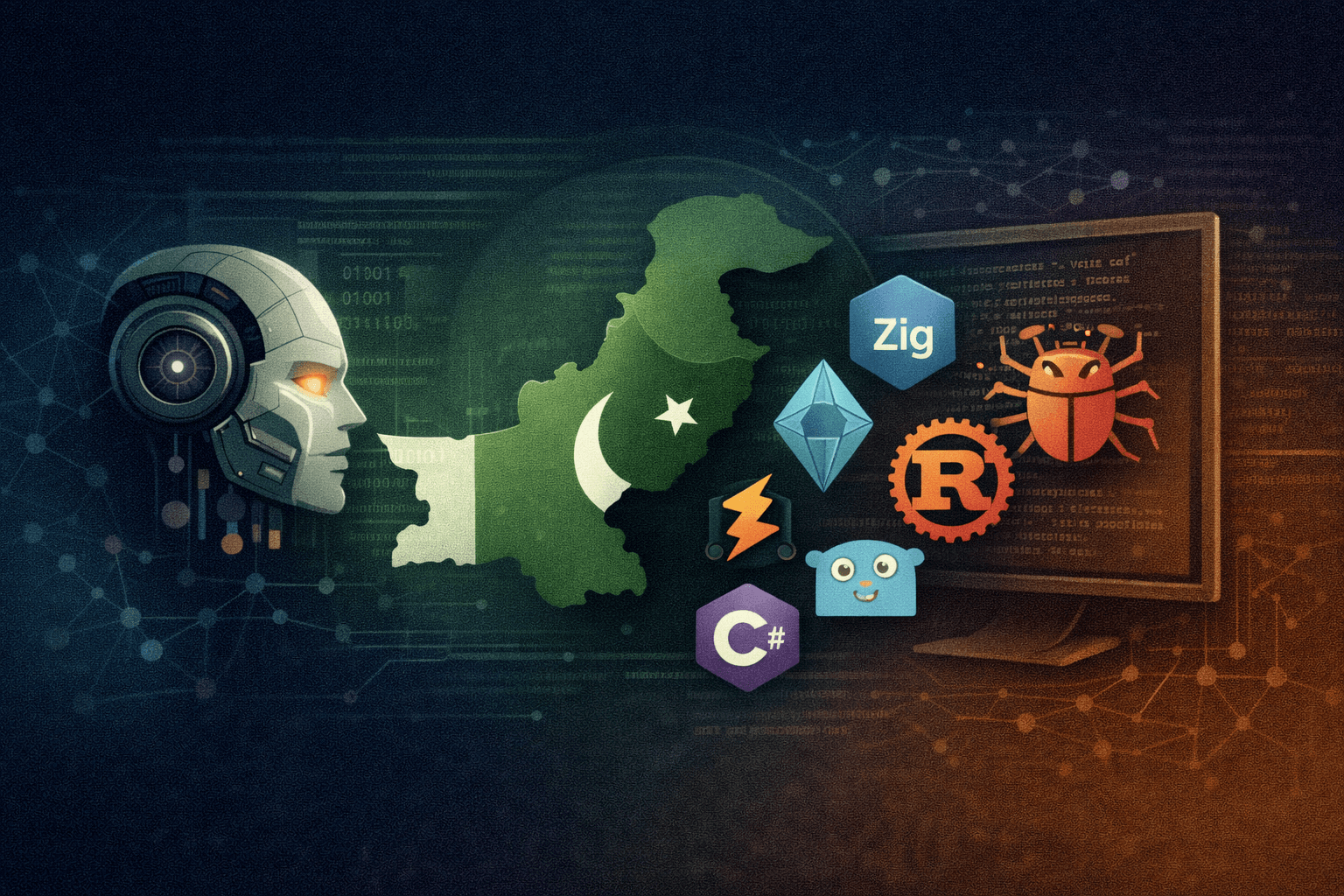
State-linked threat actors have crossed a threshold. Pakistan-affiliated Transparent Tribe (also tracked as APT36) is n...

A single AI model. One major browser. Twenty-two security vulnerabilities — 14 rated high severity — discovered before a...
Generative AI has changed the math for attackers. According to Microsoft Threat Intelligence (2025), adversaries now dep...
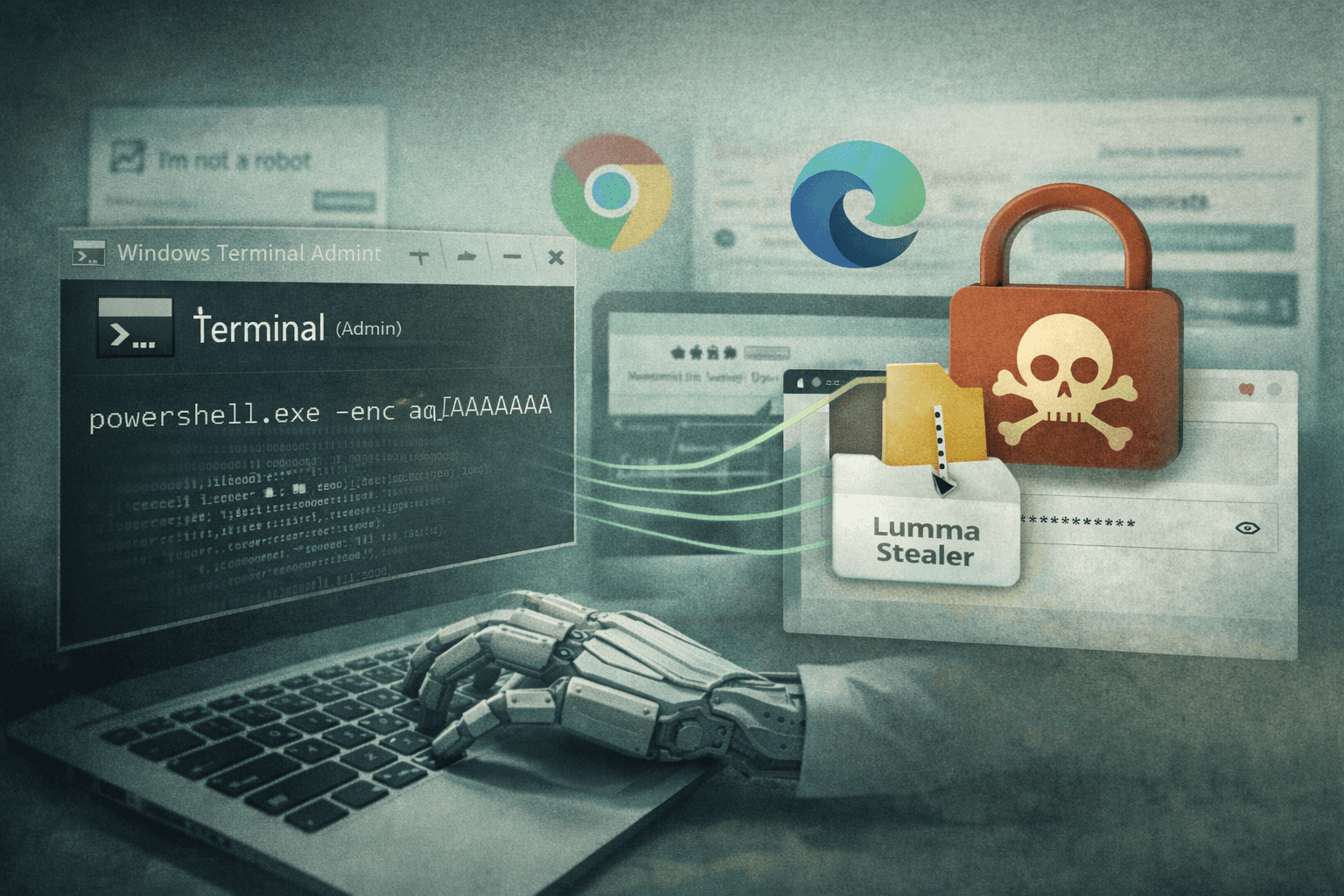
A new wave of credential theft attacks is exploiting one of the most trusted tools on your desktop. Since February 2026,...
In October 2024, security researchers uncovered a disturbing evolution in state-sponsored cyberattacks. A Pakistan-linke...
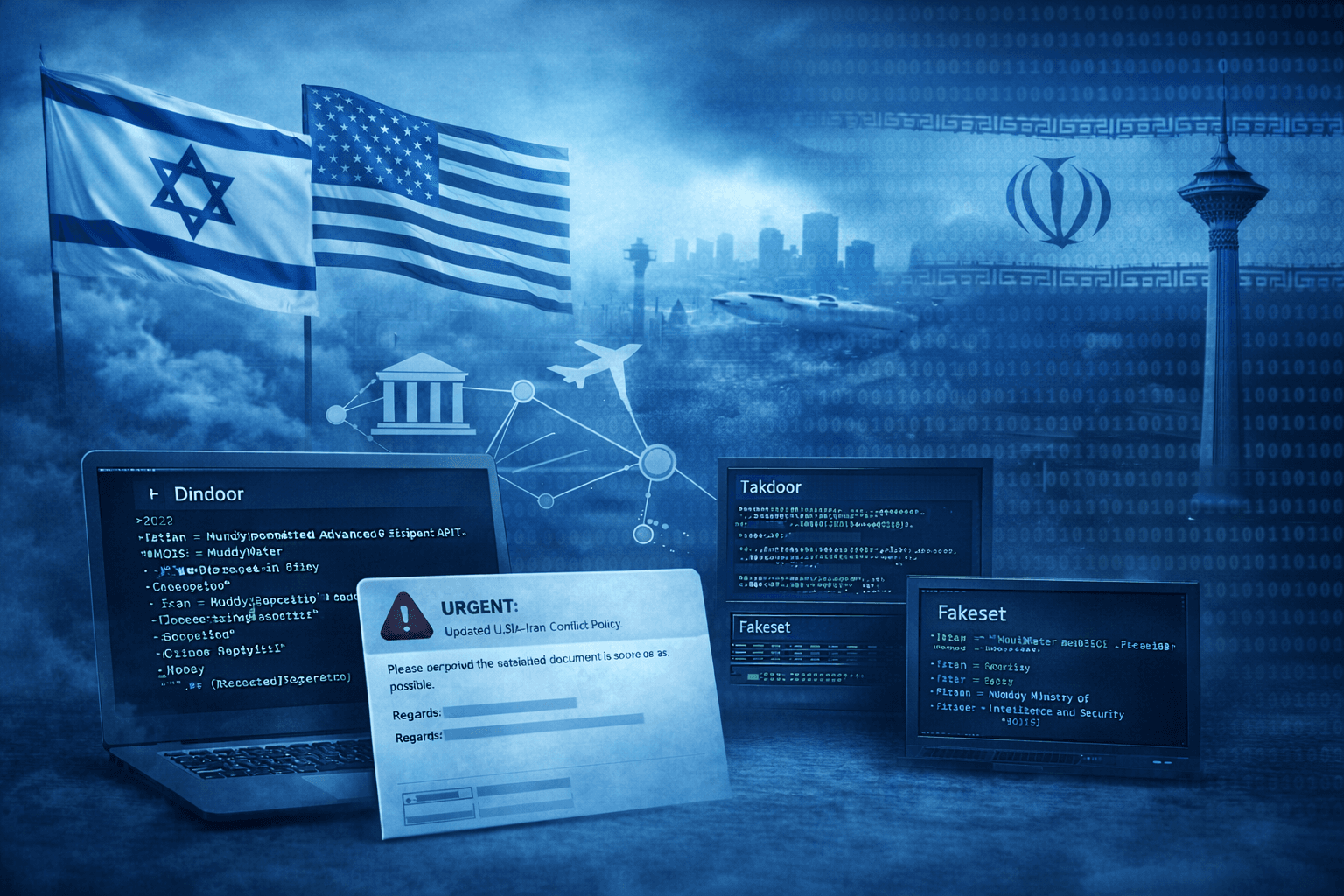
The geopolitical aftershocks of U.S. and Israeli military strikes on Iran are now reverberating through corporate networ...
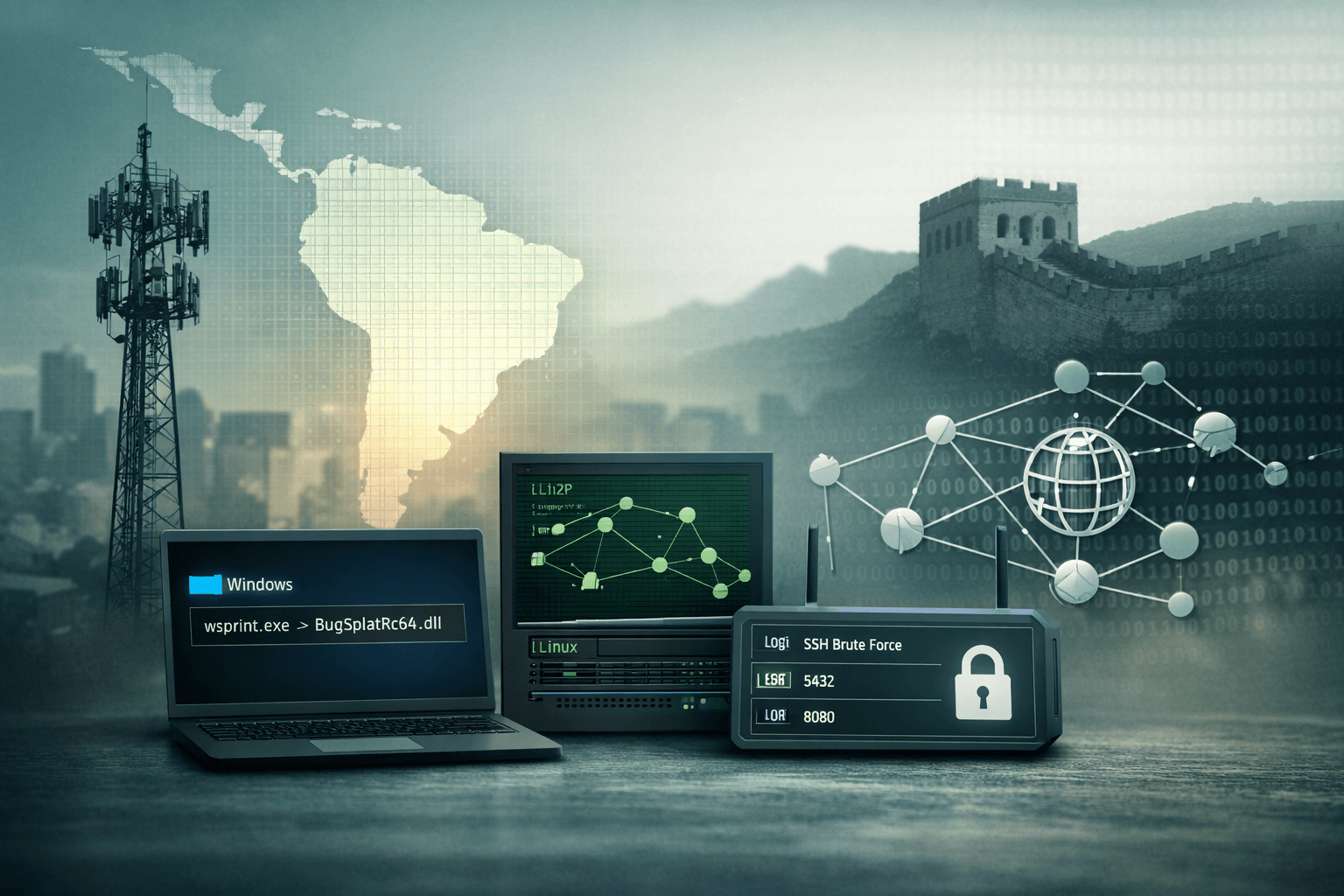
A state-sponsored threat actor has been systematically dismantling South American telecommunications infrastructure — an...

A new wave of phishing campaigns is exploiting browser technology most users have never heard of — and the results are d...
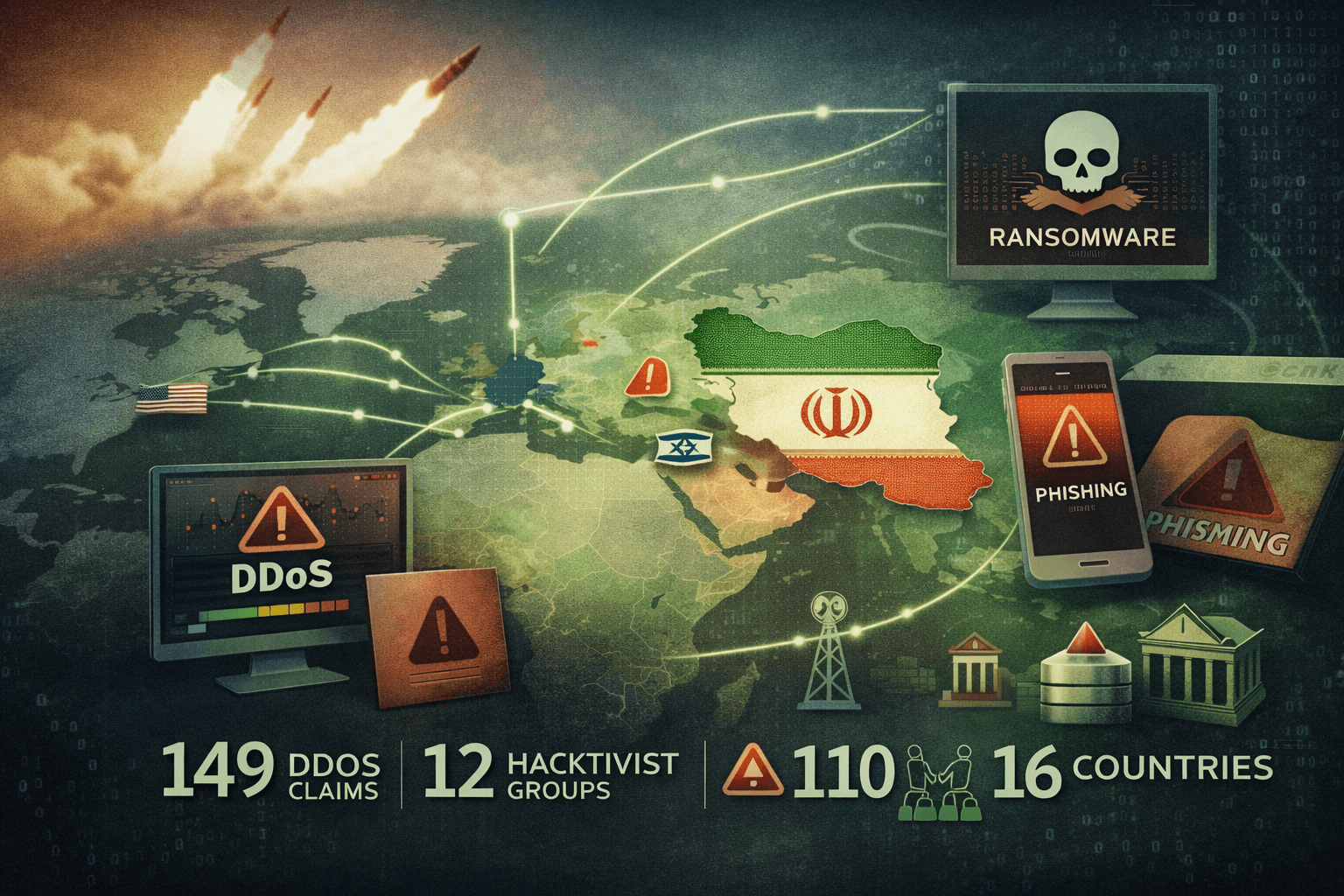
When missiles strike, keyboards follow. Within hours of U.S. and Israeli military operations against Iran—codenamed Epic...
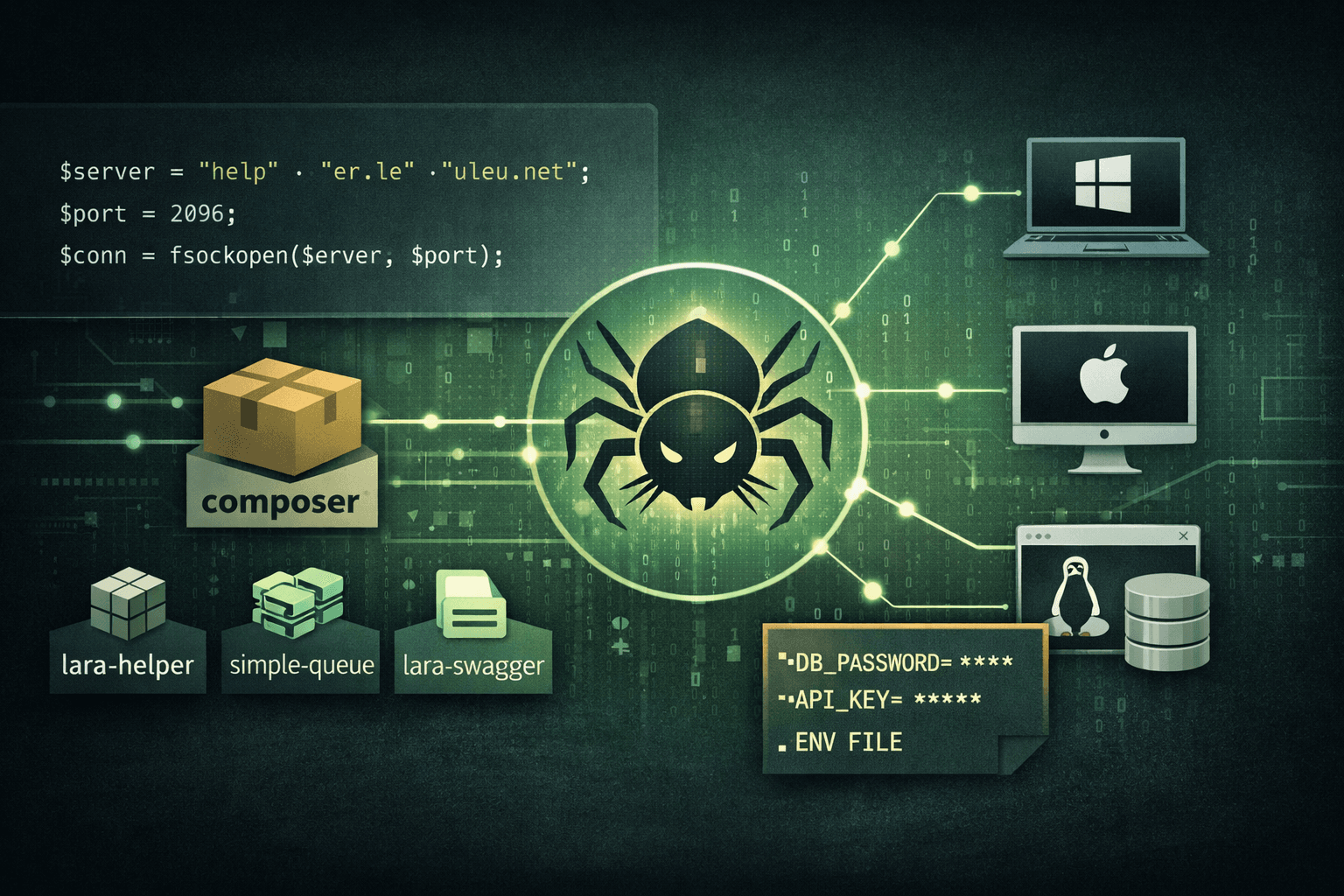
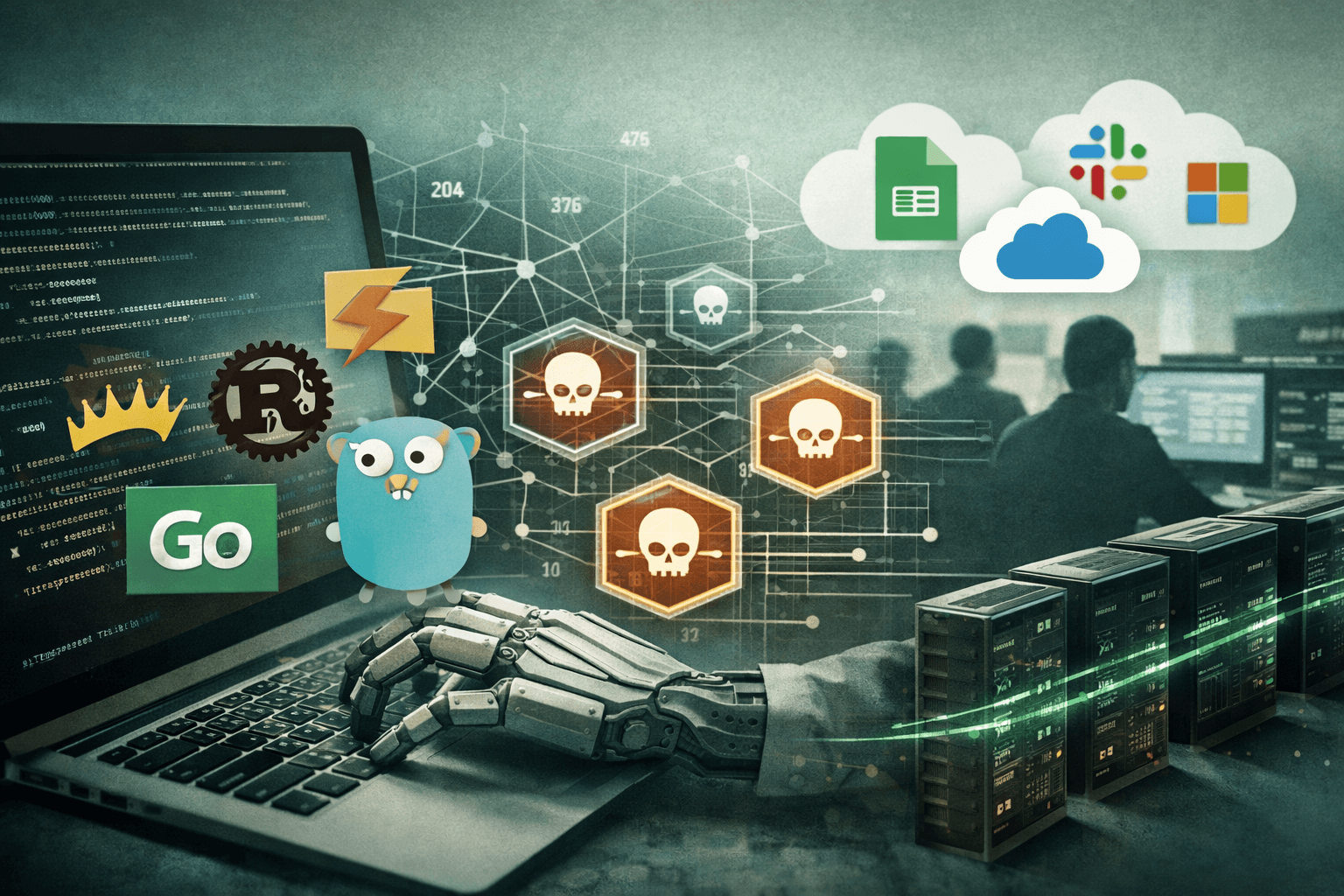
Supply chain attacks are no longer just an npm problem. Security researchers in 2025 identified three malicious Packagis...