Windows 11 April 2026 Update: BitLocker Lockouts and How to Stay Safe
A single mandatory update shouldn't lock you out of your own computer. Yet that is exactly what thousands of Windows 11...
Stay ahead of cyber threats with expert insights, breaking news, and practical guides tailored specifically for the Cyber Security landscape.
Join 5,000+ subscribers. No spam, unsubscribe anytime.
Deep dives into the latest security trends. (173 articles)
A single mandatory update shouldn't lock you out of your own computer. Yet that is exactly what thousands of Windows 11...
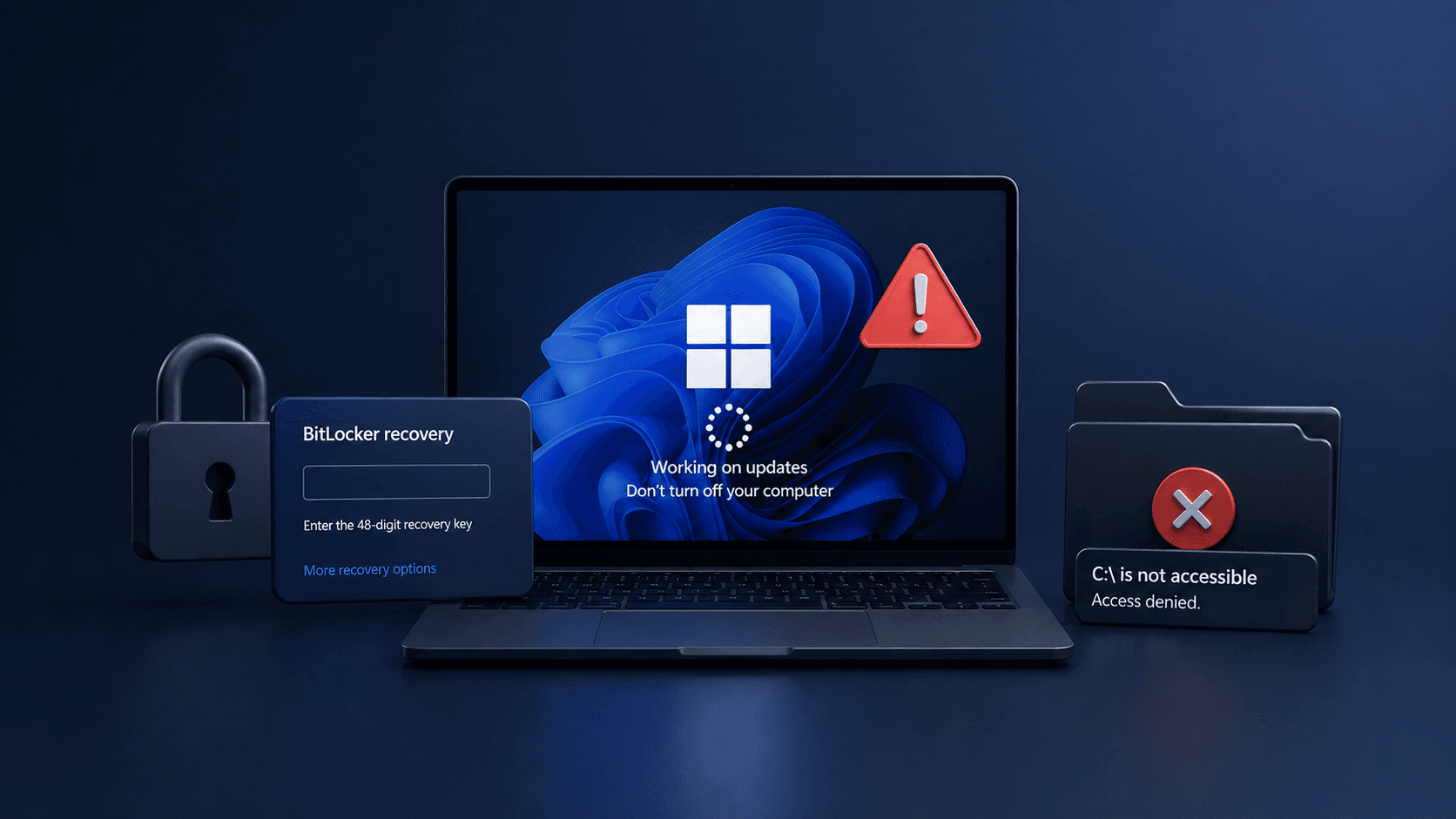
The assumption that multi-factor authentication makes an account impenetrable has cost organizations dearly. In early 20...
Cloud research environments are prime targets — they combine privileged IAM roles, sensitive datasets, and often-overloo...
In April 2026, attackers infiltrated the Slack workspace of the TODO Group — a Linux Foundation working group for open s...

In April 2025, Microsoft's threat research team quietly began a responsible disclosure process that would culminate in o...

In December 2025, threat researchers confirmed that attackers had been silently exploiting an unpatched vulnerability in...
In early 2025, BeyondTrust Phantom Labs disclosed a vulnerability that should have shaken every organization relying on...
In March 2025, a mid-sized U.S. healthcare network received a ransom note before its security team had even opened a sin...
A penetration tester at a financial services firm flags an anomaly in early 2026: a browser extension installed silentl...

A government agency's SOC analyst opens a routine alert in January 2026: a wave of emails impersonating DocuSign and Mi...

In late January 2026, a malicious LNK file quietly appeared on VirusTotal. By the time analysts traced it back to APT28...
In mid-2024, a phishing campaign began circulating that looked, at first glance, like a routine Google security alert....